Table of Contents
ToggleDoes HTTPS protect premium video content from piracy? HTTPS encrypts the connection between a server and a browser, protecting data in transit — but it does not protect video content after delivery. Once a stream reaches a viewer’s device, HTTPS has no control over screen recording, stream ripping, or credential sharing. Premium video protection requires Multi-DRM encryption, dynamic watermarking, and tokenized delivery working together.
Every online course creator, enterprise media company, and premium content publisher making the decision to host their video content online faces the same critical question: is my content actually protected? The instinctive answer is usually “yes — we have HTTPS.” And that answer, while partially correct, is dangerously incomplete.
HTTPS is not video security. It is channel security. Understanding that distinction is the difference between content that is genuinely protected and content that only feels protected — until the day it isn’t.
This guide breaks down exactly where HTTPS stops working, what real threats are waiting on the other side, and what a complete, enterprise-grade video security stack actually looks like in 2025.
What HTTPS Actually Does (And What It Doesn’t)
The Lock on the Front Door — Understanding Transport Layer Security
HTTPS — Hypertext Transfer Protocol Secure — is built on TLS (Transport Layer Security), a cryptographic protocol that creates an encrypted tunnel between a web server and a user’s browser. Think of it as a locked, armored truck transporting your video data from point A to point B. Nobody can intercept or tamper with the package while it’s in transit.
This is genuinely valuable. Without HTTPS, man-in-the-middle attacks could intercept unencrypted video streams mid-delivery, injecting malicious content or stealing session tokens. HTTPS eliminates that class of threat entirely, and for that reason, it is an absolute baseline requirement for any online content platform.
But here is where the metaphor breaks down entirely: the moment that armored truck arrives at its destination and the package is handed over, the truck drives away. Whatever happens next is no longer its concern.
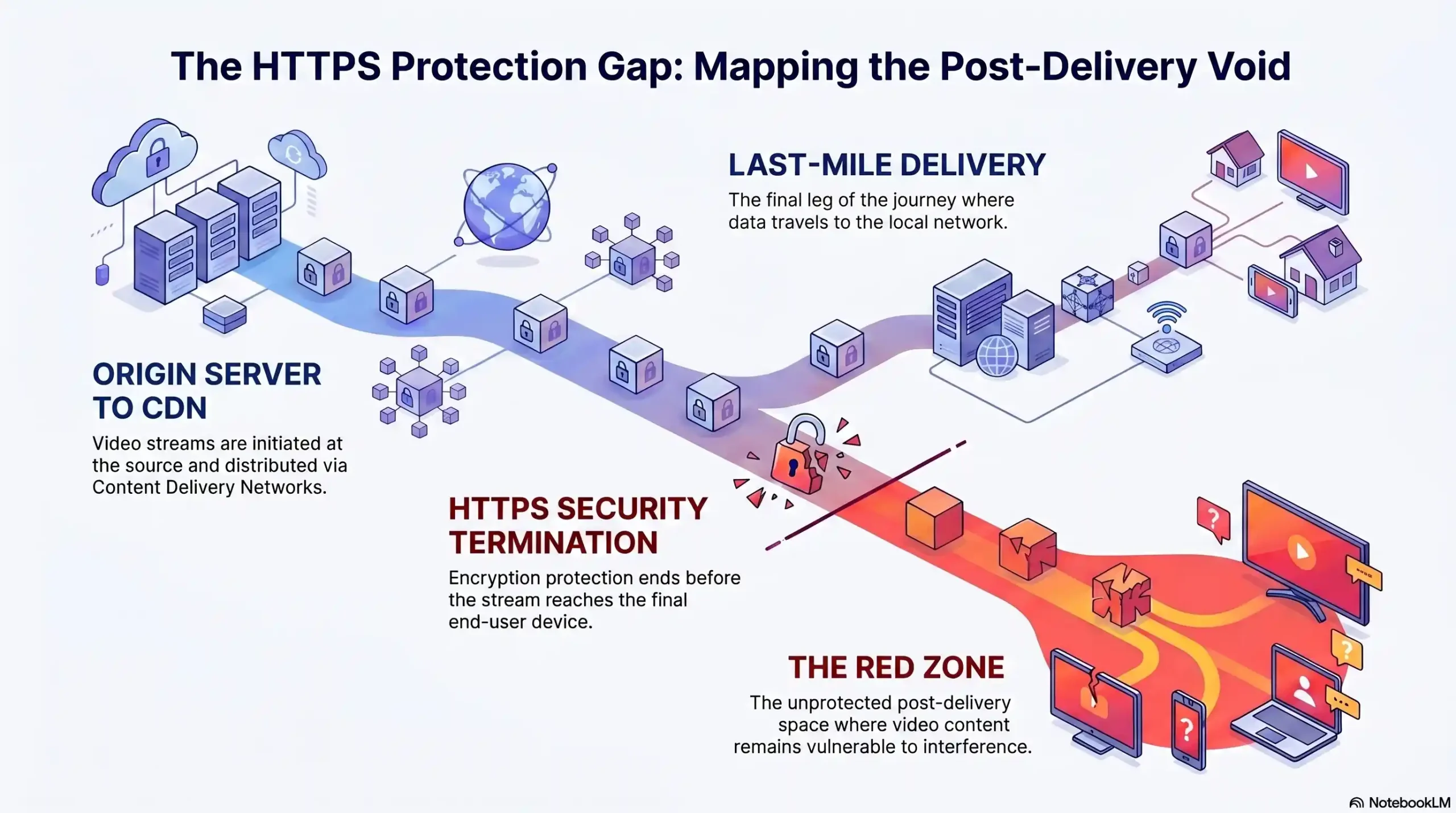
Where HTTPS’s Protection Ends: The Last-Mile Vulnerability
The “last mile” in video delivery is the space between your CDN edge server and the actual playback device — the laptop, phone, or smart TV in your viewer’s hands. HTTPS secures the journey. It has no authority over the destination.
Once your video stream is decrypted at the device level for playback — which it must be, or the user cannot watch it — it exists in a decrypted, accessible state. At that precise moment, HTTPS protection is functionally over. The content is now exposed to whatever tools or intentions the end user brings to that session.
The Three Threats HTTPS Was Never Designed to Stop
HTTPS was designed by engineers solving a specific problem: secure data transmission. It was never designed to address post-delivery content exploitation. The three threats it categorically cannot prevent are:
1. Content capture at the device level — screen recorders and stream rippers operate after decryption, where HTTPS has no jurisdiction.
2. Credential and link sharing — HTTPS authenticates the connection, not the identity or exclusivity of the viewer using it.
3. Unauthorized redistribution — once content is downloaded or captured, HTTPS has no mechanism to track, trace, or revoke it.
| Protection Layer | Threat Covered | HTTPS Covers? | DRM Required? |
|---|---|---|---|
| Data in Transit | Man-in-the-middle attack | ✅ Yes | ❌ No |
| Content at Device Level | Screen recording/ripping | ❌ No | ✅ Yes |
| Viewer Identity | Credential sharing | ❌ No | ✅ Yes |
| Post-Delivery Tracking | Unauthorized redistribution | ❌ No | ✅ Yes |
| Link Security | URL sharing/hijacking | ❌ No | ✅ Yes |
The Real Threat Landscape for Premium Video Content
Stream Ripping — The Silent Revenue Killer
Stream ripping tools — software designed to capture and download video streams during playback — are widely available, free, and require no technical expertise to operate. A course creator selling a $997 program can have their entire curriculum downloaded, redistributed on Telegram, and shared across piracy forums within hours of a single student gaining access.
The damage is rarely visible immediately. Enrollment numbers drop gradually. Refund requests increase. The creator assumes the market has shifted — when in reality, their content is circulating freely. Stream ripping is silent, scalable, and entirely invisible to HTTPS.
Screen Capture & Recording Tools: Impossible to Block Without DRM
Modern operating systems include native screen recording capabilities. Third-party applications add professional-grade capture with audio. Without DRM enforcement at the hardware level — specifically Widevine L1 on Android and PlayReady SL3000 on Windows — there is no technical mechanism within an HTTPS-only environment to prevent a viewer from recording your premium video content in full HD.
This is not a gap that can be patched with terms of service language or watermark overlays. It requires hardware-level DRM enforcement that instructs the device’s secure enclave to refuse rendering to screen capture APIs.
Credential Sharing & Link Hijacking
A single purchased account shared across twelve users is not a hypothetical — it is standard behavior among cost-conscious consumers. HTTPS authenticates the encrypted session, but it does not enforce viewer uniqueness, device limits, or geographic restrictions. One login can become thirty viewers without triggering a single HTTPS-level alert.
Link hijacking follows a similar pattern. A tokenless, unprotected video URL embedded in an HTTPS page can be extracted from browser developer tools in under sixty seconds and shared globally. HTTPS delivered that URL securely — and then stood by while it was weaponized.
Man-in-the-Middle Attacks Beyond the Browser
While HTTPS eliminates classical man-in-the-middle attacks at the network layer, sophisticated actors operating within enterprise environments — on corporate proxies, VPNs, or compromised routers with SSL inspection enabled — can intercept and inspect HTTPS traffic in ways that basic TLS implementations do not anticipate. For enterprise media companies handling high-value content, this represents a non-trivial attack surface that transport-layer security alone cannot close.
🎯 Concerned about what HTTPS is leaving exposed? Inkrypt Videos closes every one of these gaps with enterprise-grade DRM, forensic watermarking, and tokenized delivery. Reach our team directly at +971 544 077 967 to learn more.
HTTPS vs. AES-128 vs. Multi-DRM — What’s Actually Protecting Your Content?
AES-128 Encryption — A Step Up, But Still Not Enough
AES-128 (Advanced Encryption Standard with 128-bit keys) applied at the segment level — as used in HLS (HTTP Live Streaming) — is a meaningful improvement over unencrypted delivery. It encrypts individual video segments so that intercepted stream data cannot be played without the decryption key.
However, AES-128 in standard HLS implementations has a critical weakness: the decryption key is delivered to the player via a standard HTTPS request. A technically competent user can extract that key from browser memory or network traffic, decrypt the segments offline, and reconstruct the full video file. AES-128 raises the barrier — it does not eliminate the threat.
What Multi-DRM Actually Means (Widevine, PlayReady & FairPlay Explained)
Multi-DRM is the industry standard for genuine premium content protection, combining three proprietary DRM systems that cover virtually every device and browser combination:
| DRM System | Developer | Primary Coverage |
|---|---|---|
| Widevine | Chrome, Android, Chromecast, most Smart TVs | |
| PlayReady | Microsoft | Edge, Windows, Xbox |
| FairPlay | Apple | Safari, iOS, macOS, Apple TV |
Each system operates by storing decryption keys inside a hardware-secured enclave on the user’s device — the Trusted Execution Environment (TEE). The key never exists in accessible memory. The video content is decrypted inside the secure enclave and rendered directly to the display hardware, bypassing any software-level screen capture API entirely.
This is the architecture that Netflix, Disney+, and every major streaming platform deploys. It is the only technical solution that prevents both stream ripping and screen capture simultaneously.
The W3C Encrypted Media Extensions (EME) Standard — Why It Matters
The W3C Encrypted Media Extensions specification is the browser-level API that enables DRM playback within standard HTML5 video players — without requiring proprietary plugins. EME creates the standardized interface through which Widevine, PlayReady, and FairPlay operate inside Chrome, Edge, Safari, and Firefox. It is the architectural foundation that makes multi-DRM both platform-agnostic and scalable — exactly what enterprise content distributors require.
| Security Feature | HTTPS Only | AES-128 HLS | Multi-DRM |
|---|---|---|---|
| Encrypts data in transit | ✅ | ✅ | ✅ |
| Encrypts video segments | ❌ | ✅ | ✅ |
| Prevents stream ripping | ❌ | ⚠️ Partial | ✅ |
| Prevents screen capture | ❌ | ❌ | ✅ |
| Hardware-level key protection | ❌ | ❌ | ✅ |
| Forensic tracking capability | ❌ | ❌ | ✅ |
| Device & geo-restriction | ❌ | ❌ | ✅ |
Dynamic Watermarking — The Forensic Layer HTTPS Can Never Provide
What Is Dynamic Watermarking and How Does It Work?
Dynamic watermarking embeds a unique, invisible identifier into each individual stream at the moment of delivery — specific to the viewer, the session, the device, and the timestamp. Unlike static watermarks that are applied once to the master file, dynamic watermarks are generated in real time and woven into the video data itself, making them impossible to remove without visibly degrading the content.
Every viewer of an Inkrypt Videos-protected stream receives a uniquely fingerprinted version of that content. If that content appears on a piracy forum, torrent site, or Telegram channel, the watermark survives — and the leak is traceable back to its precise origin in minutes.
Forensic Watermarking vs. Visible Watermarking — Know the Difference
| Feature | Visible Watermark | Forensic Watermark |
|---|---|---|
| Visibility | Seen by viewer | Invisible to viewer |
| Purpose | Branding / deterrence | Forensic identification |
| Removability | Croppable / blurable | Survives encoding changes |
| Piracy Tracing | ❌ No | ✅ Yes — to individual user |
| Post-Leak Utility | Low | High — legal evidence grade |
Visible watermarks provide deterrence. Forensic watermarks provide accountability. For enterprise media companies and premium publishers, forensic-grade watermarking is the difference between suspecting a leak and proving it in a legal context.
Real-World Scenario: Tracing a Leak Back to the Source
Consider an enterprise media company that distributes a proprietary training series to 3,000 corporate accounts. Three weeks after launch, segments appear on a competitor’s internal platform. Without forensic watermarking, the investigation is a needle-in-a-haystack exercise with no guaranteed outcome.
With Inkrypt Videos dynamic watermarking, the recovered content carries its origin identifier. The leaking account is identified within hours. Access is revoked, legal proceedings are initiated with forensic-grade evidence, and the remaining 2,999 accounts are notified with zero disruption to service.
🎯 Forensic-grade watermarking is standard in every Inkrypt Videos deployment — not a premium add-on. Speak directly with our content security team: +971 544 077 967
Tokenized URLs & Signed Delivery — Closing the Link-Sharing Loophole
How Tokenized URLs Work in HLS and MPEG-DASH Streams
A tokenized URL is a dynamically generated, time-limited, cryptographically signed stream URL that is unique to each authorized playback session. Unlike a static video URL — which, once extracted, can be shared and accessed indefinitely — a tokenized URL expires after a defined window, is bound to a specific IP address or device fingerprint, and becomes invalid the moment the authorized session ends.
In HLS and MPEG-DASH streaming protocols, tokenization is applied at the manifest level, meaning every segment request within the stream carries authentication. Extracting a single segment URL provides no usable access to the stream as a whole.
Session-Bound Playback — Tying a Stream to One Authorized Viewer
Session-bound playback extends tokenization by linking the stream not just to a URL but to a validated, authenticated user session with enforced constraints — maximum concurrent streams per account, geographic IP validation, device fingerprint matching, and time-of-day access windows. A shared login that worked yesterday becomes non-functional the moment session binding detects anomalous concurrent access.
Amazon CDN + Token Authentication: The Infrastructure Behind Inkrypt Videos
Inkrypt Videos delivers all protected content via Amazon CloudFront CDN — one of the world’s largest and most performant content delivery networks — with token authentication enforced at the edge. This means every stream request is authenticated at the CDN level before a single byte of video data is delivered. Unauthorized requests are rejected at the infrastructure layer, not after delivery. The result is both maximum security and zero-latency performance for authorized viewers worldwide.
The True Cost of “Good Enough” Security — What Piracy Is Costing You Right Now
Revenue Loss Statistics for Online Course Creators
The global e-learning piracy problem is not a fringe issue. Industry estimates suggest that for every legitimate sale of premium educational content, between 1.5 and 3 unauthorized copies are in circulation. For a course creator generating $200,000 annually, this implies a potential revenue leakage of $100,000 to $300,000 per year — invisible, ongoing, and entirely preventable with the right security infrastructure.
The Reputational Damage of a Content Leak for Enterprise Media
For enterprise media companies, the cost of a content leak extends far beyond immediate revenue loss. A leaked pre-release film or proprietary training series damages distribution agreements, violates licensing contracts, and triggers liability clauses. The reputational signal to partners and investors — that the company cannot secure its own assets — can suppress deal-making for quarters after the incident is resolved.
Calculating Your Content’s Risk Exposure
| Audience Segment | Average Content Value | Piracy Risk Level | Estimated Annual Leakage |
|---|---|---|---|
| Online Course Creators | $500 – $5,000 per course | High | 30–60% of revenue potential |
| Enterprise Media Companies | $50K – $500K per title | Critical | $100K – $2M+ per incident |
| Premium Publishers | $10K – $100K per content library | High | 20–40% subscriber revenue |
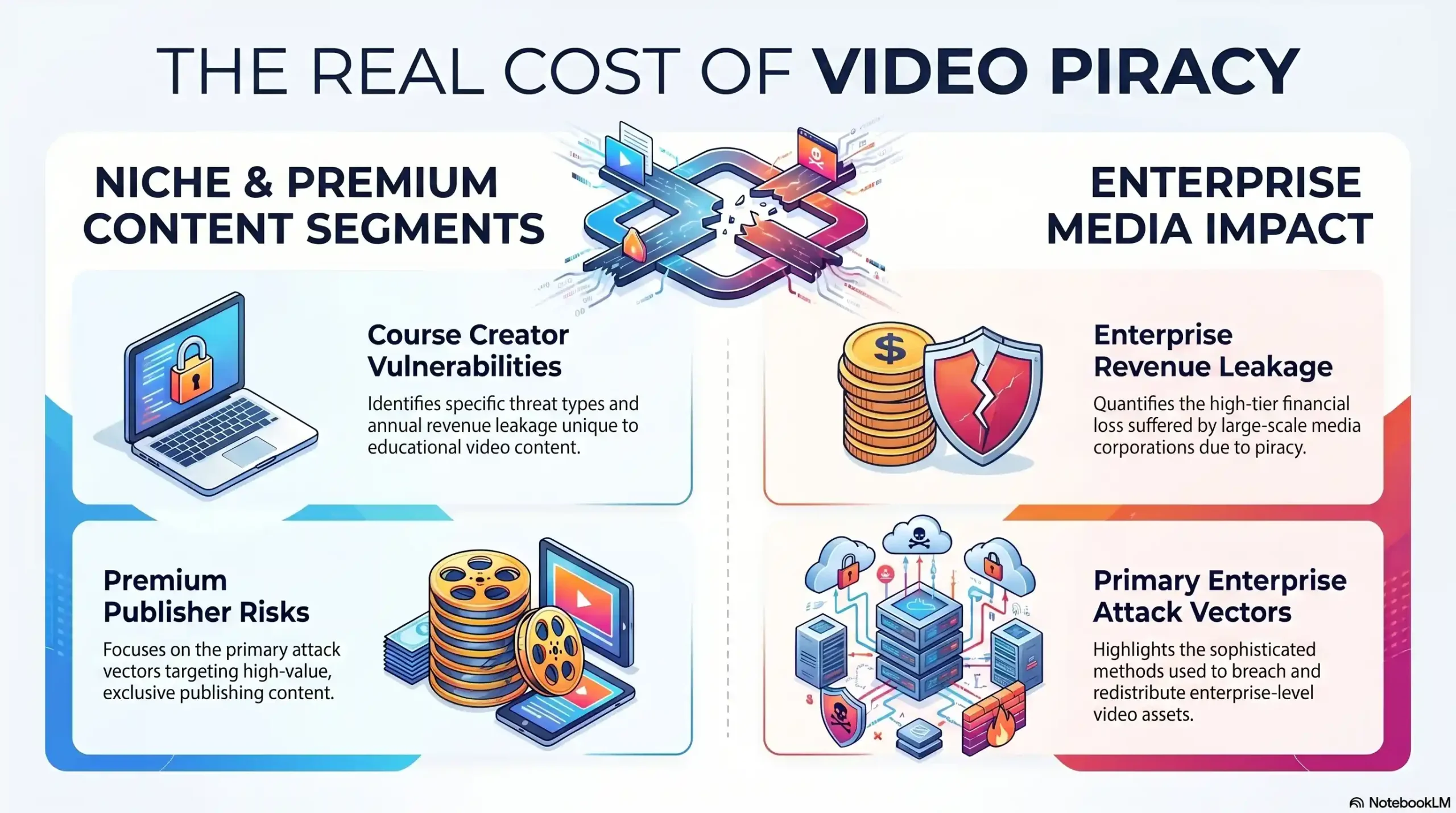
| Segment | Primary Threat | Revenue Impact | Recovery Time |
|---|---|---|---|
| Course Creators | Stream ripping & credential sharing | $100K–$300K/year | 6–18 months |
| Enterprise Media | Content leaks & DRM bypass | $100K–$2M+ per incident | 12–36 months |
| Premium Publishers | Credential sharing & link hijacking | 20–40% subscriber revenue | Ongoing |
What a Complete Video Security Stack Looks Like in 2025
Layer 1 — Transport Security (HTTPS/TLS — The Baseline)
The foundational layer. Mandatory, non-negotiable, and entirely insufficient on its own. Secures the delivery channel only.
Layer 2 — Content Encryption (AES-128 + Multi-DRM)
Encrypts video segments and protects decryption keys inside hardware-secured enclaves. Prevents stream ripping and screen capture at the OS level. Widevine, PlayReady, and FairPlay working in concert.
Layer 3 — Forensic Watermarking & Identity Tracking
Embeds unique, invisible identifiers per viewer session. Survives re-encoding and compression. Provides legal-grade evidence for breach investigation and prosecution.
Layer 4 — Tokenized Delivery & Session Management
Cryptographically signed, time-limited, session-bound URLs. Concurrent stream limits. Geographic and device-level access controls. Eliminates link sharing and credential abuse.
Layer 5 — Real-Time Analytics & Threat Intelligence
Continuous monitoring of playback sessions for anomalous behavior — unusual geographic access, concurrent session spikes, abnormal playback patterns. Threat signals are surfaced in real time, enabling immediate access revocation before damage escalates.
Why Inkrypt Videos Is the Complete Security Stack — Not Just Another Tool
30-Minute Setup vs. Weeks of Enterprise Configuration
Enterprise DRM implementations from legacy vendors routinely require weeks of developer time, custom SDK integration, and dedicated DevOps resources. Inkrypt Videos compresses that timeline to thirty minutes through purpose-built WordPress plugins, clean REST APIs, and a zero-configuration CDN architecture that arrives pre-integrated with Amazon CloudFront. Security that is too complex to implement is security that never gets implemented.
Global Delivery via Amazon CDN — Zero Buffering, Maximum Protection
Content protection that degrades playback performance is a false trade-off that Inkrypt Videos refuses to accept. By routing all protected streams through Amazon CloudFront’s global edge network — 400+ points of presence across 90+ countries — Inkrypt Videos delivers DRM-encrypted content with the same load performance as unprotected streams. Your viewers in Cairo, São Paulo, or Seoul experience zero buffering. Your content remains protected at every edge node.
Universal Device Compatibility — No Viewer Left Behind
Legacy DRM implementations frequently break on older devices, obscure browsers, or non-standard operating systems — creating support burdens and viewer churn. Inkrypt Videos maintains full playback compatibility across all modern and legacy device categories, ensuring that your security infrastructure never becomes a barrier to your audience’s access.
🏛️ Local Resources & Citations
1. W3C — Encrypted Media Extensions (EME) Specification The official W3C standard that defines how browsers communicate with DRM systems like Widevine, PlayReady, and FairPlay — reference this to verify the technical architecture behind Multi-DRM playback described in the article.
2. NIST — Cybersecurity Framework 2.0 (CSF 2.0) The U.S. government’s official cybersecurity risk management framework — reference this to validate the layered security stack approach recommended in the article, particularly the Protect and Detect functions that align directly with DRM and forensic watermarking strategies.
3. WIPO — Copyright & Internet Treaties (WCT & WPPT) The UN’s World Intellectual Property Organization governs the international legal framework that protects digital content from unauthorized access and distribution — reference this for the global legal basis underpinning content protection rights that DRM enforces technically.
4. IETF — RFC 8446: TLS 1.3 Official Protocol Specification The Internet Engineering Task Force’s official specification for TLS 1.3 — the protocol that powers HTTPS — reference this to demonstrate precisely what TLS was designed to do (and not do), directly supporting the article’s core argument that HTTPS is a transport-layer tool only.
Conclusion — Real Security for Real Creators
HTTPS is not your enemy — it is simply not your solution. It was built for a different problem, and asking it to protect premium video content from post-delivery exploitation is like asking a postal service to prevent someone from photocopying a letter after it’s been delivered. The transport was secure. The destination was not.
Real content protection in 2025 requires a layered, forensic-grade security architecture: Multi-DRM encryption at the hardware level, dynamic watermarking that survives redistribution, tokenized delivery that eliminates link sharing, and real-time analytics that detect threats before they become incidents.
That architecture exists. It is live, it is deployable in thirty minutes, and it is built for creators and enterprises who understand that their content is not just media — it is their business.
Inkrypt Videos. Real security for real creators.
🎯 Every layer of the complete video security stack is live inside Inkrypt Videos — deployed in thirty minutes, operating worldwide. Start protecting your premium content today. 📞 Call: +971 544 077 967 🌐 Visit: inkryptvideos.com
Frequently Asked Questions
No, HTTPS alone is not enough to protect video content from piracy. HTTPS encrypts the connection between a server and a viewer’s browser — securing data in transit only. Once a video stream is delivered and decrypted at the device level for playback, HTTPS has no control over screen recording, stream ripping, or unauthorized redistribution. Premium video protection requires Multi-DRM encryption working alongside tokenized delivery and forensic watermarking
HTTPS and DRM protect video content at completely different layers. HTTPS secures the delivery channel — encrypting data as it travels from server to browser. DRM (Digital Rights Management) secures the content itself — controlling how video is decrypted, rendered, and accessed at the device level. A complete video security strategy requires both: HTTPS for transport security and Multi-DRM for content protection
AES-128 is a segment-level encryption standard used in HLS video streaming that encrypts individual video chunks during delivery. While it is significantly stronger than HTTPS-only protection, AES-128 alone is insufficient for premium content because its decryption keys can be extracted from browser memory by technically skilled users. Full Multi-DRM protection — storing keys inside a hardware-secured enclave — is required to close this gap
Dynamic watermarking embeds a unique, invisible identifier into each viewer’s video stream at the moment of delivery — tied to their account, session, device, and timestamp. Unlike visible watermarks that can be cropped or blurred, dynamic watermarks survive re-encoding and compression. If watermarked content appears on a piracy platform, the leak is traceable back to its precise source, providing legal-grade forensic evidence
Tokenized URLs are cryptographically signed, time-limited stream links that are unique to each authorized playback session. Unlike static video URLs — which can be extracted from a browser and shared indefinitely — tokenized URLs expire after a defined window and are bound to a specific device or IP address. Once the authorized session ends, the URL becomes permanently invalid, eliminating link-sharing and unauthorized redistribution
The three industry-standard DRM systems for premium video protection are Widevine (Google — covering Chrome, Android, and most Smart TVs), PlayReady (Microsoft — covering Edge, Windows, and Xbox), and FairPlay (Apple — covering Safari, iOS, macOS, and Apple TV). Together, these three systems form a Multi-DRM architecture that provides hardware-level content protection across virtually every device and browser combination
Preventing screen recording of online course content requires hardware-level DRM enforcement — specifically Widevine L1 on Android devices and PlayReady SL3000 on Windows. These DRM systems instruct the device’s secure enclave to decrypt and render video in a protected environment that screen capture APIs cannot access. No software-only solution, watermark overlay, or terms-of-service restriction can reliably prevent screen recording without DRM at the hardware level
HDCP encrypts HDMI signals between devices, enforcing DRM for high-value content like 4K HDR. It blocks unprotected displays or recorders.
Yes, use AES with signed URLs on CloudFront or S3. Add DRM for stronger protection against external access.
HLS AES-128 keys can be extracted from manifests, allowing offline decryption. Pair with DRM to secure keys.
Widevine uses hardware-backed keys and license servers to verify devices before decryption. It blocks software-only attacks.
RTMPS adds TLS to RTMP for ingest security, but playback needs AES/DRM. HTTPS suits adaptive streaming like HLS.
Disclaimer: The information provided in this guide is intended for educational and informational purposes only. While enterprise-grade DRM, dynamic watermarking, and tokenized delivery represent the industry standard for protecting premium video content, no digital security infrastructure is entirely impenetrable. Threat landscapes evolve rapidly, and content publishers should continually assess their unique risk profiles and technical requirements when implementing a comprehensive content protection strategy.