Table of Contents
ToggleYes — Chrome extensions can download most “protected” videos. When a video plays in a browser, the media stream is technically accessible at the network level, regardless of right-click locks, iframe embeds, or basic token authentication. The only protection that reliably blocks browser-based download tools is multi-layer DRM encryption (such as Widevine or PlayReady) combined with dynamic watermarking. Platforms that rely solely on surface-level restrictions give creators a false sense of security.
You spent months building your course. You uploaded your videos, locked them behind a paywall, disabled right-click, and told yourself the content was safe. Then someone sent you a link — your own video, uploaded to a public site, freely available to anyone.
This is not a rare scenario. It is happening to course creators, media publishers, and enterprise content teams every single day. And in most cases, the theft took less than three minutes using a free Chrome extension anyone can install.
This article explains exactly how it happens, why most video platforms leave you exposed, and what genuine protection architecture actually looks like.
The False Sense of Security Most Creators Have
The most dangerous moment in content security is when a creator believes they are protected without actually being protected.
Disabling right-click on a video player feels like a lock on the door. An iframe embed feels like a barrier. A membership paywall feels like a vault. None of these are security measures in any technical sense — they are user interface decisions that create friction for casual users and zero friction for anyone with a browser extension.
The fundamental reality of video delivery is this: for a video to play in a browser, the media stream must travel from a server to that browser. That stream — whether delivered as a progressive MP4, an HLS playlist, or a DASH manifest — passes through the browser’s network layer. And anything that passes through the network layer can be intercepted.
Right-click locks block the context menu. They do not block the network. Token authentication adds a time-limited signature to a URL. It does not encrypt the stream itself. Basic embed restrictions tell the player where it can be embedded. They do not prevent the underlying file from being requested directly.
Surface-level protection gives creators confidence. It does not give them security.
How Chrome Extensions Actually Steal Your Video Content
Understanding the mechanism of the attack is the first step toward choosing a defense that actually addresses it.
The Extensions Creators Don’t Know About
Video DownloadHelper is a browser extension with millions of active installs. Flash Video Downloader, CatchVideo, and dozens of similar tools operate on the same principle. When a user visits a page and a video begins to play, these extensions monitor the browser’s active network requests in real time. They detect the media stream — whether it is an MP4 file, an HLS (.m3u8) stream, or a DASH manifest — and present the user with a one-click download option.
The extension does not need to bypass your paywall. It does not need your video’s direct URL. It simply watches what the browser is already receiving and captures it. The player’s security settings, your platform’s embed rules, and your membership gateway are entirely irrelevant at this stage. By the time any of those controls have been satisfied, the stream is already flowing — and the extension is already watching.
This is not a vulnerability in the traditional sense. It is not a bug that can be patched with a software update. It is a structural characteristic of how browser-based video delivery works. Any platform that does not address this at the encryption layer is leaving its users exposed, regardless of how many surface restrictions it applies.
Why Token Authentication Alone Is Not Enough
Token authentication is a legitimate and important security layer. It works by appending a time-limited cryptographic signature to the CDN delivery URL, ensuring that a stolen link cannot be replayed indefinitely. Many platforms present this as their primary security feature.
The problem is the delivery window. For a video to play without buffering interruptions, the authenticated token must remain valid for the duration of the viewing session. During that window — which can range from minutes to hours depending on platform configuration — the stream is live, authenticated, and flowing to the browser. An extension capturing that stream during the valid window has everything it needs.
Token authentication controls who can initiate a stream. It does not control what happens to that stream once it arrives. Without encryption at the content layer, the authenticated stream is still a readable, downloadable media file.
📌 Think your videos are protected? The most dangerous assumption in content security is an untested one. Inkrypt Videos offers real DRM-grade protection built for creators who cannot afford to lose their content. Call us at 804-500-2905 or visit inkryptvideos.com to see exactly what genuine protection looks like.
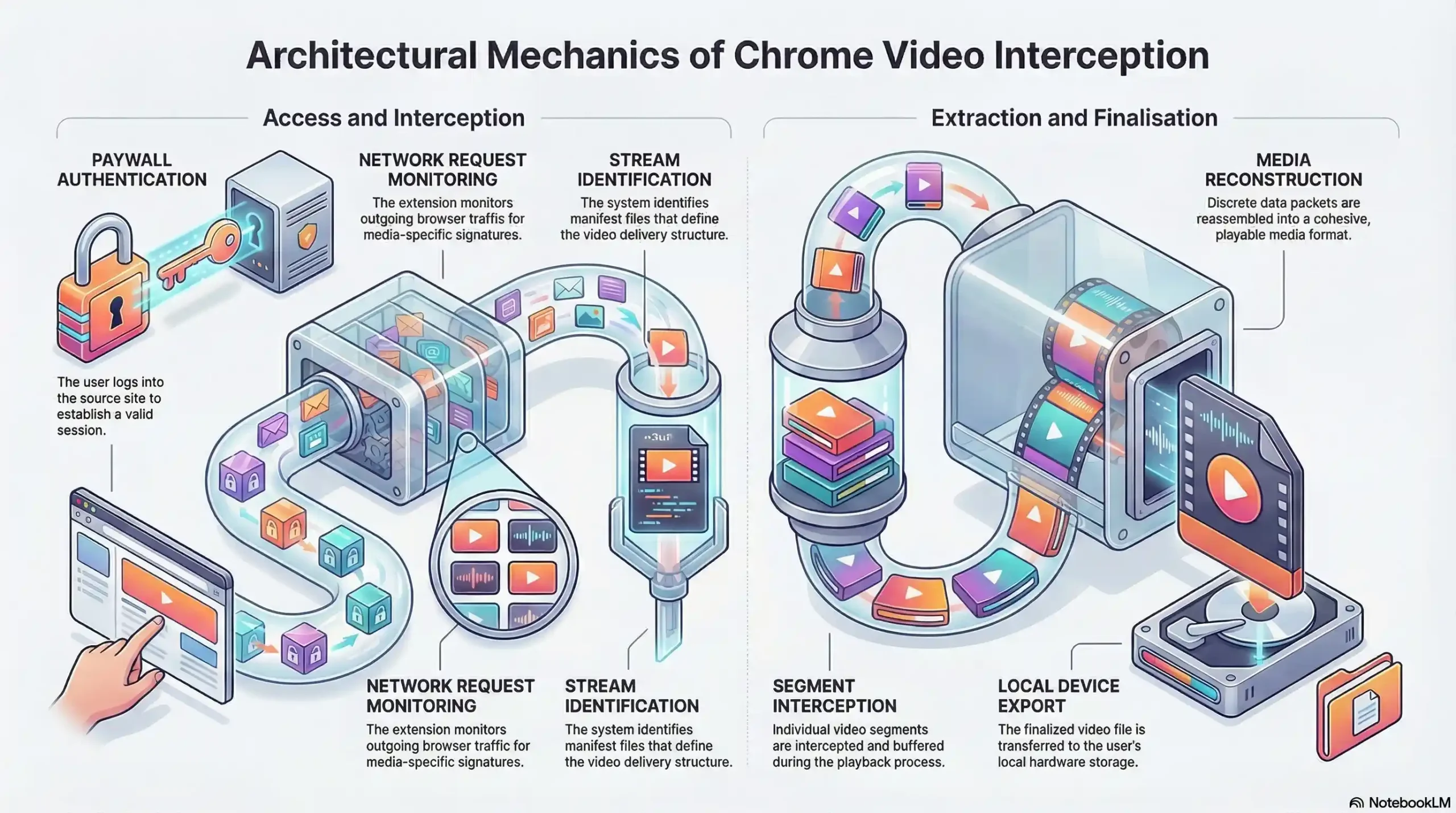
| Step | Action | Security Layer Bypassed |
|---|---|---|
| 1 | User visits paywall-protected video page | Membership gate passed (legitimate login) |
| 2 | Browser authenticates token and requests media stream | Token authentication satisfied |
| 3 | HLS/DASH stream begins flowing to browser | No encryption on stream content |
| 4 | Chrome extension detects active media network request | Right-click lock irrelevant |
| 5 | Extension presents one-click download to user | Embed restriction irrelevant |
| 6 | Full video downloaded to local device in minutes | No forensic trace left |
What “Real” Video Protection Actually Looks Like
Genuine video security operates at the content layer — not the interface layer. It means the media stream itself is encrypted, and decryption requires hardware or software authorization that a browser extension cannot replicate.
DRM Encryption — The Only Standard That Actually Works
Digital Rights Management (DRM) is not a feature. It is a content licensing architecture that governs how a media file can be decrypted, on which devices, under which conditions, and for how long. The three major DRM systems in active deployment are Google’s Widevine, Microsoft’s PlayReady, and Apple’s FairPlay. A robust platform implements all three to ensure device-wide compatibility.
When a video is DRM-encrypted, the media file stored on the CDN is not a readable video file. It is an encrypted payload. To play it, the viewer’s device must communicate with a license server, prove authorization, and receive a decryption key scoped specifically to that session and that device. The key never travels through the browser’s accessible memory in a usable form. There is nothing for a Chrome extension to intercept — because the stream itself, even if captured, is unreadable without the license.
AES-128 encryption applied at the CDN level adds a further layer: every segment of the HLS or DASH stream is individually encrypted. Even if a sophisticated attacker were to capture individual stream segments, assembling them into a playable file would require breaking the encryption — which is computationally infeasible with current technology.
Dynamic Watermarking — Your Forensic Safety Net
DRM prevents unauthorized downloading. Dynamic watermarking addresses the scenario where a human uses a camera pointed at a screen — the so-called “analog hole” — or where DRM is circumvented on a compromised device.
Unlike static watermarks, which apply the same visible or invisible mark to every viewer’s copy, dynamic watermarking embeds a unique, session-specific identifier into every stream delivered. This identifier is invisible to the viewer and changes position and encoding across the video, making it impossible to crop, blur, or edit out without destroying the video quality.
If a watermarked video appears on a piracy site, Inkrypt Videos’ forensic system can analyze the recovered copy and identify the exact account, session, and timestamp associated with that specific stream. The leaker is identified — even if they never downloaded the file directly, and even if the recording was made with a physical camera.
This transforms the security posture from reactive damage control to active deterrence. When users know that every stream they watch is uniquely fingerprinted to their session, the calculus of sharing changes entirely.
Domain Restriction and Token Authentication as Supporting Layers
Domain restriction ensures your videos cannot be embedded on unauthorized third-party sites. Token authentication ensures CDN delivery URLs cannot be harvested and reused. These are not replacements for DRM — they are complementary layers that close additional attack vectors.
Inkrypt Videos applies all three layers simultaneously: DRM encryption at the content level, dynamic watermarking for forensic identification, domain restriction to control embed contexts, and CDN token authentication to control delivery windows. No single layer is treated as sufficient. The architecture is designed around the assumption that any individual control may be tested — and that the system as a whole must hold regardless.
Widevine L1 vs L3 — Why Your Current Platform May Be Leaving You Exposed
Widevine is the most widely deployed DRM system in the world, used across Android devices, Chrome browsers, and Chromebook hardware. However, not all Widevine implementations are equal. Widevine operates across three security levels — L1, L2, and L3 — and the difference between L1 and L3 is the difference between genuine hardware-enforced security and software-only protection that can be bypassed on a rooted device.
| Feature | Widevine L1 | Widevine L3 |
|---|---|---|
| Decryption environment | Hardware Trusted Execution Environment (TEE) | Software only |
| Screen capture resistance | Hardware-enforced blocking | Limited — can be bypassed |
| Rooted device vulnerability | Resistant | Vulnerable |
| Maximum supported resolution | 4K HDR | 1080p (platform dependent) |
| Target use case | Premium content, enterprise media | Standard streaming |
| Extension interception resistance | High | Moderate |
Many video hosting platforms advertise Widevine DRM without specifying which level they implement. A platform delivering L3 only is providing software-layer protection — meaningful against casual users, but insufficient against determined attackers using rooted Android devices or modified browser environments.
Inkrypt Videos implements Widevine across applicable security levels, combined with PlayReady for Microsoft ecosystems and FairPlay for Apple devices, ensuring that protection quality is not sacrificed for the sake of compatibility.
📌 Your content deserves more than software-level protection. Inkrypt Videos delivers enterprise-grade DRM with Widevine integration, dynamic watermarking, and Amazon CDN global delivery — with a setup time of 30 minutes. Visit inkryptvideos.com or call 804-500-2905 to get started today.
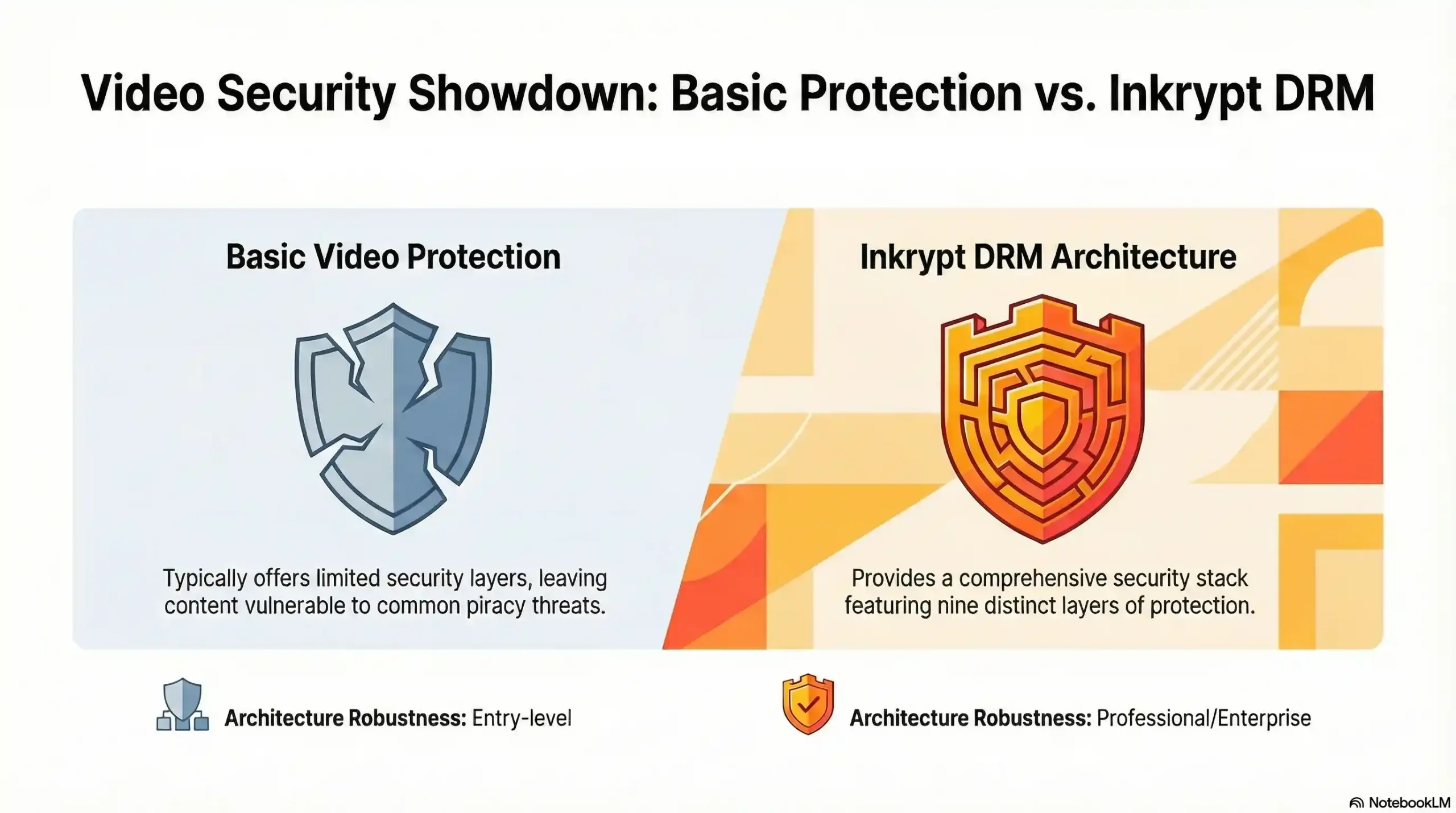
| Protection Layer | Basic Platform | Inkrypt Videos |
|---|---|---|
| Right-click disable | ✓ | ✓ |
| Embed domain restriction | ✓ | ✓ |
| CDN token authentication | ✓ | ✓ |
| AES-128 stream encryption | ✗ | ✓ |
| Widevine / PlayReady / FairPlay DRM | ✗ | ✓ |
| Dynamic forensic watermarking | ✗ | ✓ |
| Chrome extension interception blocked | ✗ | ✓ |
| Screen recording resistance | ✗ | ✓ |
| Leaker identification capability | ✗ | ✓ |
Does Vimeo or YouTube Protect Your Videos From Chrome Extensions?
This is one of the most common questions asked by course creators and media publishers evaluating their options — and it deserves a direct, honest answer.
YouTube applies its own proprietary DRM to content delivered through the YouTube platform. However, YouTube is a public distribution platform, not a secure content delivery system. Videos uploaded to YouTube — even unlisted ones — are subject to YouTube’s terms, YouTube’s ad policies, and YouTube’s infrastructure decisions. The platform is not designed to protect premium paid content, and the ecosystem of download tools targeting YouTube specifically is enormous.
Vimeo offers meaningful security upgrades over basic hosting, including domain-level privacy controls, password protection, and in its enterprise tier, some DRM capabilities. For casual content protection, Vimeo’s controls are reasonable. For creators whose business model depends on content exclusivity — course creators charging hundreds or thousands of dollars per enrollment, media companies protecting distribution windows, publishers monetizing premium archives — Vimeo’s architecture was not built for that threat model.
The fundamental distinction is this: general-purpose video platforms optimize for reach, discoverability, and ease of use. Dedicated content protection platforms optimize for security architecture. These are different engineering priorities, and they produce different outcomes when a determined user installs a download extension.
Local Resources & Citations
1. U.S. Copyright Office — Copyright.gov
Why it helps: The official US government authority on the Digital Millennium Copyright Act (DMCA) — creators can reference this to understand their legal rights when their video content is stolen or illegally redistributed online.
2. World Intellectual Property Organization — WIPO.int
Why it helps: The United Nations agency governing global intellectual property law — provides internationally recognized frameworks for digital content protection that apply to creators distributing video content across borders.
3. Google Widevine — Widevine.com
Why it helps: The official technical specification page for Google’s Widevine DRM system — creators and enterprises can verify L1/L3 certification standards and device compatibility requirements directly from the manufacturer.
4. MIT OpenCourseWare — ocw.mit.edu
Why it helps: MIT’s publicly accessible academic resource on digital rights management and content security provides a peer-reviewed educational context that reinforces the technical claims made throughout the article with institutional authority.
The Inkrypt Videos Solution — Built for Creators Who Cannot Afford to Lose Content
Inkrypt Videos was built specifically to close the gap between how protected creators think they are and how protected they actually are. The platform is not a general-purpose video host that added security features. It is a security-first architecture that also delivers enterprise video performance.
The core stack includes multi-DRM encryption (Widevine, PlayReady, FairPlay), dynamic forensic watermarking, AES-128 CDN-level stream encryption, domain restriction, and token-authenticated delivery — all applied simultaneously, not as optional add-ons.
Global delivery is handled through Amazon CDN integration, ensuring that a course creator in Toronto, a student in Singapore, and an enterprise viewer in Frankfurt all receive the same zero-buffering, high-fidelity stream — with the same security architecture applied regardless of geography or device.
Integration requires no dedicated technical team. The WordPress plugin and straightforward API mean that a creator with no development background can have full DRM protection live within 30 minutes. The platform supports all devices, including older hardware that many enterprise DRM solutions exclude, ensuring that security does not come at the cost of student or viewer accessibility.
Real-time analytics provide visibility into viewing behavior, engagement patterns, and access logs — giving creators both the business intelligence to improve their content and the security intelligence to identify anomalous access patterns before they become a piracy incident.
Inkrypt Videos is a registered US company, reachable at 1528 W Sunset Ave, Springdale, Arizona 72764, and operates a global content protection infrastructure built for creators and enterprises who understand that their video content is not just media — it is their business.
📌 Stop hoping your videos are protected. Know that they are. Inkrypt Videos delivers DRM encryption, dynamic watermarking, and global CDN performance — with setup in 30 minutes and support you can actually reach. Call 804-500-2905 or visit inkryptvideos.com today. Your content built your business. Protect it accordingly.
Frequently Asked Questions
No — Chrome extensions cannot download videos that are protected with properly implemented DRM encryption. DRM systems such as Widevine and PlayReady encrypt the media stream at the content layer, meaning the data flowing to the browser is an unreadable encrypted payload. Without a hardware or software-authorized decryption license scoped to that specific session and device, the captured stream cannot be assembled into a playable file. Extensions that intercept HLS or DASH streams are only effective against unencrypted or token-only protected content.
The safest platform for hosting course videos is one that implements multi-layer DRM encryption — including Widevine, PlayReady, and FairPlay — combined with dynamic forensic watermarking and CDN-level AES-128 stream encryption. Inkrypt Videos is purpose-built for this use case, offering enterprise-grade DRM protection, leaker identification through dynamic watermarking, and global delivery via Amazon CDN, with a 30-minute integration process designed for non-technical creators.
Widevine DRM prevents video piracy by encrypting the media file so that it cannot be played without an authorized decryption license. When a viewer requests a video, their device must authenticate with a Widevine license server and receive a session-specific decryption key. This key is processed inside a secure environment and is never exposed in a usable form to the browser or any extension monitoring network traffic. The video stream itself, even if intercepted, remains unreadable without the license.
Widevine L1 processes decryption inside a hardware-secured Trusted Execution Environment (TEE), making it resistant to software-based attacks and screen capture tools. Widevine L3 operates in software only, which is sufficient for casual protection but vulnerable to bypass on rooted Android devices or modified browser environments. L1 supports up to 4K HDR delivery; L3 is typically capped at 1080p. For premium and enterprise content, L1 is the required standard.
Dynamic watermarking alone is not sufficient to prevent video theft — it is a forensic identification tool, not a prevention mechanism. Its function is to embed a unique, invisible, session-specific identifier into every stream so that if a video is leaked, the source can be traced back to the exact account and viewing session. For active prevention, dynamic watermarking must be combined with DRM encryption. Together, DRM blocks unauthorized downloading while watermarking identifies any leak that occurs through screen recording or physical camera capture.
Yes — Inkrypt Videos offers a WordPress plugin that integrates directly with standard WordPress installations, allowing course creators and content publishers to deploy full DRM-encrypted video protection without writing code. The integration process takes approximately 30 minutes from account setup to live protected video delivery. The platform also provides a simple API for custom integrations with other content management systems and e-learning platforms.
No — disabling right-click provides no meaningful protection against video theft. Right-click restrictions only block the browser’s context menu, preventing casual users from selecting “Save video as.” They do not affect the underlying network stream. Anyone using a Chrome extension, browser developer tools, or a download manager can capture the media stream regardless of right-click settings. Genuine video protection requires encryption at the content delivery layer, not interface-level restrictions.
Chrome extensions like CocoCut or Video DownloadHelper detect video streams via network requests, bypassing basic protections like right-click disables.
Extensions fetch videos in the background using host permissions, ignoring client-side blocks like right-click or hotkeys.
Use server-side DRM encryption, dynamic watermarking, signed URLs, and domain referrers to make streams unplayable outside your site.
Yes, via background scripts or webRequest API to alter headers and fetch cross-origin videos directly.
Install extensions like Video DownloadHelper, play your video, and check if downloads fail or show black screens/no audio.
Network sniffers in extensions reveal MP4 links or segments despite JavaScript minification.
Disclaimer:
This article is intended for educational and informational purposes only. It explains common methods used in video content delivery and potential vulnerabilities to help creators make informed security decisions. It does not promote or encourage unauthorized downloading, distribution, or misuse of copyrighted material.

