Table of Contents
ToggleWhat is CDN Security Configuration? CDN security configuration is the process of applying protective layers — including token authentication, geo-restrictions, origin shielding, and encryption — to a Content Delivery Network to prevent unauthorized access, hotlinking, and content leaks. For video platforms and online course creators, a properly configured CDN is the difference between a secure, revenue-generating content library and one that is actively being stolen. Inkrypt Videos delivers enterprise-grade CDN security with a 30-minute setup, combining Amazon CDN performance with military-grade content protection.
You built something valuable. Hundreds of hours of premium video content — courses, masterclasses, training modules, or exclusive media — hosted on a platform you trust. But if your CDN security configuration is weak, incomplete, or simply default, that content is not protected. It is exposed.
Every day, misconfigured CDNs silently bleed revenue for content creators and enterprises worldwide. Hotlinked videos. Bypassed tokens. Geo-spoofed streams. Direct origin access. The attack vectors are real, they are active, and most platforms have no idea they are being exploited until the damage is already done.
This guide gives you the exact framework to configure CDN security correctly — so your content reaches every legitimate viewer worldwide, and nobody else.
Why CDN Security Is the #1 Threat to Your Video Revenue
Most content creators focus their security efforts on passwords and login pages. That is the wrong battlefield. The real vulnerability sits deeper — inside the delivery infrastructure itself. Your CDN is the highway your video content travels on. If that highway has no checkpoints, anyone can get on.
A single misconfigured CDN setting can expose your entire video library to unauthorized access, regardless of how strong your platform login is. Attackers do not need your password. They need your URL.
The Real Cost of a Content Leak
The numbers are not abstract. The global video piracy market costs the industry an estimated $71 billion annually, with online course piracy and unauthorized streaming accounting for a rapidly growing share. For individual creators, a single leaked course can represent thousands of dollars in lost enrollments within days of publication.
Beyond direct revenue loss, content leaks destroy competitive advantage. Your proprietary methodology, your teaching style, your premium media — once leaked, it becomes free content on piracy forums, Telegram channels, and torrent sites. Credential sharing compounds the problem further, with studies showing that up to 73% of streaming subscribers have shared login access with someone outside their household.
The entry point for most of these breaches is not a sophisticated cyberattack. It is a CDN that was never properly configured in the first place.
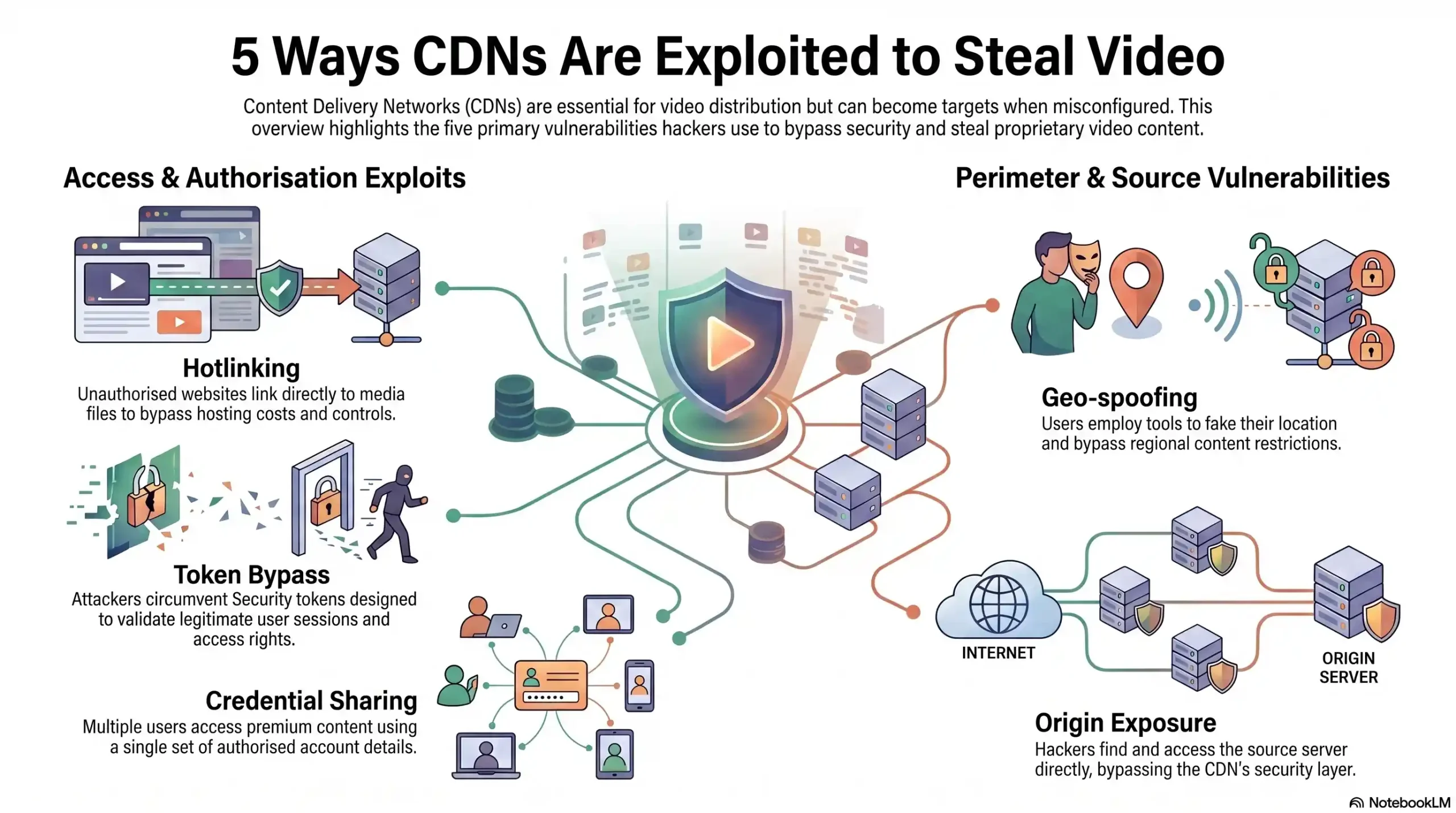
| Attack Vector | Method | Risk Level |
|---|---|---|
| Hotlinking | Direct URL embedding on external sites | 🔴 Critical |
| Token Bypass | Exploiting unsigned or expired tokens | 🔴 Critical |
| Geo-Spoofing | VPN masking to bypass geo-restrictions | 🟠 High |
| Origin Exposure | Direct origin server access bypassing CDN | 🔴 Critical |
| Credential Sharing | Multi-user login on single account | 🟠 High |
The 6 Pillars of a Bulletproof CDN Security Configuration
Securing your CDN is not a single switch you flip. It is a layered architecture — six interlocking pillars that, when configured correctly, create an environment where content leaks become structurally impossible rather than just unlikely.
Pillar 1 — Signed URLs & Token Authentication
Signed URLs are the foundation of CDN access control. Instead of generating a static, permanent link to your video content — which can be copied, shared, and accessed indefinitely — token authentication generates a unique, time-limited URL for each authorized viewing session.
When a verified user requests your video, the system generates a cryptographically signed URL that expires after a defined window, typically between 30 seconds and a few hours depending on your configuration. If that URL is copied and shared, it is already dead. No valid token, no access.
Inkrypt Videos implements dynamic token authentication at the CDN layer, meaning every video request is individually validated before a single frame is delivered. This eliminates hotlinking and unauthorized URL sharing at the infrastructure level.
Pillar 2 — Hotlink Protection & Referrer Validation
Hotlinking occurs when an external website or application embeds your video URL directly, consuming your CDN bandwidth and serving your content to their audience without authorization. Without referrer validation, your content can be broadcast from any domain on the internet.
Referrer-based hotlink protection restricts video playback exclusively to your whitelisted domains. A video hosted on your platform will only play when the request originates from your approved domain list. Any attempt to embed or access the content from an unauthorized domain returns an immediate block.
This is particularly critical for online course creators whose content is frequently targeted for embedding on piracy aggregator sites.
Pillar 3 — Geo-Restriction & IP Whitelisting
Geo-restriction allows you to define exactly which countries or regions are authorized to access your content. For enterprises managing licensing agreements, regional compliance requirements, or market-specific content strategies, geo-restriction is not optional — it is a legal necessity.
From a piracy prevention perspective, geo-restrictions combined with IP whitelisting create a geographic perimeter around your content. When integrated with VPN detection capabilities, this pillar also addresses the growing challenge of geo-spoofing, where users mask their true location to bypass regional access controls.
Inkrypt Videos supports granular geo-restriction configuration, allowing creators to whitelist specific countries, blacklist high-risk regions, and apply different access rules to different content libraries simultaneously.
Pillar 4 — Origin Shield & Direct Access Blocking
Your CDN edge network is your content’s public-facing delivery layer. Your origin server — where the master video files actually live — should never be publicly accessible. Origin exposure is one of the most dangerous and most commonly overlooked CDN security vulnerabilities.
An origin shield acts as an additional caching and protection layer between the CDN edge and your origin server, masking the origin’s true IP address and ensuring all traffic is routed exclusively through the CDN. Direct access blocking then enforces that the origin server will only respond to requests from authorized CDN nodes, rejecting all other traffic entirely.
Without this configuration, a technically motivated attacker can bypass your entire CDN security stack by accessing your origin server directly, rendering every other security measure irrelevant.
Pillar 5 — End-to-End Encryption & HTTPS Enforcement
Transmitting video content over unencrypted HTTP connections is a critical security failure. Every video stream must be delivered over HTTPS with enforced TLS encryption, ensuring that content cannot be intercepted, inspected, or captured in transit.
End-to-end encryption means the content is protected from the moment it leaves your origin server to the moment it renders in your viewer’s browser or app. This is especially important for enterprise clients operating in regulated industries — healthcare training content, financial services onboarding, and government agency materials all carry compliance requirements that mandate encrypted content delivery.
Inkrypt Videos enforces HTTPS across all delivery endpoints by default, with no configuration required from the user — it is the baseline, not an add-on.
Pillar 6 — Dynamic Watermarking as a Security Layer
Traditional watermarks are static — a logo burned into the corner of the video that determined pirates simply crop out. Dynamic watermarking is fundamentally different, and it is one of Inkrypt Videos’ most powerful proprietary security tools.
Dynamic watermarks embed invisible, session-specific identifiers directly into the video stream for each individual viewing session. If a user records their screen and distributes that recording, the watermark travels with it — carrying the exact user ID, timestamp, IP address, and session data of the person who leaked it. This transforms your content security from reactive to forensic.
For enterprise clients and premium content publishers, dynamic watermarking is not just a deterrent. It is an evidence-gathering system that makes every content leak fully traceable back to its source.
🎯 Ready to See All 6 Security Pillars in Action?
Discover how Inkrypt Videos configures every layer automatically — so your content is protected before your first video goes live. 👉 Request Your Free Inkrypt Videos Demo Today
How to Configure CDN Security for Video in 30 Minutes — Step-by-Step
Most enterprise CDN security configurations take weeks to implement. Inkrypt Videos was built on the principle that uncompromising security should not require an engineering team or a month-long onboarding process. Here is how the full configuration works in five steps.
Step 1 — Connect Your Video Library to the CDN
Begin by uploading your video content to the Inkrypt Videos platform or connecting your existing video library via the API or WordPress plugin. The platform automatically routes all content through Amazon CDN’s global edge network, distributing your files across multiple geographic nodes for zero-buffering worldwide delivery from the moment of upload.
Step 2 — Enable Token Authentication & Set Expiry Rules
Inside the Inkrypt Videos dashboard, navigate to the security configuration panel and activate signed URL token authentication. Define your token expiry window based on your content type — shorter windows for high-value premium content, longer windows for lower-risk materials. The system handles cryptographic signing automatically, requiring no manual URL generation on your end.
Step 3 — Configure Geo-Restrictions & Domain Whitelisting
Select your authorized delivery regions from the geo-restriction map and input your approved domain list for hotlink protection. For course creators, this typically means whitelisting your course platform domain. For enterprises, this may include multiple owned domains and partner distribution channels. Changes apply globally across all CDN edge nodes within minutes.
Step 4 — Activate Origin Shield & Block Direct Access
Enable origin shield protection from the advanced security settings panel. Inkrypt Videos automatically masks your origin server address and configures CDN-only access rules, ensuring your master video files are never directly reachable from the public internet. This step requires zero server-side configuration from the user — the platform handles origin isolation entirely.
Step 5 — Enable Dynamic Watermarking & Analytics Tracking
Activate dynamic watermarking to begin embedding invisible, session-specific identifiers into every video stream. Simultaneously, enable real-time analytics to begin tracking viewer engagement, geographic distribution, access patterns, and any anomalous activity that may indicate unauthorized access attempts. Your content is now fully protected and fully monitored.
🎯 Your Content Is Ready. Is Your Security?
Configure enterprise-grade CDN security for your entire video library in 30 minutes or less. 👉 Start Your Free Inkrypt Videos Trial — No Credit Card Required
CDN Security Configuration Checklist for Content Creators & Enterprises
Before launching any video content publicly, run through this pre-launch security checklist to confirm every critical CDN security layer is active and correctly configured.
Pre-Launch CDN Security Checklist
| Security Layer | Configuration Item | Status |
|---|---|---|
| Token Authentication | Signed URLs enabled with defined expiry windows | ✅ |
| Hotlink Protection | Domain whitelist configured, referrer validation active | ✅ |
| Geo-Restriction | Authorized regions defined, blocked regions enforced | ✅ |
| Origin Shield | Origin IP masked, CDN-only access enforced | ✅ |
| HTTPS Enforcement | All delivery endpoints on TLS encryption | ✅ |
| Dynamic Watermarking | Session-specific watermarks active on all streams | ✅ |
| Analytics Monitoring | Real-time access tracking and anomaly alerts enabled | ✅ |
| Credential Protection | Single-session or device-limit rules configured | ✅ |
If any item in this checklist is unconfigured, your content has an exploitable vulnerability. Every row matters.

| Security Layer | Technology | Inkrypt Feature |
|---|---|---|
| Origin Protection | Origin Shield | ✅ Built-in |
| Access Control | Signed URLs / Token Auth | ✅ Built-in |
| Regional Control | Geo-Restriction | ✅ Built-in |
| Identity Tracking | Dynamic Watermarking | ✅ Proprietary |
| Delivery Encryption | HTTPS / TLS | ✅ Built-in |
| Threat Intelligence | Real-Time Analytics | ✅ Built-in |
Why Global Delivery Doesn’t Have to Mean Global Risk
There is a persistent myth in the content security space that performance and security exist in tension — that locking down your content means slowing it down. This tradeoff is outdated, and it has never been true for platforms built correctly from the ground up.
How Inkrypt Videos Combines Amazon CDN Speed With Fortress-Level Security
Inkrypt Videos is built on Amazon CDN’s global edge infrastructure, distributing content across a worldwide network of delivery nodes that serve video from the location physically closest to each viewer. The result is sub-second load times and zero-buffering playback regardless of whether your audience is in New York, Nairobi, or New Delhi.
Critically, every security layer — token authentication, geo-restriction, origin shielding, dynamic watermarking, and HTTPS enforcement — operates at the CDN edge level. Security processing does not add latency to the viewer experience because it happens at the infrastructure layer, not the application layer. Your viewers get a seamless, professional streaming experience. Unauthorized users get nothing.
This is the architecture that enterprise OTT platforms and global media companies pay hundreds of thousands of dollars to build independently. Inkrypt Videos delivers the identical security and performance stack to individual course creators and growing media businesses — configured in 30 minutes, not 30 weeks.
🔗 Local Resources & Authoritative Citations
1. NIST Computer Security Resource Center — CDN & Encryption Guidelines (U.S. Government — .gov) The U.S. National Institute of Standards and Technology publishes the definitive federal frameworks for CDN security, TLS encryption standards, and access control — reference this resource to verify that your video security configuration aligns with globally recognized government-grade cybersecurity benchmarks.
2. NIST Cybersecurity Framework (CSF 2.0) (U.S. Government — .gov) NIST develops cybersecurity standards, guidelines, best practices, and resources to meet the needs of U.S. industry, federal agencies, and the broader public — use this framework to evaluate whether your content delivery infrastructure covers all five core security functions: Identify, Protect, Detect, Respond, and Recover.
3. IETF RFC 8446 — TLS 1.3 Official Encryption Standard (Internet Engineering Task Force) The Internet Engineering Task Force’s TLS 1.3 protocol allows client/server applications to communicate over the internet in a way designed to prevent eavesdropping, tampering, and message forgery — this is the official technical specification behind the HTTPS encryption that every secure CDN video stream must implement.
4. WIPO Internet Treaties — Digital Content Protection (United Nations Agency) WIPO administers the WIPO Copyright Treaty and the WIPO Performances and Phonogram Treaty, which set down international norms aimed at preventing unauthorized access to and use of creative works on the Internet or other digital networks — reference this resource to understand the international legal framework that makes DRM enforcement and anti-piracy measures legally binding across 115+ countries worldwide.
🎯 Your Content Built Your Business. Don’t Let a Misconfigured CDN Tear It Down.
Join thousands of creators and enterprises who trust Inkrypt Videos to protect and deliver their premium content worldwide — with zero compromise on speed or security. 👉 Start Your Free Inkrypt Videos Trial Today — Full Security Stack Included
Frequently Asked Questions About CDN Security Configuration
CDN security configuration is the process of applying protective layers — including token authentication, signed URLs, geo-restrictions, origin shielding, and end-to-end encryption — to a Content Delivery Network. For video platforms, it determines whether your content reaches only paying, authorized viewers or becomes vulnerable to hotlinking, piracy, and unauthorized redistribution.
Without a properly configured CDN, your video library is technically accessible to anyone who can obtain or guess a direct URL — regardless of how secure your login page is. CDN security closes the delivery-layer gap that platform-level passwords cannot address, making it the most critical and most overlooked layer of video content protection.
To prevent content leaks through your CDN, you must implement five core configurations: enable signed URL token authentication with short expiry windows, activate hotlink protection with domain whitelisting, configure geo-restrictions for your target regions, shield your origin server from direct public access, and enforce HTTPS encryption across all delivery endpoints.
Each of these layers closes a specific attack vector. Token authentication prevents URL sharing. Hotlink protection blocks unauthorized embedding. Geo-restrictions stop regional bypasses. Origin shielding prevents direct server access. HTTPS prevents in-transit interception. Inkrypt Videos applies all five configurations automatically within a single 30-minute setup, eliminating the need for manual CDN engineering.
Standard CDN delivery prioritizes speed and global distribution, routing content through edge servers worldwide for fast load times. Secure CDN delivery adds access control, encryption, and identity verification layers on top of that performance infrastructure — ensuring content reaches only authorized users while maintaining zero-buffering delivery speeds.
The practical difference is significant. A standard CDN serves your video to anyone with the URL. A secure CDN — like the infrastructure powering Inkrypt Videos — validates every request against token authentication rules, referrer whitelists, geo-permissions, and encryption standards before delivering a single frame. Performance and security are not in conflict when the architecture is built correctly from the start.
Dynamic watermarking embeds invisible, session-specific identifiers into each individual video stream at the point of delivery. Unlike static watermarks, which are fixed overlays that can be cropped or edited out, dynamic watermarks are woven into the video data itself — carrying unique viewer information including user ID, IP address, timestamp, and session details.
If a viewer records their screen and distributes the recording, the dynamic watermark travels with that content permanently. Rights holders can use the embedded data to forensically identify the exact source of the leak — making dynamic watermarking both a powerful piracy deterrent and an evidence-gathering tool for legal action. Inkrypt Videos applies dynamic watermarking at the CDN layer, meaning it activates automatically on every stream without any manual per-video configuration.
No. When CDN security is implemented at the infrastructure level — rather than the application layer — it adds no measurable latency to video delivery. Security processing such as token validation, geo-checks, and encryption enforcement happens at the CDN edge node, which is the same point where delivery speed is optimized.
Inkrypt Videos is built on Amazon CDN’s global edge network, meaning security and performance operate simultaneously at every delivery point worldwide. Viewers experience sub-second load times and zero-buffering playback regardless of their geographic location, while every security layer remains fully active. The myth that security compromises speed applies only to poorly architected solutions — not to platforms engineered with both priorities from the ground up.
Yes. Online course creators are among the most frequently targeted victims of video piracy precisely because their content is high-value, often sold at premium price points, and historically hosted on platforms with inadequate delivery-layer security. A single leaked course can circulate on piracy forums, Telegram channels, and torrent sites within hours of publication.
Enterprise-grade CDN security is no longer exclusive to large media companies. Inkrypt Videos was specifically built to give individual course creators and coaching businesses access to the same DRM encryption, dynamic watermarking, token authentication, and forensic tracking capabilities used by global OTT platforms — at a price point and setup complexity designed for creators, not enterprise IT departments.
With Inkrypt Videos, a complete CDN security configuration — including token authentication, hotlink protection, geo-restrictions, origin shielding, dynamic watermarking, and HTTPS enforcement — can be fully activated in 30 minutes or less. No engineering team, no server-side configuration, and no technical expertise is required.
The platform connects to your existing video library via API, WordPress plugin, or direct upload, and applies the full security stack automatically through a guided dashboard setup. For course creators migrating from unsecured platforms, the transition requires no downtime and no disruption to existing student access.
Yes, DNS leaks reveal origin IPs, allowing direct attacks that evade edge security—hide IPs and use authenticated pulls.
No, WAF blocks app-layer threats but pair it with DDoS mitigation, bot detection, and origin lockdown for full protection.
Signed URLs add expiring cryptographic tokens; CDN validates before serving, blocking shared or leaked links effectively.
HSTS forces HTTPS, blocks downgrade attacks, and prevents MITM on global deliveries—enable with proper max-age rollout.
Full logs detect subtle abuses like credential stuffing; avoid sampling to catch short bursts and map shadow APIs.
Disclaimer:
The information provided in this article is for educational and informational purposes only. While the security architectures and best practices discussed are designed to mitigate risks and prevent unauthorized access, no digital infrastructure can be guaranteed to be 100% secure against all potential threats. Organizations and creators should regularly review their security configurations and consult with cybersecurity professionals to ensure compliance with their specific legal and regional requirements.

