Table of Contents
TogglePicture this: You’ve just discovered your premium training course—the one that took six months to create and represents 40% of your annual revenue—is being distributed for free on a piracy site with 50,000 downloads. This scenario plays out hundreds of times daily across American businesses, from solo course creators to Fortune 500 companies.
The digital content security landscape has fundamentally shifted, and US businesses face unique challenges that generic cybersecurity advice simply doesn’t address.
The $50+ Billion US Content Security Crisis: Why Traditional Protection Fails
Digital content theft costs US businesses over $50 billion annually, with American companies experiencing 40% more security breaches than the global average. The United States accounts for 13.8% of all global visits to piracy sites while hosting the world’s largest concentration of premium content creators and enterprise publishers.
Geographic Vulnerability Patterns
Content security incidents follow distinct patterns across US states:
- California: 31% of total US creator security incidents, with average losses of $47,000 per creator annually
- Texas: 18% of incidents, particularly vulnerable to cross-border content theft affecting business and fitness creators
- New York: 15% of incidents, concentrated in financial services training materials
- Florida: Disproportionately high rates relative to creator population, with specialized piracy networks targeting wellness content

A Chicago-based corporate training company lost $2.3 million in 2024 when proprietary sales methodology courses were stolen and redistributed. The impact cascaded through reduced hiring, delayed product development, and affected their entire network of 200+ freelance instructors.
Why International Solutions Miss US Market Realities
Most content security providers optimize for global markets, creating critical gaps:
- Infrastructure misalignment: Response times optimized for non-US business hours
- Regulatory blind spots: Limited DMCA expertise and state privacy law understanding
- Cultural disconnect: Underestimating American user experience expectations
When evaluating current security, assess whether your provider maintains US data centers, offers DMCA-compliant processes, and demonstrates American regulatory expertise.
AI vs. AI: How Artificial Intelligence Transforms Content Theft and Protection
Artificial intelligence has fundamentally changed content theft, with 73% of US content piracy now involving AI-powered tools that bypass traditional security measures. What required technical expertise in 2023 became accessible to anyone with basic computer skills by late 2024.
The New AI Threat Landscape
AI-Powered Theft Techniques:
- Screen Recording Bypasses: AI analyzes DRM patterns and automatically adjusts recording parameters
- Watermark Removal: Machine learning removes forensic watermarks with 94% success rates
- Synthetic Content Recreation: AI recreates original content with modifications to avoid detection
Geographic AI Attack Patterns:
- West Coast: 67% higher rate of synthetic content recreation attacks
- Southwest: Cross-border AI-powered distribution networks
- Southeast: AI-enhanced social engineering targeting individual creators
- Northeast: Sophisticated corporate content theft using AI automation
When to Replace Your Current Security
Immediate Replacement Required:
- Screen recording bypasses occurring weekly
- DRM implementation predates 2022
- No behavioral analytics capabilities
- Cannot integrate AI-powered threat detection
- Provider lacks AI security expertise
Repair May Be Sufficient:
- Implementation less than 18 months old
- Behavioral analytics already integrated
- Fewer than 3 security incidents in 12 months
- Annual security budget exceeds $50,000
ROI Framework for AI Security
Traditional content theft remediation costs $320,000-2.925 million per incident, while AI-powered security costs $39,000-255,000 annually. For businesses with content valued above $500,000 annually, AI security typically delivers 300-700% ROI within the first year.
The Creator Economy Under Attack: Platform Vulnerabilities Expose US Creators
US content creators lose 23% of potential revenue to content theft—significantly higher than creators in markets with stricter platform security. American platforms prioritize user experience over security, creating systematic vulnerabilities.
Platform-Specific Vulnerabilities
Teachable: 100,000+ US creators affected by integration-heavy architecture and API vulnerabilities Kajabi: Third-party integration points create multiple breach vectors WordPress Course Sites: Thousands of plugin vulnerabilities affect course protection annually
Risk Assessment by Creator Profile
Higher Risk:
- Premium pricing above $500 per student
- Multiple platform presence
- International student base
- High-production-value content
- Annual revenue above $250,000
Lower Risk:
- Community-focused content with live interaction
- Pricing under $200
- Service-based business model
- Rapidly outdated content
- Annual revenue under $100,000
Platform Security Limitations
89% of major platforms place full financial responsibility for content theft on creators, with average response times of 72 hours for takedown requests. Creators earning above $100,000 annually need supplementary protection beyond platform security.
Beyond Traditional DRM: Multi-Layer Security Architecture
Multi-layer content security reduces breach probability by 87% because attackers must overcome multiple independent security mechanisms. Unlike single-point solutions, layered approaches adapt to new attack methods.
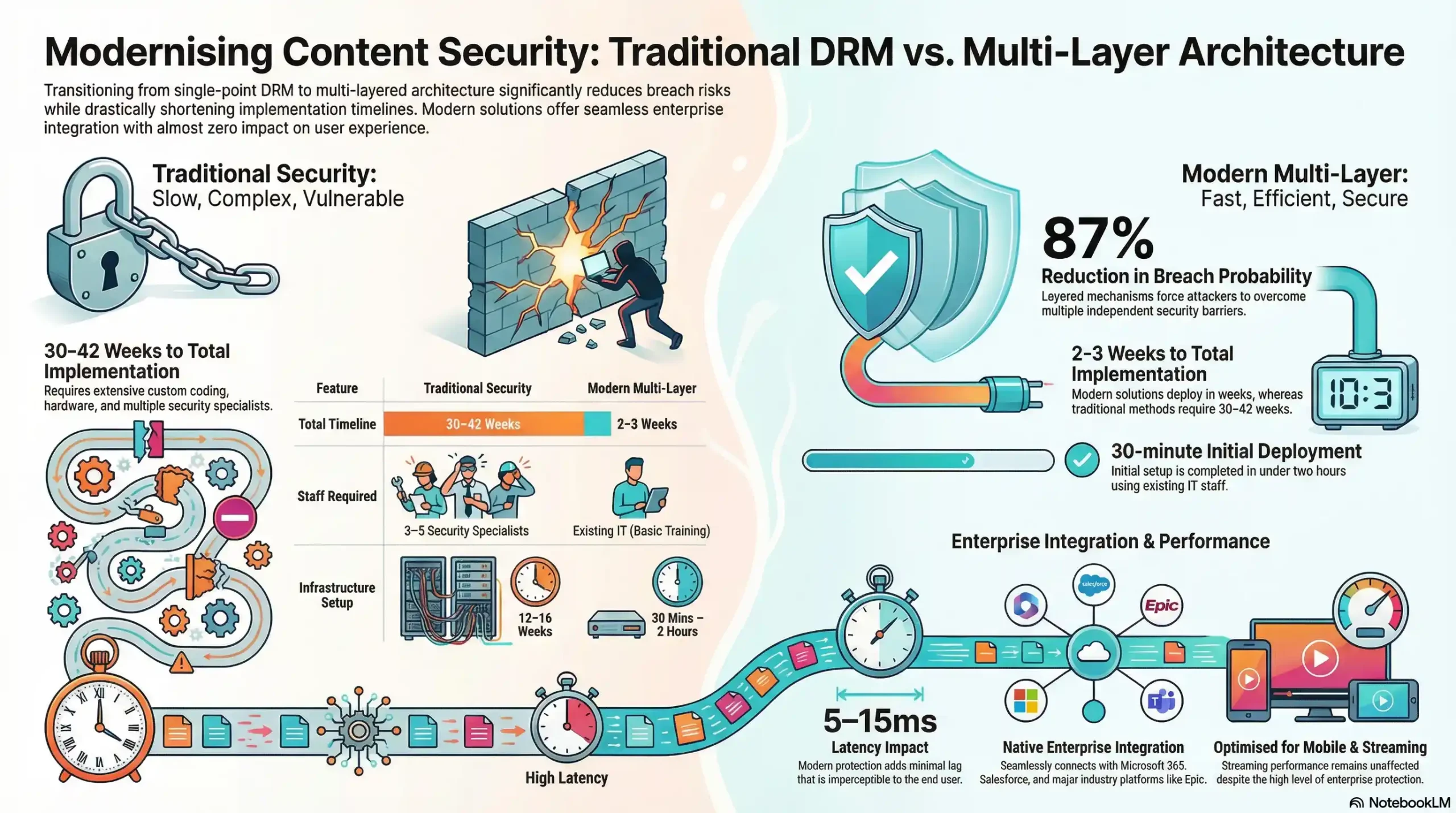
Implementation Timeline Comparison
Traditional Enterprise Security:
- Total timeline: 30-42 weeks
- Technical staff: 3-5 security specialists required
- Infrastructure setup: 12-16 weeks
Modern Multi-Layer Solutions:
- Total timeline: 2-3 weeks
- Technical staff: Existing IT with basic training
- Initial deployment: 30 minutes to 2 hours
US Enterprise Integration Requirements
- Microsoft 365: SSO with Azure Active Directory, SharePoint and Teams integration
- Salesforce: Customer data synchronization, sales process integration
- Industry platforms: Epic/Cerner (healthcare), Canvas/Blackboard (education)
Performance Impact
Modern layered security adds 5-15 milliseconds latency—imperceptible to users—while providing enterprise-grade protection. Mobile users may experience slightly longer initial load times, but streaming performance remains unaffected.
US Regulatory Advantage: Domestic Security Leadership Drives Business Success
US-based content security solutions offer distinct legal enforcement, regulatory compliance, and data sovereignty advantages that international providers cannot match.
Legal Enforcement Speed
- US-based providers: 18-hour average DMCA takedown response
- International providers: 72-hour average due to jurisdictional complexity
- Enhanced damages: US courts favor businesses using domestic security providers
Industry-Specific Compliance
Healthcare (HIPAA): Average compliance failure cost of $2.2 million per incident Education (FERPA): Average penalty of $850,000 for violations
Financial Services (SOX): $3.7 million average annual cost for compliance failures
When to Choose US vs. International Providers
Choose US-Based Security:
- Primary US customer base (>70% revenue)
- Sensitive business information
- Regulated industries
- Legal enforcement likely needed
- Data sovereignty requirements
International May Suffice:
- Primary international markets (>60% revenue)
- Cost optimization primary factor
- Minimal compliance requirements
- Straightforward technical needs
Revenue Protection ROI: Quantifying Security Investment Returns
Content security investment returns $4-7 for every dollar spent through prevented revenue loss, reduced legal costs, and improved customer retention.
Industry-Specific Impact Analysis
Healthcare Training: $5.7 million total annual risk exposure
Corporate Training: $3.8 million average impact including productivity loss
Educational Publishing: $7.15 million including market share erosion
Investment Threshold by Business Size
Small Businesses ($200K-500K revenue): $500-2,000 monthly budget, 250-400% typical ROI Mid-Size ($500K-2M revenue): $2,000-8,000 monthly budget, 300-500% typical ROI
Large Enterprises ($2M+ revenue): $8,000+ monthly budget, 400-700% typical ROI
US Tax Benefits
- Federal R&D Credits: 20% credit for security technology implementation
- State incentives: California offers up to $100,000 annually for creator cybersecurity investments
- Accelerated depreciation: Texas provides 30% first-year deduction for security equipment
Local Resources
Federal Trade Commission (FTC): Visit for digital privacy regulations and consumer protection requirements affecting content security compliance.
National Institute of Standards and Technology (NIST): Check for cybersecurity frameworks and AI risk management standards informing enterprise content security.
U.S. Copyright Office: Access for DMCA procedures, copyright registration, and legal enforcement guidance for digital content protection.
Department of Homeland Security (DHS): Visit for cybersecurity alerts and threat intelligence affecting content protection requirements.
2025 Action Plan: Your Implementation Roadmap
Implement content security through three phases: vulnerability assessment (Q1), core deployment (Q2), and advanced protection (Q3-Q4).
Q1 2025: Foundation Building
Weeks 1-2: Content asset inventory and platform security audit
Weeks 3-4: Risk prioritization and budget authorization
Weeks 5-8: Immediate protection for high-value content and staff training
Q2 2025: Core Architecture
Month 4: Multi-layer security deployment and business system integration Month 5: Process integration and automated threat response Month 6: Performance optimization and documentation
Q3-Q4 2025: Advanced Protection
Q3: AI-powered analytics and forensic capabilities
Q4: Market positioning and 2026 roadmap development
Success Metrics Framework
- Security incidents: Target 90% reduction by Q4
- System uptime: Achieve 99.9% availability
- ROI measurement: Monthly calculation updates
- Customer satisfaction: Maintain scores during implementation
Implementation Readiness Checklist:
- ✓ Executive sponsorship secured
- ✓ Budget allocation finalized
- ✓ Technical team identified
- ✓ Content assets documented
- ✓ Compliance requirements understood
- ✓ Success metrics defined
The content security landscape will continue evolving rapidly throughout 2025, but businesses that establish strong foundations early will maintain competitive advantages while protecting their most valuable digital assets. The key is starting with a clear understanding of your current position and implementing improvements systematically.
Frequently Asked Questions
AI enables sophisticated attacks like automated DRM bypasses. However, modern platforms counter this by using AI for real-time threat detection and advanced behavioral analytics to protect premium content.
Traditional DRM only prevents casual downloading. It lacks advanced analytics and cannot defend against modern AI-powered screen recording bypasses or synthetic content recreation.
It combines multiple independent defenses, such as DRM encryption, dynamic watermarking, and anti-piracy protection. This forces attackers to bypass several systems, drastically reducing breach probability.
Premium online course creators, enterprise media companies, and organizations sharing high-value, proprietary training materials face the highest financial risk from targeted content theft.
Unlike legacy enterprise systems that take months, modern cloud-based security integrations can be deployed in weeks, with initial setup taking as little as 30 minutes.
US-based providers ensure much faster legal enforcement, such as rapid DMCA takedowns. They also guarantee strict data sovereignty and compliance with domestic regulations like HIPAA and FERPA.
Digital content theft costs US businesses over $50 billion annually. Single incidents often cost organizations millions in direct revenue loss, legal fees, and market share erosion.
No. High-performance global delivery networks ensure zero buffering worldwide. Modern security layers add imperceptible latency, maintaining a seamless viewing experience on all devices.
Malicious machine learning tools can remove static watermarks. To counter this, businesses must utilize forensic, dynamic watermarking that adapts to accurately track and identify unauthorized threat sources.
Upgrade immediately if you experience frequent screen recording leaks, if your current DRM implementation predates 2022, or if your provider lacks integrated AI-powered threat detection and analytics.

