Table of Contents
ToggleEncrypted video hosting is a security-first solution that uses military-grade encryption and DRM to ensure your premium content cannot be illegally downloaded or shared. By combining end-to-end encryption with dynamic watermarking, you protect your revenue streams and maintain total control over who views your intellectual property.
Online Security Measures
In an era where cyber-attacks and online data breaches are becoming more sophisticated, businesses and individuals need to adopt robust online security measures. These measures should encompass all aspects of data storage, transmission, and access. When it comes to video content, ensuring data privacy becomes even more critical, as videos often contain sensitive information. Here are some common online security measures:
Use strong and unique passwords: A strong password is a fundamental requirement for protecting any digital asset. It should be sufficiently long, include a variety of character types, and should not be easily guessable.
Implement two-factor authentication (2FA): Two-factor authentication adds an extra layer of security by requiring users to provide additional verification, such as a code sent to their mobile devices, in addition to their password.
Encrypt data in transit: Encryption ensures that data transmitted over networks is secure and not susceptible to interception. Secure protocols, such as HTTPS, should be used for transmitting video data over the internet.
Secure Video Storage
When it comes to video storage, choosing a secure solution is crucial to safeguarding sensitive data. Traditional storage methods may not provide the necessary level of protection against data breaches and unauthorized access. Let’s explore some key elements of secure video storage:
Data Encryption
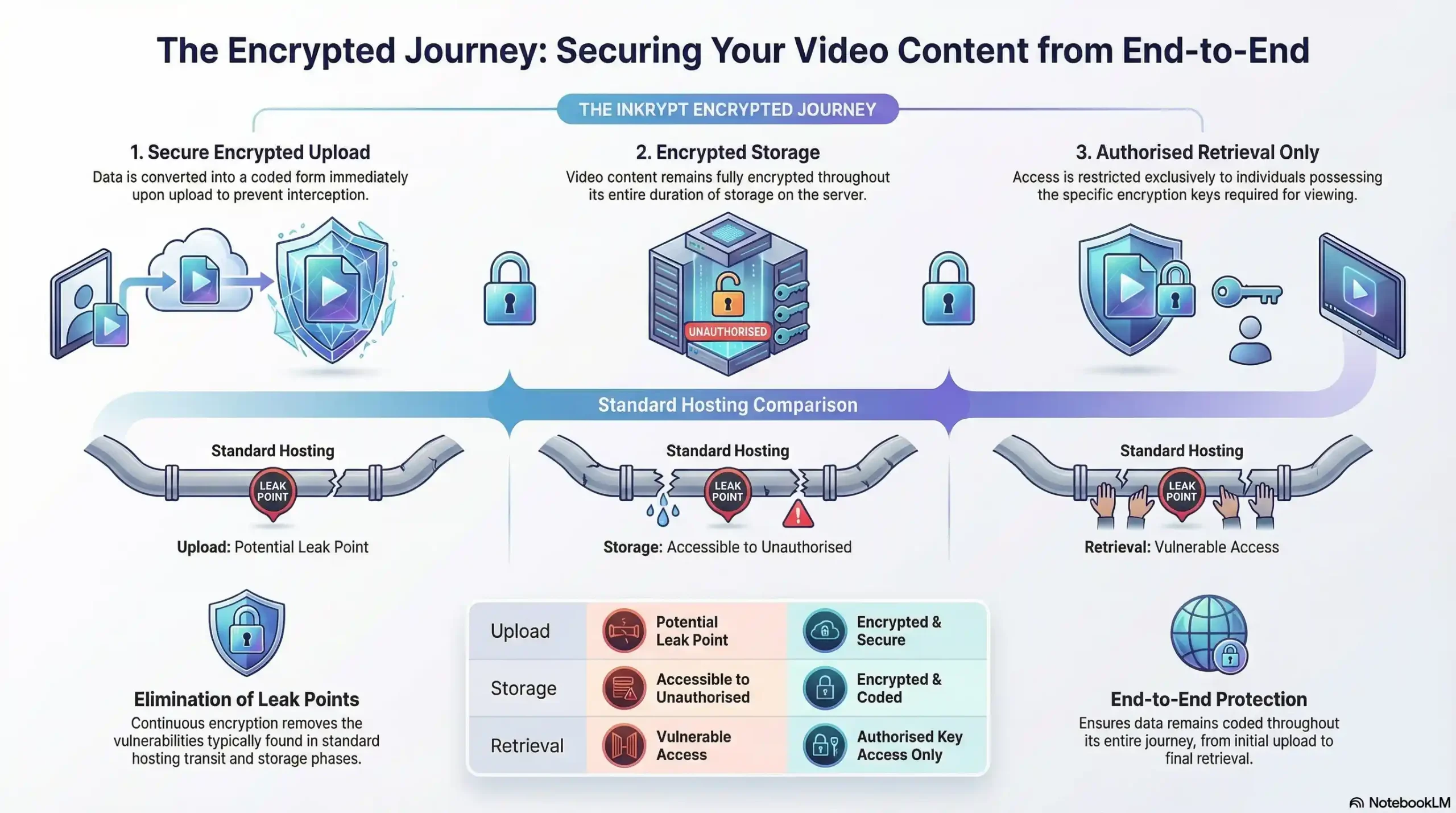
Encryption is a powerful technique that converts data into a coded form, making it unreadable for unauthorized individuals. When considering video storage solutions, it’s essential to choose a platform that offers end-to-end encryption. End-to-end encryption ensures that data remains encrypted throughout its entire journey, from upload to storage and retrieval. This means that only authorized individuals with the encryption keys can access and view the video content.
Access Controls
Another crucial aspect of secure video storage is robust access control mechanisms. Access controls ensure that only authorized individuals can view, edit, or delete video content. Role-based access control is a recommended approach, where different users are granted varying levels of access based on their roles and responsibilities. Additionally, implementing multi-factor authentication for accessing video storage platforms adds an extra layer of security.
Data Backup and Redundancy
Data loss can lead to severe consequences, especially when valuable video content is at stake. Secure video storage solutions should offer reliable data backup and redundancy features. Regular backups ensure that data can be recovered in the event of accidental deletion, system failures, or natural disasters. Redundancy, achieved through distributed data storage across multiple servers, ensures high availability and minimizes the risk of data loss.
Secure Video Hosting
Secure video hosting involves the storage and delivery of video content through a platform that prioritizes data privacy and security. Let’s dive into the key features and benefits offered by secure video hosting:
Content Protection
A secure video hosting platform should provide robust content protection measures to prevent unauthorized copying, sharing, and downloading of video content. Digital Rights Management (DRM) technologies can be employed to enforce copyright restrictions and prevent piracy. Secure video hosting platforms should also offer the ability to add watermarks, disable video embedding, and restrict access to specific IP addresses or geographical locations.
Secure Video Streaming
Streaming video hosting involves delivering video content in real-time over the internet. When it comes to secure video streaming, encryption plays a crucial role in protecting the video data during transmission. Advanced video streaming protocols, such as Secure Real-Time Transport Protocol (SRTP) or Secure Reliable Transport (SRT), can be employed to ensure secure and reliable video streaming.
Analytics and Viewer Insights
In addition to data privacy, secure video hosting platforms often provide analytics and viewer insights. These features enable content creators and businesses to gather valuable data about viewer engagement, such as the number of views, watch time, and audience demographics. It’s important to ensure that such platforms offer privacy-friendly analytics, where viewer data is anonymized, aggregated, and compliant with relevant data protection regulations.
Encrypted Video Hosting
Encrypted video hosting takes video security to the next level by combining secure video storage and secure video hosting. By leveraging end-to-end encryption techniques, encrypted video hosting offers unparalleled data privacy and protection. Here are some key benefits of encrypted video hosting:
Complete Data Privacy
With encrypted video hosting, all video content is encrypted using strong encryption algorithms. This ensures that even if the data is intercepted or accessed without authorization, it remains unreadable and unusable. This level of data privacy is crucial for organizations and individuals who deal with sensitive and confidential video content.
Secure Collaboration
Encrypted video hosting platforms often provide collaboration features that enable multiple users to work on video projects securely. Users can securely share, review, and edit video content without the risk of unauthorized access. Collaborative workflows are protected by encryption and access controls, ensuring that only authorized individuals can contribute to the video content.
Compliance with Data Protection Regulations
Data protection regulations, such as the General Data Protection Regulation (GDPR), require organizations to ensure the security and privacy of personal data. Encrypted video hosting platforms offer robust data protection mechanisms, helping organizations comply with such regulations. By encrypting video content and implementing strong access controls, organizations can demonstrate their commitment to data privacy and avoid potential legal issues.
The Role of Encrypted Video Hosting in Various Industries
Encrypted video hosting can benefit a wide range of industries and individuals who deal with video content. Let’s explore how encrypted video hosting can enhance data privacy in different sectors:
eLearning Platforms
eLearning platforms often rely on video content to deliver educational material. With encrypted video hosting, eLearning platforms can ensure that sensitive course material remains secure and protected. Students’ personal information and progress can also be safeguarded using encryption and access controls, instilling trust and confidence in the eLearning platform.
Influencers and Digital Marketing
For influencers and digital marketers, video content is a valuable asset that needs to be protected from unauthorized use or distribution. Encrypted video hosting platforms offer content protection features, such as disabling video downloads and embedding restrictions, ensuring that valuable video content remains exclusively accessible to authorized viewers.
Content Creators
Content creators invest significant time and effort into producing high-quality video content. Encrypted video hosting platforms provide an added layer of security, protecting their creative work from unauthorized access, plagiarism, and unauthorized distribution. By ensuring data privacy, content creators can maintain control over their intellectual property.
Software Development and Technical Support
Software development companies and technical support teams often utilize video tutorials and documentation to assist users. Encrypted video hosting platforms enable them to securely store and share these instructional videos, ensuring that sensitive information, such as code snippets or configuration details, remains confidential and accessible only to authorized users.
Conclusion
Data privacy is a critical concern in today’s digital landscape, and video content is no exception. Encrypted video hosting provides a robust solution for ensuring data privacy and protecting sensitive video content. By leveraging encryption, strong access controls, and secure transmission protocols, encrypted video hosting platforms offer unparalleled security and data protection. Whether you are an eLearning platform, content creator, influencer, or digital marketer, encrypted video hosting can enhance your online security measures and instill confidence in your audience.
Remember, data privacy should never be compromised, especially when it comes to video content. Choose an encrypted video hosting solution that meets your specific needs and ensures the highest level of data privacy and protection. Safeguard your sensitive videos and empower your audience to engage with your content without worrying about their privacy.
FAQs
Encrypted video hosting stores and streams videos using end-to-end encryption, making content unreadable without keys. It protects data at rest and in transit.
It uses strong algorithms like AES-256 to prevent unauthorized access, even if intercepted. Only authorized users decrypt and view videos securely.
Regular hosts risk breaches and downloads; encrypted ones add DRM, access controls, and no-download features to block piracy and leaks.
Prevents unauthorized sharing, supports secure collaboration, and protects intellectual property with watermarks and geo-restrictions.
Upload videos to a platform with end-to-end encryption, enable 2FA, role-based access, and backups. Use HTTPS for all transmissions.
Yes, it meets GDPR via encryption, access logs, and anonymized analytics, ensuring personal data privacy and audit trails.
Dynamic watermarks, signed URLs, domain locking, and DRM like Widevine block downloads and screen recording effectively.
Self-hosting offers control but requires manual encryption and maintenance; cloud platforms provide easier end-to-end security and redundancy.
Protocols like SRTP or TLS encrypt streams in real-time, preventing interception while allowing smooth playback for authorized viewers.
Users worry about data collection on YouTube/Zoom; recommend password protection, DRM, and self-hosting to avoid tracking and breaches.

