Table of Contents
ToggleForensic video watermarking embeds a unique, invisible identifier into every copy of a video at the per-user level. Unlike static watermarks — which apply the same mark to every copy — dynamic watermarking creates an unbreakable chain of evidence that traces leaked content back to the exact individual who shared it, making it the only watermarking method that actually identifies pirates.
Every day, premium video content is stolen, reshared, and monetized by people who never paid for it. For online course creators, enterprise media companies, and premium content publishers, this isn’t a theoretical risk — it’s an active, daily revenue hemorrhage. The frustrating reality? Most creators have watermarks on their videos and still cannot identify a single pirate.
That is the central failure of static watermarking. And it is exactly the problem that dynamic, forensic-grade watermarking was engineered to solve.
This guide breaks down how each method works, where static watermarking catastrophically fails under real-world piracy attacks, and how dynamic watermarking gives you something no static system ever can: a name.
1. Why Most Video Watermarks Fail to Catch Pirates
The instinct to watermark video content is correct. The execution, for most creators and platforms, is dangerously inadequate.
1.1 The False Security of Visible Watermarks
A visible watermark — your logo or channel name stamped in the corner of your video — feels like protection. It signals ownership. It looks professional. But from a forensic standpoint, it does precisely nothing to help you identify who leaked your content.
Here is why: a visible static watermark is the same on every single copy of your video. Whether your course is accessed by Student A in London or Student B in Dubai, they both receive an identical watermark. If either of them leaks the content, you have no mechanism to distinguish which copy was the source. You know your content was stolen. You have no idea by whom.
Worse, visible watermarks are trivially removed by anyone with basic video editing knowledge. AI-powered inpainting tools — freely available online — can erase a corner logo in minutes, leaving no trace of your branding. What you believed was a security measure has become a cosmetic feature.
1.2 What Pirates Actually Do to Your Content
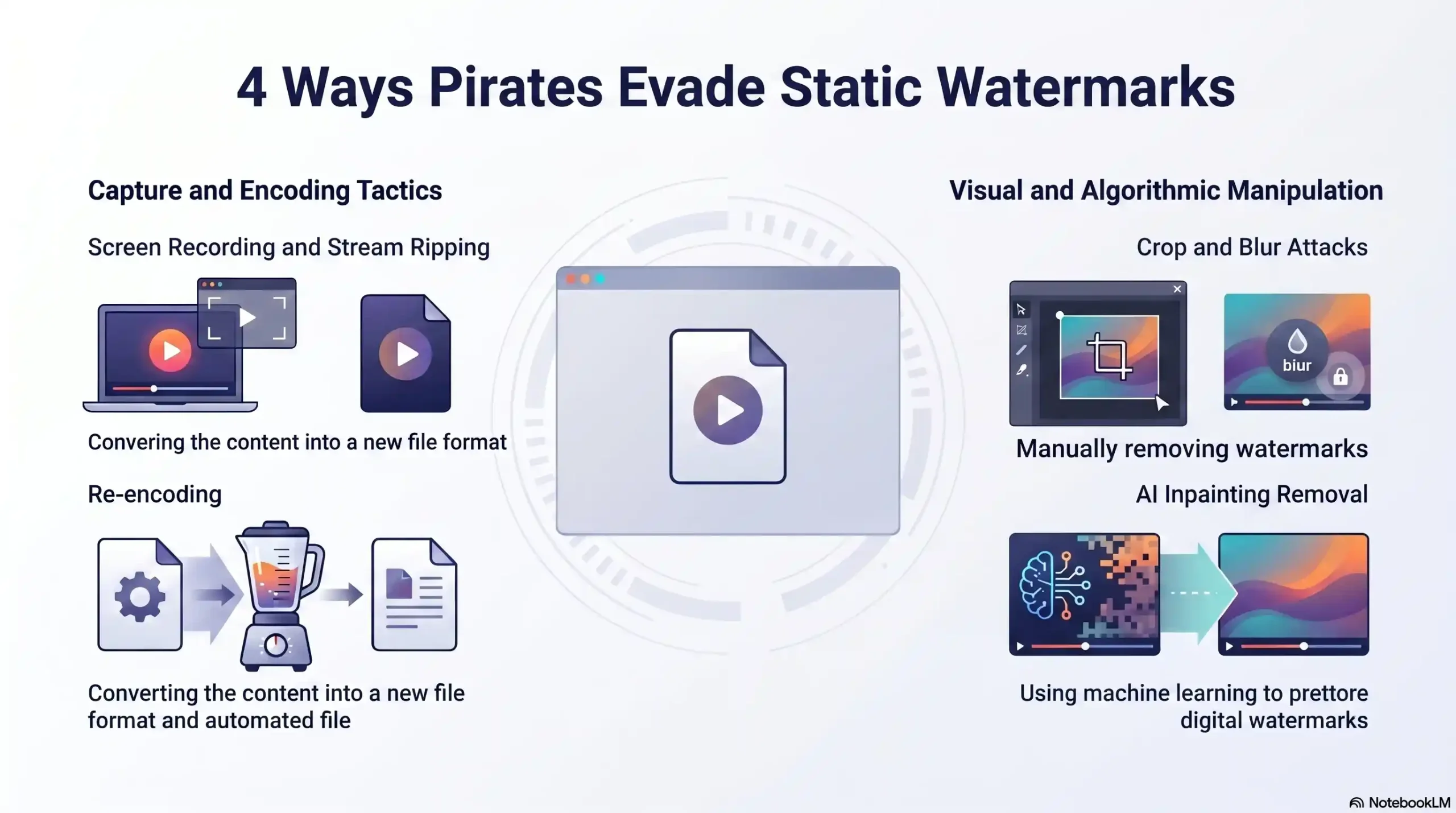
Understanding how content theft actually happens is essential to understanding why static watermarking cannot survive it. Pirates do not simply download a file and reshare it unchanged. They run it through a deliberate pipeline designed to strip every identifying marker you have applied.
The most common attack vectors include screen recording, where the entire video is captured at the display level, bypassing any server-side protection entirely. Stream ripping tools intercept and download the video stream directly during playback, often producing a clean copy with no visible watermark depending on placement. Re-encoding attacks compress and reformat the stolen video, which destroys any fragile static watermark data embedded in the original file. Finally, cropping and blur attacks physically alter the frame to remove visible logo placements.
A static watermark survives none of these attacks reliably. A forensic dynamic watermark is engineered to survive all of them.
📞 See How Inkrypt Videos Protects Your Content From Real Piracy Attacks — Contact us today at +971 544 077 967
2. Static Watermarking — What It Is and Where It Breaks Down
2.1 How Static Watermarking Works
Static watermarking applies a fixed, uniform identifier to a video file. This identifier can be visible — a logo, text overlay, or channel branding — or invisible, embedded as metadata or a subtle pixel-level pattern. The defining characteristic of static watermarking is that the same mark is applied universally across every copy of the content distributed.
This approach was developed for broadcast media environments where mass distribution to anonymous audiences made per-user identification impractical. In those contexts, static watermarking served a legitimate purpose: proving ownership in copyright disputes. For modern digital content businesses built on subscription access, course sales, and premium memberships, it is fundamentally insufficient.
2.2 The Critical Limitations of Static Watermarks
The architectural flaw of static watermarking is not technical — it is logical. When every user receives an identical watermark, the watermark contains zero information about the individual user. It can confirm that content belongs to you. It cannot tell you which of your ten thousand subscribers leaked it.
| Attack Method | How It Works | Defeats Static Watermark? | Defeats Dynamic Watermark? |
|---|---|---|---|
| Screen Recording | Captures display output bypassing server protection | ✅ Yes | ❌ No — user token persists |
| Stream Ripping | Intercepts video stream during playback | ✅ Yes | ❌ No — embedded at encoding level |
| AI Inpainting Removal | Erases visible logo using AI fill technology | ✅ Yes | ❌ No — invisible steganographic layer |
| Re-encoding Attack | Recompresses video destroying fragile watermark data | ✅ Yes | ❌ No — survives compression |
| Crop & Blur Attack | Physically removes visible watermark placement | ✅ Yes | ❌ No — not placement-dependent |
The conclusion is unambiguous: static watermarking is security theater. It satisfies the psychological need to feel protected without providing the forensic capability to act on a breach.
3. Dynamic Watermarking — The Forensic Standard for Identifying Pirates
3.1 How Dynamic Watermarking Works at a Technical Level
Dynamic watermarking operates on a fundamentally different architectural principle. Instead of applying a uniform mark to every copy, dynamic watermarking generates a unique, imperceptible identifier for each individual user session at the moment of playback or delivery.
This identifier is embedded using steganographic encoding — a technique that hides information within the video data itself at the pixel level, invisible to the human eye and undetectable by standard video analysis tools. Critically, this embedded token is engineered to survive the full range of piracy attack vectors: screen recording captures it, re-encoding preserves it, and cropping cannot remove it because it is distributed across the entire frame rather than anchored to a single location.
When dynamic watermarking is layered on top of DRM encryption — as implemented by Inkrypt Videos — the result is a two-barrier security architecture. Encryption prevents unauthorized access at the stream level. Dynamic watermarking ensures that even if a user bypasses encryption through legitimate access and then leaks the content, the watermark identifies them precisely.
3.2 The Forensic Identification Workflow
The true power of dynamic watermarking is not prevention — it is identification. Here is exactly how the forensic workflow operates when a breach occurs:
Step 1 — Breach Detection: Leaked content is discovered on a piracy platform, Telegram group, or unauthorized site. The content creator or security team identifies the unauthorized copy.
Step 2 — Watermark Extraction: The forensic watermarking system analyzes the leaked video file or stream, extracting the embedded unique identifier even if the video has been re-encoded, compressed, or partially edited.
Step 3 — Token Matching: The extracted token is matched against the platform’s user database. Because each token was generated uniquely for a specific user session, the match returns a single account — the source of the leak.
Step 4 — Evidence Assembly: The system produces a forensic report linking the leaked content to the identified user account, including session data, access timestamp, and device information.
Step 5 — Action: The creator or enterprise security team takes targeted action — account termination, legal proceedings, or demand letters — backed by irrefutable forensic evidence.
This is the difference between knowing your content was stolen and knowing exactly who stole it.
3.3 Dynamic Watermarking vs. Static Watermarking — The Definitive Comparison
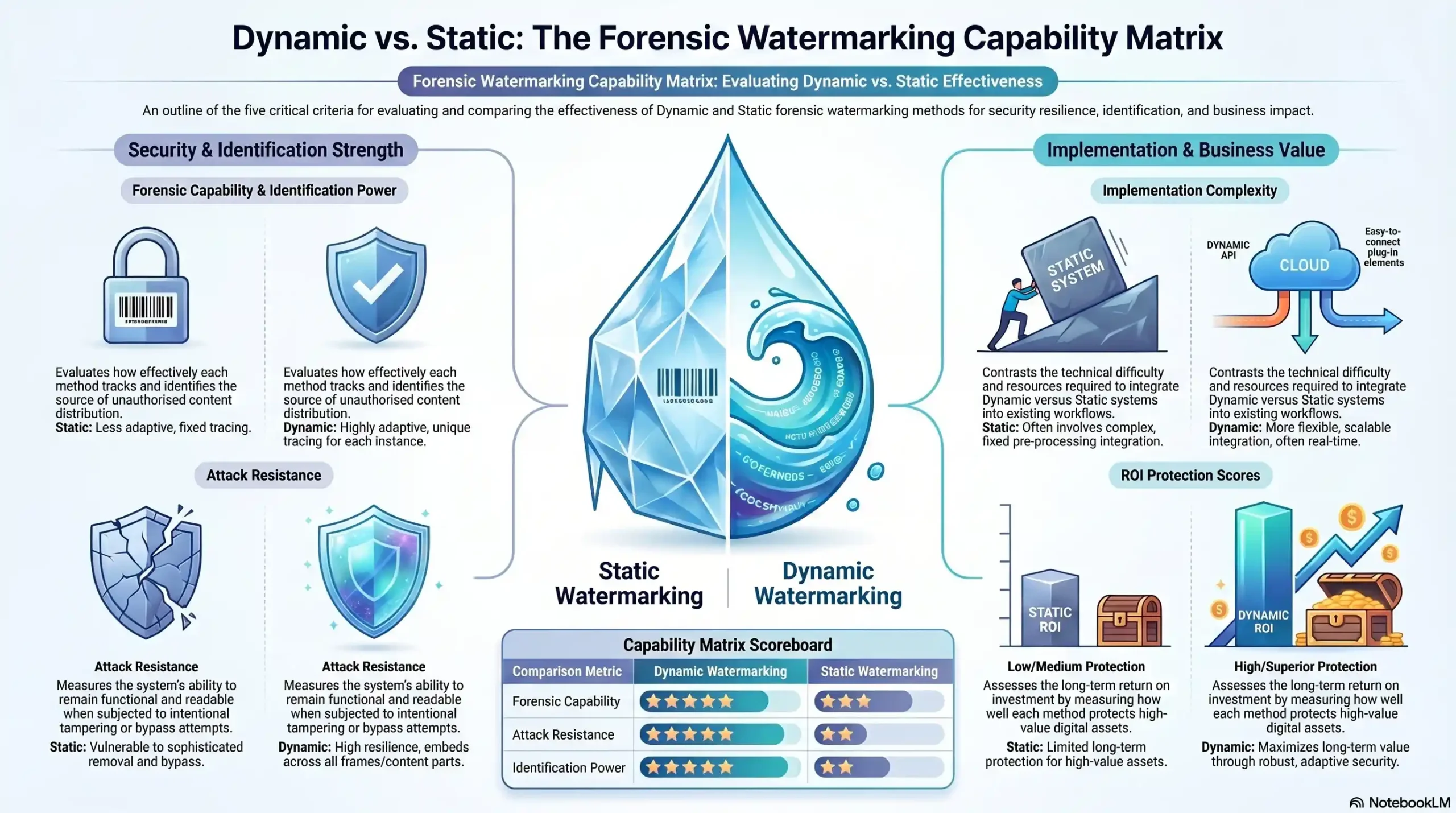
| Capability | Static Watermarking | Dynamic Watermarking |
|---|---|---|
| Proves Ownership | ✅ Yes | ✅ Yes |
| Identifies Individual Leaker | ❌ No | ✅ Yes |
| Survives Screen Recording | ❌ No | ✅ Yes |
| Survives Re-encoding | ❌ No | ✅ Yes |
| Survives AI Removal Tools | ❌ No | ✅ Yes |
| Forensic Evidence Generation | ❌ No | ✅ Yes |
| Per-User Unique Token | ❌ No | ✅ Yes |
| Works With DRM Encryption | ⚠️ Limited | ✅ Full Integration |
| Deters Future Leaks | ⚠️ Minimal | ✅ Strong Deterrent |
| Legal Action Support | ⚠️ Weak | ✅ Court-Admissible Evidence |
4. The Real Cost of Getting Watermarking Wrong
4.1 Quantifying Revenue Loss From Video Piracy
The global cost of digital piracy exceeds $70 billion annually across industries, with online video content representing one of the fastest-growing theft categories. For individual course creators, the mathematics are sobering. A single $997 course with 500 enrolled students represents a $498,500 revenue event. If even 5% of those students share access credentials or leak course content to piracy networks, the downstream exposure — content redistributed to audiences who never pay — can dwarf the original revenue figure many times over.
For enterprise media companies, a single content leak of a premium series or proprietary training library carries not only direct revenue implications but regulatory exposure, contractual liability with content partners, and irreversible reputational damage in licensing markets.
4.2 Why “Good Enough” Security Is Never Good Enough
The most dangerous position a content business can occupy is believing their current watermarking solution is adequate without having tested it against real attack vectors. Static watermarks create a documented false confidence gap — creators see their logo on screen and believe they are protected, while pirates see the same logo as a minor inconvenience requiring thirty seconds of editing to eliminate.
Beyond revenue, there is a legal dimension that is consistently underestimated. Pursuing copyright infringement action without forensic evidence of the specific infringer is extraordinarily difficult and expensive. Courts require proof — not suspicion, not circumstantial access logs, but traceable, content-embedded evidence directly linking a specific individual to the leaked copy. Only dynamic forensic watermarking generates that evidence automatically, at scale, on every single piece of content delivered.
5. How Inkrypt Videos Implements Forensic-Grade Dynamic Watermarking
5.1 The Inkrypt Videos Security Architecture
Inkrypt Videos was engineered from the ground up as a forensic content protection platform, not a video hosting service that added security features as an afterthought. The platform’s dynamic watermarking system operates as a native layer within its broader DRM encryption stack, ensuring that protection is not a bolt-on feature but an architectural constant.
Every video delivered through Inkrypt Videos receives a unique per-session watermark token generated at the moment of playback authorization. This token is embedded invisibly using steganographic techniques that survive the full spectrum of known piracy attack vectors. The watermark layer operates beneath the DRM encryption layer — meaning content is protected at both the access level and the forensic identification level simultaneously.
Global content delivery is powered by Amazon CDN integration, ensuring that forensic watermarking does not come at the cost of performance. Content creators and enterprise clients worldwide receive zero-buffer delivery with full forensic protection active on every stream. Setup requires approximately 30 minutes — compared to weeks or months for legacy enterprise DRM solutions — with WordPress plugins and straightforward API integration available for technical teams.
Reach Inkrypt Videos directly at +971 544 077 967 to discuss your specific content protection architecture.
5.2 Who Needs Forensic Watermarking Right Now
Online course creators generating revenue from premium courses priced at $500 or above are operating in the highest-risk category for content piracy. A single leaked course in an active Telegram group or piracy forum can result in thousands of unauthorized accesses within days of discovery. Forensic watermarking converts that nightmare scenario from an unsolvable mystery into an actionable investigation with a named suspect.
Enterprise media and streaming companies face the compounded risk of contractual obligations to content partners, regulatory compliance requirements, and the reputational consequences of publicly disclosed security failures. Forensic watermarking provides the audit trail and breach response capability that enterprise security frameworks demand.
Premium content publishers and media institutes whose entire competitive advantage rests on the exclusivity of their content library cannot afford the false comfort of static watermarking. When content exclusivity is the product, forensic protection of that exclusivity is a business-critical infrastructure requirement.
📞 Start Protecting Your Content With Forensic-Grade Watermarking Today — Contact Inkrypt Videos at +971 544 077 967
6. Choosing the Right Watermarking Strategy for Your Content Business
6.1 Decision Framework — Static vs. Dynamic by Use Case
Not every piece of video content carries the same risk profile or requires the same level of forensic protection. The following framework helps content creators and enterprise teams allocate watermarking resources appropriately.
| Content Type | Monetization Level | Piracy Risk | Recommended Method |
|---|---|---|---|
| Free YouTube-style content | None | Low | Static (branding only) |
| Low-cost courses (under $100) | Low | Low-Medium | Static with access controls |
| Premium courses ($500+) | High | High | Dynamic — Non-Negotiable |
| Enterprise training libraries | High | High | Dynamic — Non-Negotiable |
| Streaming service originals | Very High | Very High | Dynamic + DRM Encryption Stack |
| Licensed media content | Very High | Very High | Dynamic + DRM Encryption Stack |
6.2 Implementation Checklist for Content Creators & Enterprises
Before committing to any watermarking solution, use this five-point verification checklist to ensure the solution will hold under real-world attack conditions:
✅ Point 1 — Per-User Uniqueness: Does the solution generate a unique watermark for each individual user session, or does it apply the same mark to all users? If the same mark — it is static and forensically worthless.
✅ Point 2 — Attack Survival Testing: Has the watermark been tested against screen recording, re-encoding, and AI removal tools? Demand documented evidence of survival rates, not vendor claims.
✅ Point 3 — Forensic Extraction Capability: Can the platform extract the watermark from a re-encoded, compressed, or partially edited leaked copy? This is the forensic moment that matters — if extraction fails on degraded copies, identification fails.
✅ Point 4 — DRM Integration: Is watermarking integrated with DRM encryption, or is it a standalone feature? Layered protection is significantly more resilient than single-barrier approaches.
✅ Point 5 — Evidence Output: Does the system produce a forensic report suitable for legal proceedings? Actionable breach response requires documented, court-admissible evidence chains.
🔗 Local Resources & Citations
1. World Intellectual Property Organization (WIPO)
WIPO — United Nations Agency for IP: Reference here for internationally recognized copyright treaties, anti-piracy legal frameworks, and global intellectual property protection standards that validate the legal necessity of forensic watermarking.
2. U.S. Copyright Office — DMCA Resources
U.S. Copyright Office (.gov): Use this official government resource to file DMCA takedown notices, understand safe harbor provisions, and build the legal paper trail that forensic watermark evidence directly supports.
3. Moving Picture Experts Group — MPEG Standards
MPEG — Official Video Encoding Standards Body: Reference here for the technical specifications behind video compression standards (MPEG-4, HEVC) that define how forensic watermarks must be engineered to survive re-encoding and compression attacks.
4. European Union Intellectual Property Office (EUIPO)
EUIPO — EU Anti-Piracy Observatory: Consult here for official European data on digital piracy trends, revenue impact studies, and enforcement frameworks — ideal for substantiating ROI and revenue-loss claims within the article.
7. Conclusion — Watermarking Is Only as Good as Its Ability to Name the Pirate
The question was never whether to watermark your video content. The question has always been whether your watermark can do the one thing that actually matters when your content is stolen: tell you exactly who took it.
Static watermarking cannot answer that question. It was never designed to. It belongs to an era of broadcast media where individual identification was technically impossible and legally unnecessary. That era ended the moment content businesses moved to subscription access, course enrollment, and premium digital distribution.
Dynamic forensic watermarking is not an upgrade to static watermarking — it is a categorically different technology serving a categorically different purpose. It transforms your content security posture from reactive and powerless to proactive and forensically equipped.
Inkrypt Videos delivers that forensic capability with the global performance, implementation simplicity, and DRM integration depth that real content businesses require. Real security for real creators — worldwide, at enterprise grade, in 30 minutes.
When your content matters enough to protect, it matters enough to protect with a system that can name the pirate.
📞 Ready to Identify Your Next Pirate? Get Forensic Watermarking With Inkrypt Videos — +971 544 077 967
Frequently Asked Questions
Static watermarking applies an identical mark to every copy of a video, proving ownership but offering zero ability to identify individual leakers. Dynamic watermarking generates a unique, invisible identifier for each specific user session. When content is leaked, the dynamic watermark is extracted from the stolen copy and matched to the exact user who shared it — something static watermarking is architecturally incapable of doing
Visible static watermarks can be removed using freely available AI inpainting tools, cropping, or blurring in minutes. Forensic dynamic watermarks — such as those implemented by Inkrypt Videos — are embedded invisibly at the pixel level using steganographic encoding. They are engineered to survive screen recording, re-encoding, compression, and AI removal attacks, making them effectively irremovable without destroying the video entirely
When a breach is detected, the forensic watermarking system analyzes the leaked video — even if re-encoded or compressed — and extracts the unique embedded token. This token is matched against the platform’s user database, returning the exact account and session that was the source of the leak, complete with access timestamp and device data for legal evidence assembly
For any course priced above $500, dynamic watermarking is not optional — it is essential infrastructure. A single leaked course redistributed across piracy networks can generate thousands of unauthorized accesses within days. Dynamic watermarking provides the only mechanism to identify the source of the leak, take targeted legal or platform action, and deter future breaches through the credible threat of forensic identification
No. Professional forensic watermarking systems embed identifiers at the steganographic level — invisible to the human eye and imperceptible during playback. Inkrypt Videos delivers dynamic watermarking through Amazon CDN integration, ensuring zero-buffer global streaming performance is maintained at full quality while forensic protection operates invisibly on every session
Once the watermark extraction matches the leaked content to a specific user account, you have four immediate action options: terminate the identified account and revoke access, issue a formal DMCA takedown against the pirated content, pursue direct legal action supported by the forensic evidence report, or contact the identified individual with a documented cease-and-desist. Inkrypt Videos’ system generates the forensic report needed for all four responses. For immediate assistance, contact +971 544 077 967.
Pirates often crop, blur, or mirror the video, or re‑encode and re‑stream it; invisible forensic watermarks and quickly moving visible marks are specifically designed to resist these modifications.
Yes, when you inform users in your terms and privacy policy and only embed lawful identifiers (like account‑linked email or IP), it’s widely used by streaming platforms and learning platforms for anti‑piracy.
Most systems handle both: dynamic overlays can be injected in real‑time for live‑stream, and forensic or visible marks can be baked into VOD files or segmented streams for on‑demand playback.
Limitations include: heavier client‑side processing, possible UX friction if overdone, and the fact that technically sophisticated pirates may still strip or distort some marks, so it works best combined with DRM and analytics.
Disclaimer: The information provided in this article is for educational and informational purposes only and does not constitute legal advice. While forensic dynamic watermarking and DRM encryption are highly effective methods for deterring piracy and identifying unauthorized distribution, no digital security measure can guarantee absolute protection against all forms of content theft. Content creators and enterprises should consult with legal counsel regarding copyright enforcement, compliance, and taking legal action against identified infringers in their specific jurisdictions.

