Table of Contents
ToggleCourse piracy networks are organized criminal ecosystems that systematically steal, repackage, and resell premium digital courses and educational content through dark web marketplaces, Telegram groups, and credential-sharing platforms. These underground economies cost content creators and e-learning platforms an estimated $74 billion annually in lost revenue globally, operating with the same sophistication as legitimate digital businesses — complete with tiered pricing, reseller programs, and customer support channels.
The moment a creator publishes a premium online course, a clock starts ticking. Somewhere in the invisible layers of the internet — inside encrypted Telegram channels, on dark web storefronts, and across credential-sharing forums — the machinery of an entire underground economy begins assessing, targeting, and monetizing that content. This is not the work of lone pirates with too much free time. This is organized, profitable, and growing.
Understanding how course piracy networks operate is no longer optional for serious content creators, e-learning platforms, or enterprise media companies. It is a matter of financial survival.
1. What Is the Course Piracy Underground Economy?
1.1 — Defining the Threat: More Than Casual Downloading
Most creators imagine content piracy as a single bad actor downloading a video and sharing it with a friend. The reality is categorically different. Course piracy networks are structured criminal enterprises with defined roles, revenue models, and distribution infrastructure. They function less like opportunistic theft and more like a shadow version of the legitimate digital distribution industry they are parasitizing.
These networks acquire premium course content through multiple vectors — compromised platform accounts, inside-access exploitation, screen recording operations, and increasingly, automated credential stuffing attacks that bypass login security at scale. Once acquired, content is not simply uploaded and shared. It is processed, rebranded, bundled, and sold through tiered distribution channels designed to maximize revenue while minimizing exposure to legal action.
The sophistication of these operations mirrors legitimate SaaS businesses. Some networks maintain customer service channels, offer “subscription” access to libraries of stolen courses, and even provide refunds to maintain seller ratings on underground marketplaces. This is not casual piracy. This is a business.
1.2 — The Scale: How Much Are Creators Actually Losing?
The financial damage inflicted by course piracy networks is staggering and systematically underreported. The global e-learning market is projected to exceed $400 billion by 2026, and industry analysts estimate that 15–20% of premium course revenue is lost annually to piracy and unauthorized distribution.
For an individual creator generating $200,000 per year in course sales, that represents $30,000–$40,000 in annual losses — revenue that disappears silently, never appearing in any refund report or analytics dashboard. For enterprise platforms operating at scale, the losses compound into tens of millions of dollars per year.
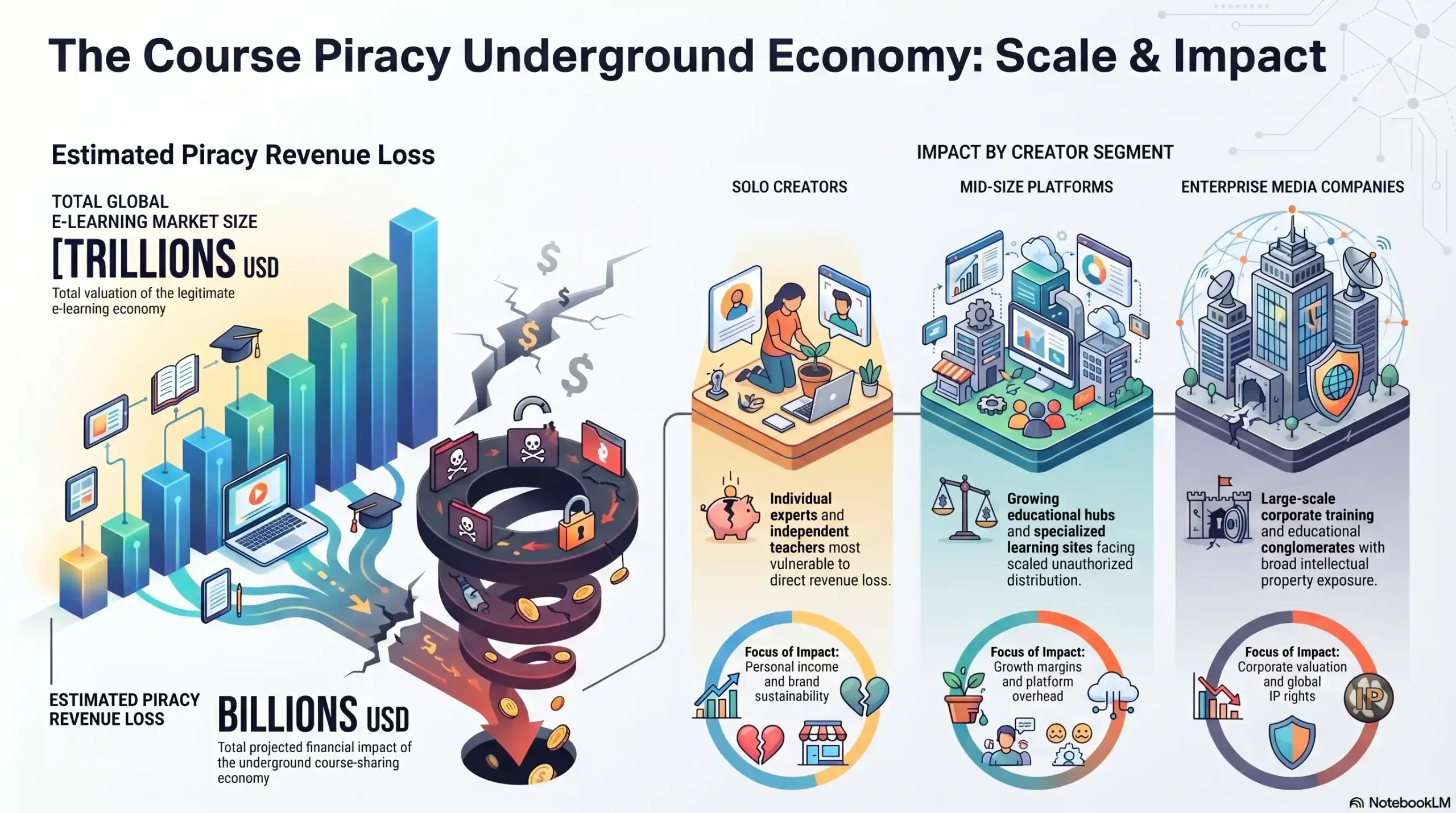
| Creator Segment | Est. Annual Revenue | Est. Piracy Loss (15–20%) | Primary Attack Vector |
|---|---|---|---|
| Solo Course Creator | $50K–$200K | $7,500–$40,000 | Credential sharing, screen recording |
| Mid-Size E-Learning Platform | $500K–$5M | $75K–$1M | Credential stuffing, account reselling |
| Enterprise Media Company | $10M+ | $1.5M–$3M+ | DRM bypass, organized reseller networks |
| Educational Institution | $1M–$20M | $150K–$4M | Bulk credential theft, content leakage |
2. Anatomy of a Course Piracy Network
2.1 — The Supply Chain: From Theft to Sale in 5 Steps
Understanding the piracy supply chain is the first step to dismantling it. Every piece of stolen course content passes through a remarkably consistent five-stage process before it generates revenue for those who stole it.
Step 1 — Acquisition: Content is obtained through compromised credentials, screen recording software, or exploited platform vulnerabilities. High-value courses are specifically targeted based on price point and market demand.
Step 2 — Processing: Raw stolen content is stripped of original watermarks where possible, re-encoded to remove identifying metadata, and in some cases, rebranded with alternative titles to evade automated detection systems.
Step 3 — Staging: Processed content is uploaded to hosting infrastructure deliberately chosen for its legal inaccessibility — servers in jurisdictions with weak IP enforcement, bulletproof hosting providers, or distributed file-sharing networks resistant to takedown requests.
Step 4 — Distribution: Staged content is listed across multiple channels simultaneously — dark web marketplaces, private Telegram channels, Discord servers, and surface-web “course dump” websites that operate in DMCA safe harbor gray zones.
Step 5 — Monetization: Networks generate revenue through one-time sales of individual courses, subscription access to entire stolen libraries, wholesale distribution to downstream resellers, and affiliate commission structures that incentivize further distribution.
2.2 — The Key Players: Who Runs These Networks?
Course piracy networks are rarely the work of a single individual. They operate with defined roles that mirror legitimate business structures. Acquisition specialists focus exclusively on obtaining new content at volume. Technical operators manage hosting infrastructure and evade takedown systems. Distribution managers maintain marketplace listings and customer-facing channels. Resellers purchase content wholesale and operate their own downstream storefronts, often with no direct knowledge of or connection to the original theft.
This compartmentalization is deliberate. It creates legal insulation between the network’s leadership and its customer-facing operations, making prosecution and content recovery dramatically more difficult.
3. The Reseller Economy — Piracy as a Business Model
3.1 — Telegram Groups, Discord Servers & Dark Web Marketplaces
The distribution layer of the course piracy underground economy is not hidden in impenetrable darkness. Much of it operates in plain sight, protected not by obscurity but by volume, jurisdictional complexity, and platform policy gaps.
Telegram has become the primary distribution channel for mid-tier course piracy operations. Private and semi-public channels routinely list thousands of stolen courses, with administrators operating subscription models charging $10–$30 per month for unlimited access to entire stolen libraries. Some of these channels have accumulated tens of thousands of subscribers, generating significant monthly recurring revenue.
Discord servers serve a similar function, particularly for communities organized around specific niches — fitness coaching, financial education, software development. Stolen courses are shared as community resources, with the piracy framed as democratizing access to expensive education. This social framing significantly reduces the perceived illegitimacy of the activity among participants.
Dark web marketplaces represent the high-value end of the distribution spectrum, where bulk content libraries, compromised platform credentials, and wholesale access deals are transacted between larger operators.
3.2 — Pricing Tiers: How Stolen Courses Are Packaged & Sold
The pricing architecture of course piracy markets reveals how sophisticated these operations have become. Stolen content is not simply dumped at a single price point. It is tiered, bundled, and marketed with the same commercial logic as legitimate digital products.
| Product Tier | Description | Typical Price |
|---|---|---|
| Single Course Download | Individual high-value course | $5–$25 |
| Niche Bundle | 10–50 courses in a specific category | $15–$50 |
| Monthly Subscription | Unlimited access to full stolen library | $10–$30/month |
| Reseller License | Wholesale rights to resell specific content | $50–$200 |
| Premium Credentials | Active login credentials to legitimate platforms | $2–$15 per account |
🔴 Protect Your Content Before It Enters These Networks
Inkrypt Videos’ DRM encryption ensures your course content is locked at the source — making acquisition by piracy networks exponentially harder. Don’t wait until your content appears on a Telegram channel.
Visit inkryptvideos.com to see how Inkrypt Videos protects creators worldwide.
4. Credential Abuse — The Other Side of the Underground
4.1 — Account Sharing, Credential Stuffing & Login Reselling
Credential abuse represents a parallel revenue stream within the course piracy underground economy — one that operates independently of content theft but feeds the same distribution networks. Rather than stealing the content itself, credential abusers steal access to legitimate platform accounts, which are then resold or exploited to acquire content at scale.
Account sharing is the most common and widely underestimated form of credential abuse. Students sharing login credentials with non-paying peers directly erodes platform revenue while generating no detectable anomaly in standard analytics. More sophisticated operations coordinate credential stuffing attacks — automated systems that test millions of username/password combinations harvested from unrelated data breaches against e-learning platform login pages, exploiting the widespread habit of password reuse.
Successfully compromised credentials are sorted by platform value and sold in bulk. A verified active account on a premium course platform with a high-value subscription may sell for $10–$15 — a small price for the buyer, but multiplied across thousands of accounts, it represents significant revenue for the credential harvesting network and devastating losses for the platform.
4.2 — How Credential Networks Operate Alongside Piracy Markets
Credential networks and content piracy networks are not separate ecosystems. They are deeply integrated. Compromised platform accounts serve as the primary acquisition mechanism for new content entering piracy supply chains. A credential reseller supplying accounts to a content piracy network effectively operates as a supplier in that network’s supply chain, receiving ongoing payment for fresh account access as previous credentials are burned through platform security responses.
This integration means that defending against content piracy requires addressing credential abuse simultaneously. A platform that secures its content delivery but ignores credential security has closed one door while leaving another wide open.
5. Why Most Content Protection Fails Against These Networks
5.1 — Common DRM Weaknesses Exploited by Piracy Rings
The uncomfortable truth is that most content protection implementations currently deployed by individual creators and even mid-size platforms are wholly inadequate against organized piracy networks. These networks have developed systematic methods for defeating common protection approaches.
Basic video lock plugins that rely on JavaScript-based access control can be bypassed by anyone with basic browser developer tools knowledge. Static watermarking — embedding a fixed identifier into video content — is routinely defeated by cropping, color filter processing, or simply re-recording the screen at a slightly different zoom level. Platform-native DRM implementations on general hosting services are frequently undermined by the same credential compromise vectors described in Section 4.
Even screen recording, the most primitive form of content theft, remains effective against protection systems that focus exclusively on download prevention while ignoring screen capture. A pirated recording of a $2,000 coaching program captured through screen recording software is commercially indistinguishable from a direct download to the end buyer in an underground marketplace.
5.2 — The “False Security” Trap: Platform Reliance vs. Real Protection
Perhaps the most dangerous vulnerability in the content protection landscape is what security professionals call the false security trap — the false confidence that comes from having some protection in place, regardless of its actual effectiveness against real-world attack vectors.
Creators who upload to general-purpose video platforms with basic privacy settings, or who deploy entry-level course protection plugins, often believe their content is secured. It is not. These measures deter casual individual piracy but are transparent to organized networks with dedicated technical resources for defeating them.
Real protection requires military-grade DRM encryption that operates at the encoding level, dynamic watermarking that cannot be defeated by post-processing, and real-time anomaly detection that identifies credential abuse patterns before they result in content leakage.
🔴 Your Current Protection May Already Be Failing
Inkrypt Videos uses enterprise-grade DRM encryption combined with dynamic watermarking — the exact combination that organized piracy networks cannot defeat with standard bypass techniques. Speak with our content protection specialists today.
📞 804 500 2905 📍 1528 W Sunset Ave, Springdale, Arizona 72764 🌐 inkryptvideos.com
6. The Forensic Advantage — How Advanced Protection Breaks Piracy Networks
6.1 — Dynamic Watermarking as a Piracy Deterrent & Forensic Tool
Dynamic watermarking represents the most significant advancement in content protection technology for the specific threat profile of course piracy networks. Unlike static watermarks that embed a fixed identifier into video content, dynamic watermarks are generated uniquely for each viewing session — invisibly encoding the viewer’s identity, session timestamp, and access credentials directly into the video stream in real time.
The implications for piracy networks are profound. Every piece of content that leaves the platform carries an invisible forensic signature that survives screen recording, re-encoding, and standard post-processing attempts. When pirated content is discovered in an underground marketplace, the dynamic watermark identifies precisely which account was used to obtain it — enabling targeted legal action, account termination, and forensic evidence collection that supports DMCA enforcement and, in organized network cases, criminal prosecution.
This forensic capability does more than enable reactive enforcement. Its existence acts as a proactive deterrent. When piracy networks know that content from a particular platform carries traceable watermarks, that platform’s content becomes a significantly higher-risk acquisition target. Networks pivot to easier prey — creators whose content carries no forensic signature and whose losses will go permanently undetected.
6.2 — How Real-Time Analytics Expose Credential Abuse Patterns
Advanced content protection platforms do not merely secure delivery — they generate the intelligence data necessary to identify credential abuse before it escalates into full content leakage. Real-time analytics that monitor concurrent viewing sessions, geographic anomalies, device fingerprint inconsistencies, and abnormal access pattern velocities provide the early warning system that standard platform analytics completely lack.
A legitimate student in Chicago does not simultaneously access the same account from São Paulo and Bangkok within a two-hour window. An account that downloads every piece of content within 48 hours of purchase and then goes permanently dormant is exhibiting the behavioral signature of a credential-compromised acquisition account. These patterns are invisible to basic analytics but immediately apparent to purpose-built content security intelligence systems.
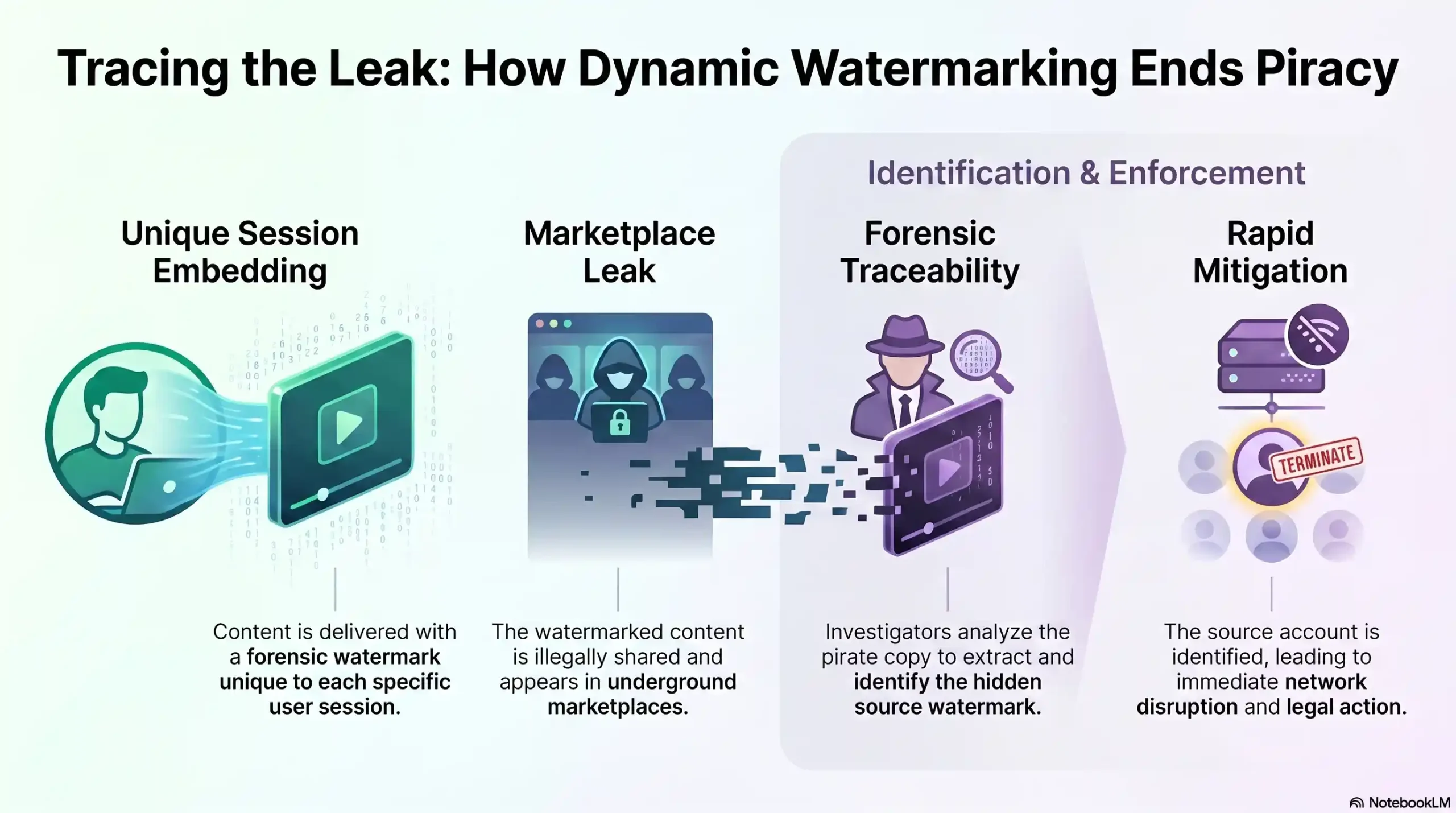
| Watermarking Stage | Action | Outcome |
|---|---|---|
| Content Delivery | Unique watermark embedded per session | Every view carries forensic identity |
| Piracy Detection | Content found in underground marketplace | Watermark survives re-encoding |
| Forensic Analysis | Watermark decoded by rights holder | Source account precisely identified |
| Enforcement Action | DMCA filing + account termination | Legal evidence chain established |
| Network Disruption | Piracy network avoids high-risk platform | Deterrence effect multiplies over time |
7. What Every Creator and Platform Must Do Right Now
7.1 — The 5-Layer Protection Framework for Course Creators
Defeating course piracy networks requires a layered defense strategy that addresses every stage of the piracy supply chain. No single technology is sufficient. The following five-layer framework represents the minimum viable protection posture for any creator whose revenue depends on premium digital content.
Layer 1 — DRM Encryption at Source: Content must be encrypted at the encoding level using enterprise-grade DRM standards (Widevine, PlayReady, FairPlay) that prevent direct file extraction regardless of the delivery method.
Layer 2 — Dynamic Watermarking: Every viewing session must carry a unique, invisible forensic identifier that survives post-processing and enables source attribution when content is discovered in piracy networks.
Layer 3 — Credential Security: Multi-factor authentication, concurrent session limits, device fingerprinting, and anomalous access detection must be deployed to close the credential abuse vector.
Layer 4 — Real-Time Analytics & Threat Intelligence: Continuous monitoring of access patterns, geographic anomalies, and download behaviors must generate actionable alerts before content leakage occurs.
Layer 5 — Legal Enforcement Infrastructure: DMCA takedown capability, forensic evidence collection, and relationships with specialized IP enforcement services must be in place to act on intelligence gathered by Layers 1–4.
7.2 — Choosing the Right Platform: Questions You Must Ask
Not all video hosting and content protection platforms are equal in their ability to defend against the threat profile described in this article. Before entrusting your content to any platform, demand clear answers to these questions:
Does the platform use Widevine or equivalent enterprise DRM, or is it relying on JavaScript access control? Does it offer dynamic watermarking, or only static identifiers? Can it provide real-time concurrent session monitoring? What is its DMCA enforcement process and how quickly can it act on piracy reports? Does it offer forensic tracking that produces legally admissible evidence? Is the platform’s CDN infrastructure capable of delivering securely at global scale without performance compromises that incentivize users to seek content through alternative channels?
These questions separate platforms that provide genuine protection from those that provide the false security trap described in Section 5.
🔗 Local Resources & Citations
1. U.S. Copyright Office — Digital Millennium Copyright Act (DMCA) The official U.S. government resource for understanding your legal rights under the DMCA, including how to file a takedown notice when your course content is found on piracy platforms or unauthorized distribution channels.
2. WIPO — World Intellectual Property Organization | Copyright in the Digital Environment The United Nations agency governing global intellectual property law — use this resource to understand how international copyright treaties protect your digital course content across all 193 member states worldwide.
3. INTERPOL — Cybercrime Division The international law enforcement body coordinating cross-border cybercrime investigations across 196 countries — reference this page to understand how organized digital piracy networks are tracked, disrupted, and prosecuted at a global scale.
4. National Intellectual Property Rights Coordination Center — IPR Center (.gov) The U.S. Department of Homeland Security’s dedicated IP enforcement center — use this resource to report large-scale course piracy operations and access government-backed intelligence on how criminal IP theft networks are dismantled.
🔴 Inkrypt Videos Delivers All 5 Layers Under One Platform
From Widevine DRM encryption to dynamic watermarking to real-time analytics — Inkrypt Videos was built specifically to defeat the piracy networks described in this article. Setup takes under 30 minutes.
📞 Call us: 804 500 2905 📍 1528 W Sunset Ave, Springdale, Arizona 72764 🌐 Visit: inkryptvideos.com
“Real security for real creators.”
Frequently Asked Questions
A course piracy network is an organized criminal ecosystem that systematically steals, repackages, and resells premium online courses and digital educational content through underground channels including dark web marketplaces, Telegram groups, and credential-sharing forums. Unlike casual individual piracy, these networks operate with defined roles, tiered pricing models, and distribution infrastructure designed to maximize revenue while evading legal action.
Course creators lose an estimated 15–20% of their annual revenue to piracy and unauthorized content distribution. For individual creators generating $200,000 per year, this translates to $30,000–$40,000 in silent annual losses. Across the global e-learning market — projected to exceed $400 billion by 2026 — total piracy-related losses are estimated at over $74 billion annually.
Piracy networks obtain premium course content through four primary methods: credential stuffing attacks that compromise legitimate platform accounts at scale, screen recording operations that capture content during playback, exploitation of platform security vulnerabilities, and the purchase of compromised login credentials from parallel credential theft networks. Once obtained, content is processed, rebranded, and distributed through tiered underground marketplaces.
Credential stuffing is an automated cyberattack in which stolen username and password combinations — harvested from unrelated data breaches — are systematically tested against e-learning platform login pages to exploit password reuse habits. Successfully compromised accounts are sold in underground marketplaces for $2–$15 each and used to access and extract premium course content at scale, feeding directly into course piracy distribution networks.
Basic DRM protection fails against organized piracy networks because it is designed to deter casual individual users, not technically resourceful criminal operations. JavaScript-based access controls are bypassed with standard browser tools, static watermarks are defeated through cropping and color processing, and platform-native security is undermined by credential compromise. Real protection requires enterprise-grade DRM encryption combined with dynamic watermarking that generates a unique forensic identifier for every individual viewing session.
Dynamic watermarking is a content protection technology that invisibly embeds a unique forensic identifier — including viewer identity, session timestamp, and access credentials — directly into each individual video stream in real time. Unlike static watermarks, dynamic watermarks survive screen recording and re-encoding, meaning that when pirated content is discovered in underground marketplaces, the watermark precisely identifies the source account. This forensic capability both enables targeted legal enforcement and deters piracy networks from targeting protected platforms.
Protecting online course content from piracy networks requires a five-layer defense strategy: enterprise-grade DRM encryption at the source, dynamic watermarking for forensic session tracking, credential security measures including multi-factor authentication and concurrent session limits, real-time analytics for anomaly detection, and DMCA enforcement infrastructure for rapid takedown action. Platforms like Inkrypt Videos deliver all five layers under a single integrated solution, purpose-built to defeat the threat profile of organized course piracy networks. Contact Inkrypt Videos at 804 500 2905 or visit inkryptvideos.com to get started.
It reduces sales and income for creators, forcing price hikes or less content production, though some argue it boosts awareness.
Free options like Khan Academy, edX audits, or YouTube abound. Libraries offer ebook loans too.
Yes, via plagiarism tools spotting shared homework or identical submissions from note-sharing sites.
Sites like CourseHero or torrent trackers lead, but they mix legit notes with illegal full courses.
Shifted to decentralized apps and crypto payments post-2020 crackdowns, evading traditional shutdowns.
Disclaimer:
This article is for educational and informational purposes only. It aims to raise awareness about digital piracy, cybersecurity risks, and content protection strategies. It does not promote, support, or encourage illegal activity, including unauthorized distribution or access to copyrighted material.

