Table of Contents
ToggleSelf-hosting course videos on WordPress exposes your content to direct MP4 URL theft, hotlinking, browser-based download tools, and credential sharing — with zero encryption protection by default. WordPress has no built-in Digital Rights Management (DRM) infrastructure. Security plugins operate only at the application layer and cannot prevent server-level file extraction. The only professional-grade solution is DRM-encrypted video hosting — combining Widevine, FairPlay, and PlayReady encryption with dynamic watermarking and signed URLs — delivered through a dedicated secure video platform.
The False Sense of Security WordPress Gives You
WordPress powers over 43% of the internet. It is flexible, affordable, and deeply familiar to course creators building their first — or fiftieth — online learning platform. When you upload a course video to your WordPress media library, it feels contained. It feels like yours. It feels safe.
It is not.
WordPress is a content management system. It was built to publish content, not to protect it. When a video file lands in your WordPress media library, it is stored as a static asset on your web server — accessible, in most configurations, to anyone who knows the URL. There is no encryption. There is no license control. There is no DRM layer standing between your premium course content and a determined downloader.
The illusion of security comes from familiarity. Your LMS plugin hides the video behind a paywall page. Your video player removes the right-click menu. A security plugin promises protection. But none of these measures touch the actual file. The MP4 sitting on your server remains exposed at the infrastructure level — and pirates operate at the infrastructure level.
What Happens When You Upload a Video to WordPress Media Library
The moment you upload a video to WordPress, the file is assigned a permanent, publicly accessible URL. A typical path looks like this: yourdomain.com/wp-content/uploads/2025/01/course-module-1.mp4. No login is required to access this URL directly. No membership check is performed at the server level. Any viewer who can find that URL — and finding it takes less than thirty seconds using a browser’s built-in developer tools — can download your video without ever paying for your course.
This is not a vulnerability in the traditional sense. It is simply how static file hosting works. And WordPress, by design, does nothing to change it.
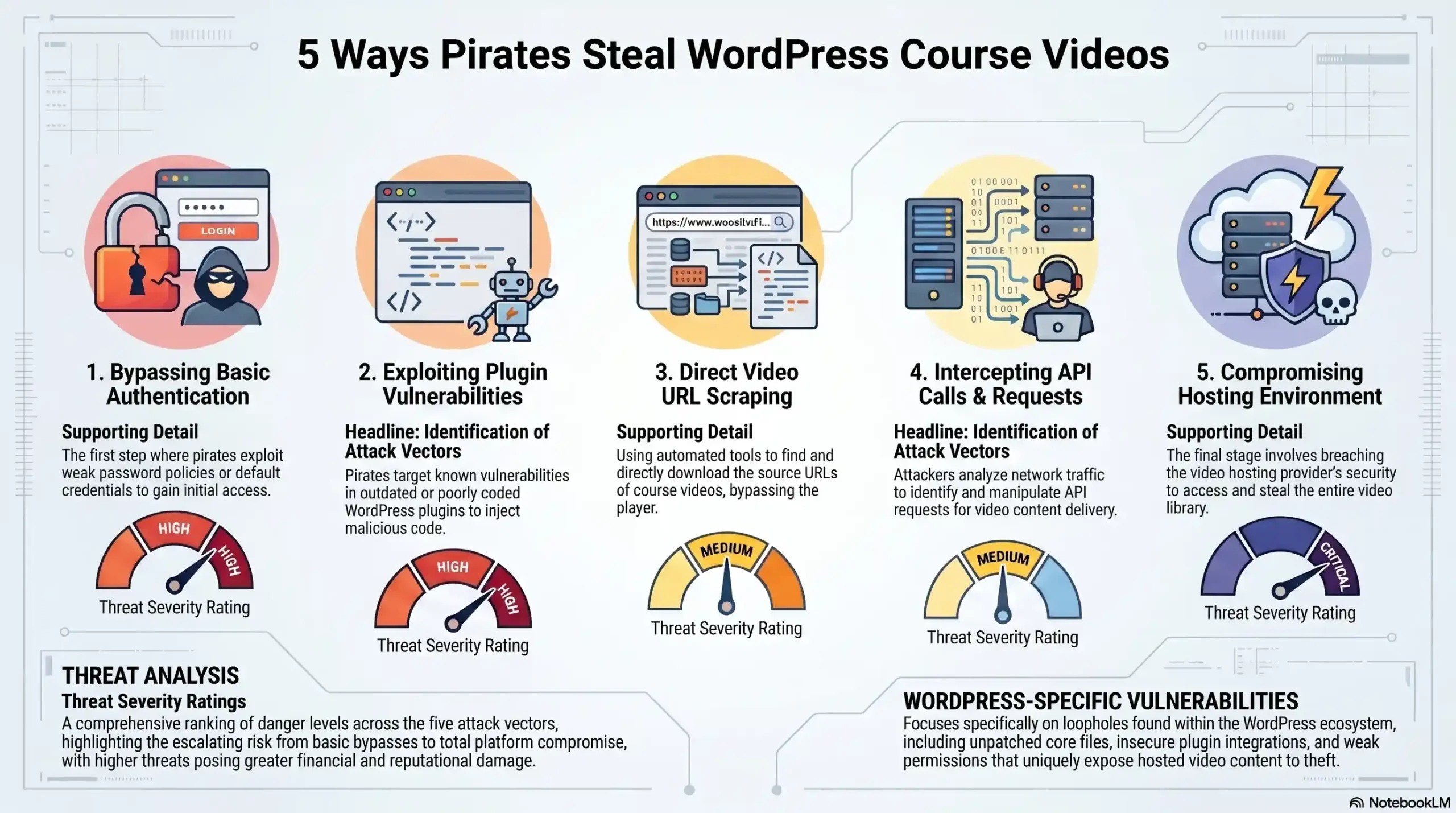
The 5 Real Attack Vectors Targeting Your Course Videos Right Now
These are not theoretical threats. They are active, documented techniques used daily against course creators, coaches, and e-learning platforms worldwide. Understanding each one is the first step toward building a genuine defense.
1. Direct MP4 URL Extraction via Browser DevTools
Every modern browser ships with a developer console. Your students have it. Anyone visiting your site has it. By opening the Network tab while a video plays, any user can identify the direct URL of the video file being streamed. Once that URL is copied, the video can be downloaded with a standard browser or any download manager — no special tools required. Anyone who opens the browser’s developer tools can usually find the direct video URL. Once they have that link, they can download or share the video without visiting your site again. Disabling the right-click menu, hiding player controls, or using a custom video player does not close this vulnerability. The URL is transmitted over the network regardless of what the player interface shows.
2. Hotlinking & Remote Embedding
Hotlinking occurs when someone copies your video’s direct URL and embeds it on their own website or platform — streaming your file from your server, on their page, without your permission. Your server pays the bandwidth costs. They deliver your content for free. Beyond the financial drain, hotlinked course videos can appear on competitor platforms, piracy aggregators, or social sharing sites with no attribution and no access control. Basic .htaccess rules can limit hotlinking by domain, but they are trivially bypassed using proxy servers or simple URL manipulation.
3. Browser Extension & Download Manager Attacks
Tools like Video DownloadHelper, Internet Download Manager (IDM), and dozens of free browser extensions are designed specifically to intercept and capture video streams from any website. These tools operate at the network interception layer — they capture the stream as it travels to the browser, entirely bypassing any interface-level restrictions your WordPress plugins may impose. If your video is served as a standard MP4 file, it is vulnerable — even if you have hidden player controls or disabled right-click.
4. Credential Sharing & Account Hijacking
A single paying student can share their login credentials with dozens of others. On a standard WordPress LMS setup, there is no mechanism to detect simultaneous logins from different IP addresses, flag account sharing, or revoke access in real time. One purchase becomes unlimited access. There is no forensic trail, no session binding, and no way to identify which account was responsible for a leak after the fact. Password sharing drains up to 30% of e-learning revenue — a figure that compounds silently while course creators attribute declining enrollment to market saturation rather than active exploitation.
5. Screen Recording & AI-Assisted Capture
Even a perfectly secured video stream can be captured through screen recording. Built-in OS tools — Windows Game Bar, macOS QuickTime — require no technical knowledge. Third-party tools go further, capturing at full resolution with audio. With high-speed internet and advanced downloading and hacking tools readily available, pirated content can be created and shared within hours of release. This is the attack vector that no firewall can fully stop — but it can be powerfully deterred through dynamic watermarking, which embeds a unique, invisible identifier into each viewing session, creating a forensic trail that survives re-encoding and compression.
| Attack Vector | Method Used | Threat Level | Stopped by WordPress Plugins? | Stopped by DRM? |
|---|---|---|---|---|
| Direct MP4 URL Extraction | Browser DevTools / Network Tab | Critical | No | Yes |
| Hotlinking & Remote Embedding | Copied URL embedded on external site | Critical | Partial | Yes |
| Browser Extension / Download Manager | Stream interception tools | Critical | No | Yes |
| Credential Sharing | Shared login credentials | High | Partial | Yes — Session binding |
| Screen Recording & AI Capture | OS/third-party screen capture | High | No | Yes — Watermarking deterrent |
Why WordPress Security Plugins Are Not Enough
The WordPress plugin ecosystem offers dozens of tools that promise video protection. Restrict Content Pro. MemberPress. WP Shield. Prevent Direct Access. These are legitimate, well-built products — and they are fundamentally insufficient for serious content protection.
Here is why: every WordPress security plugin operates at the application layer. They control who can see a page, whether a download button appears, and whether a URL is obfuscated. What they cannot do is encrypt the video file itself. The file remains a static asset on your server. The access control logic lives in PHP code that executes before the file is served — but the file, once the access check passes, travels unencrypted to the browser.
Even if you try using JavaScript and other basic security plugins, you are always vulnerable due to the private key being revealed through the network and other logs. This is the critical architectural flaw that no plugin can patch. Application-layer security stops casual browsers. It does not stop anyone with moderate technical knowledge and a free browser extension.
The “95% of average users” argument — frequently cited by plugin vendors — is dangerously misleading for premium course creators. The 5% who bypass application-layer security are precisely the users who will redistribute your content at scale. One technically capable pirate with access to your course can generate thousands of unauthorized copies. Protecting against 95% of threats while ignoring the 5% that cause 100% of the damage is not a security strategy. It is wishful thinking.
The Real Cost of Course Piracy: What the Data Says
Piracy is not an abstract risk. It is an active, measurable revenue drain happening to course creators right now.
Piracy sites attracted 216.3 billion visits in 2024. The e-learning sector is among the most targeted categories, with Telegram groups and torrent sites serving as primary distribution channels for leaked course content. Telegram-based course piracy led to an estimated $240 million in annual revenue loss for India’s e-learning sector alone in 2024. Scale that pattern globally and the financial exposure becomes staggering.
The damage does not happen all at once. It follows a predictable cascade. A single student downloads your course through a browser extension on Day 1. By Week 2, the content appears in a private Telegram group. By Month 2, it is indexed on piracy aggregator sites. By Month 6, someone is selling your entire brand as their own. At that point, you are not just losing revenue — you are competing against a free version of your own product, actively undermining the perceived value of your work.
For course creators charging $500, $1,000, or $5,000 per enrollment, a single uncontrolled leak is not a minor inconvenience. It is an existential threat to the business model.
🔒 Is your course content exposed right now?
Most course creators do not know they have been breached until they see their content shared for free online. Get a free security consultation from the team at Inkrypt Videos.
📞 804 500 2905 | 📍 1528 W Sunset Ave, Springdale, Arizona 72764
What Enterprise-Grade Video Protection Actually Looks Like
Netflix encrypts every stream. Disney+ enforces hardware-level DRM on every device. These platforms do not rely on removing download buttons or hiding video URLs. They encrypt content at the file level and issue time-limited, device-bound licenses for every single playback session. This is the standard that serious content protection demands — and it is now accessible to individual course creators, not just billion-dollar studios.
DRM Encryption — The Only Real Lock on Your Content
Digital Rights Management (DRM) is the encryption framework used by every major streaming platform on earth. It operates through three dominant systems — Google Widevine (Chrome, Android, Firefox), Apple FairPlay (Safari, iOS, macOS), and Microsoft PlayReady (Edge, Windows) — providing cross-platform coverage across virtually every device your students use.
Unlike AES-128 or standard HLS encryption, DRM integrates with DASH/HLS encryption but adds hardware-backed key protection. Decryption keys are never exposed in network logs. They are issued per session, per device, to authenticated users only — and they expire. Even if a pirate captures a stream URL, it is cryptographically useless without a valid, unexpired license issued by the DRM server to a verified device.
Dynamic Watermarking — Your Forensic Safety Net
Dynamic watermarking embeds an invisible, unique identifier into every video playback session. This identifier encodes user ID, device ID, session timestamp, and IP address — creating a forensic fingerprint that is specific to each viewing instance. These invisible marks survive compression, re-encoding, and even screen recording in many cases. If a leak occurs, forensic analysis of the pirated copy identifies the exact account responsible — enabling legal action, immediate access revocation, and public deterrence.
Watermarking does not prevent piracy. It makes piracy traceable, prosecutable, and — critically — psychologically deterring. A student who knows their name and session data is embedded in every frame they watch is far less likely to share that content.
Signed URLs & Time-Based Access Tokens
Signed URLs are cryptographically generated links that carry an embedded expiration timestamp and a user-specific token. When a student requests a video, the server generates a unique URL valid only for that session. Once the session ends or the token expires, the URL is mathematically invalid — it returns an error, not a video file. A URL intercepted by a download tool, copied from network logs, or shared in a Telegram group delivers nothing of value to a pirate.
Global CDN Delivery — Security Without Sacrificing Performance
Enterprise DRM protection should not come at the cost of viewing experience. Amazon CloudFront CDN integration ensures that encrypted video streams are delivered from edge servers geographically close to each viewer — minimizing latency, eliminating buffering, and maintaining HD quality across every region. Security and performance are not a trade-off. They are a combined deliverable.
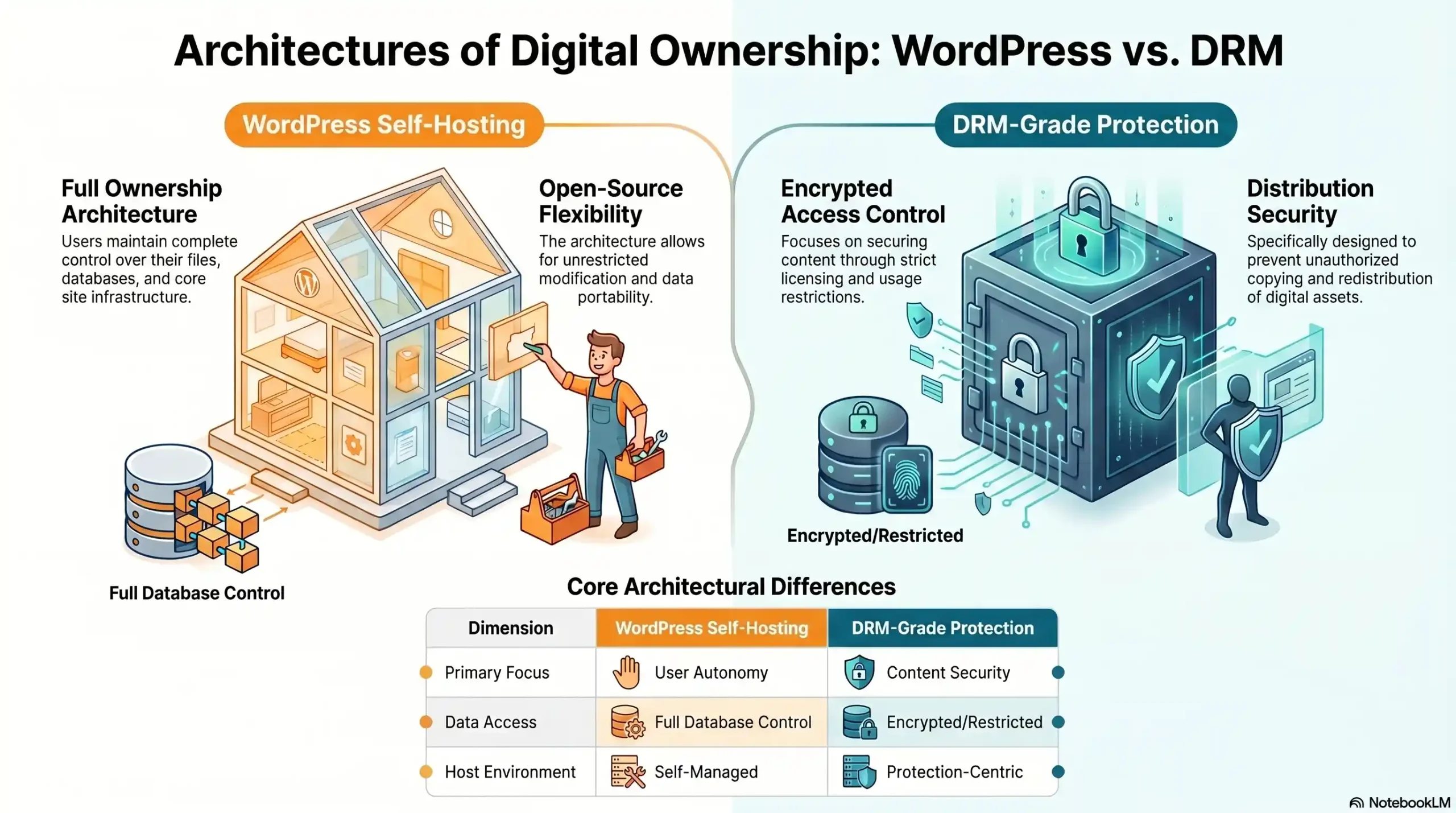
| Security Dimension | WordPress Self-Hosting | DRM-Grade Protection (Inkrypt Videos) |
|---|---|---|
| File-Level Encryption | None | AES + DRM hardware-bound |
| Direct URL Access Prevention | Exposed | Signed URLs, session-bound |
| Download Tool Protection | Vulnerable | DRM blocks interception |
| Credential Sharing Detection | None | Session binding + alerts |
| Screen Recording Deterrence | None | Dynamic watermarking |
| Hotlink Prevention | Partial (.htaccess) | Domain restriction enforced |
| Forensic Piracy Tracking | None | Per-session watermark trail |
| Global CDN Performance | Server-dependent | Amazon CloudFront CDN |
| LMS Plugin Integration | Native | Full WordPress compatibility |
| Setup Time | Immediate | Under 30 minutes |
How Inkrypt Videos Solves the WordPress Security Problem
Inkrypt Videos was built for exactly this problem — the gap between what WordPress promises and what serious content protection actually requires.
The platform delivers multi-DRM encryption using Google Widevine, Apple FairPlay, and Microsoft PlayReady in a unified system, ensuring every student on every device is covered under the same cryptographic protection framework used by global streaming platforms. There is no separate integration required for Android vs. iOS vs. desktop. The protection is universal.
Dynamic watermarking is applied per session, per viewer — silently and invisibly — generating a unique forensic fingerprint for every single playback event. If content leaks, the source is traceable within hours. Not weeks. Hours.
Integration with WordPress takes under 30 minutes. Native plugin support for LearnDash, LifterLMS, Tutor LMS, and other major LMS platforms means course creators do not need a developer, a DevOps team, or a technical background to deploy enterprise-grade protection. The plugin installs like any other WordPress plugin. The security it delivers is anything but ordinary.
Real-time analytics provide visibility into viewer behavior — watch time, drop-off points, geographic distribution, and device breakdown — giving course creators the data intelligence to improve content while simultaneously monitoring for anomalous access patterns that may signal credential sharing or unauthorized distribution.
🛡️ Stop leaving your premium content unprotected.
Inkrypt Videos delivers the same DRM encryption used by Netflix and Disney — in a 30-minute WordPress integration.
📞 804 500 2905 | 📍 1528 W Sunset Ave, Springdale, Arizona 72764
Step-by-Step: Migrating from WordPress Self-Hosting to Secure Video Delivery
Transitioning from unprotected WordPress video hosting to enterprise-grade DRM delivery is simpler than most course creators expect. The following five steps represent a complete migration path from exposed to protected.
Step 1 — Audit Your Current Video Exposure
Begin by cataloguing every video asset currently stored in your WordPress media library. Open each video URL in an incognito browser window without logging in to your site. If the video plays — your content is publicly accessible right now. Document every exposed file as a priority migration target.
Step 2 — Choose a DRM-Certified Video Hosting Platform
Select a platform that supports multi-DRM (Widevine + FairPlay + PlayReady), dynamic watermarking, signed URLs, and WordPress LMS integration. Verify that the platform uses a global CDN for delivery. Confirm that setup requires no custom development. Inkrypt Videos meets all of these criteria with a setup timeline measured in minutes, not months.
Step 3 — Integrate with Your WordPress LMS in Under 30 Minutes
Install the Inkrypt Videos WordPress plugin from your dashboard. Connect your account via API key. The plugin automatically replaces your existing video embeds with DRM-encrypted, watermarked streams — your course structure, your page layouts, and your student experience remain completely unchanged.
Step 4 — Enable Watermarking, Signed URLs & Access Controls
Within the platform dashboard, activate dynamic watermarking for all content, configure signed URL expiration windows (recommended: per-session), set domain restrictions to your course domain only, and enable geo-blocking for regions outside your target audience. These controls take minutes to configure and provide immediate, measurable uplift in content security.
Step 5 — Monitor Analytics & Set Piracy Alerts
Once live, use Inkrypt’s real-time analytics dashboard to monitor playback patterns. Flag accounts with anomalous concurrent sessions, unusual geographic access clusters, or abnormal watch frequency. Configure automated alerts for suspected credential sharing. Your content is now not just protected — it is actively monitored.
Local Resources & Citations
1. U.S. Copyright Office — Copyright.gov The official U.S. federal authority on intellectual property law — reference this to understand your legal rights when course content is stolen, file DMCA takedown notices against pirated copies of your videos, and document ownership of your original course material.
2. World Intellectual Property Organization — WIPO.int The United Nations agency governing global intellectual property standards — essential for course creators distributing content internationally, as WIPO’s frameworks define the legal basis for DRM enforcement and anti-piracy protections across 193 member countries.
3. National Institute of Standards and Technology — NIST.gov The U.S. government’s official cybersecurity and cryptography standards body — reference NIST’s encryption guidelines to verify that your video hosting platform’s AES and DRM encryption implementations meet federally recognized security benchmarks.
4. MIT OpenCourseWare — MIT.edu MIT’s official open educational resource platform — demonstrates institutional best practices for large-scale secure video delivery and content access control, providing an academic credibility benchmark that course creators can reference when evaluating enterprise-grade hosting standards.
Conclusion: Your Course Is a Business — Protect It Like One
You spent months building your course. You refined your curriculum, recorded your lessons, edited your production, and priced your expertise. Every hour of that work is stored in video files that — right now, on a WordPress self-hosted setup — are accessible to anyone who knows where to look.
Security is not paranoia. For a course creator, it is professional responsibility. The tools that protect your content are the same tools that protect your revenue, your reputation, and the value of the expertise you have worked your entire career to develop.
WordPress is an excellent platform for selling and delivering courses. It is not a video security system. Treating it as one is the most expensive mistake a course creator can make.
Enterprise-grade protection is no longer exclusive to enterprise budgets. Inkrypt Videos delivers DRM encryption, dynamic watermarking, global CDN performance, and 30-minute WordPress integration — making military-grade content security accessible to every creator, at every scale.
🔐 Your content is your business. Guard it with the technology it deserves.
Join thousands of course creators, media companies, and content publishers who trust Inkrypt Videos for unbreakable video protection.
📞 804 500 2905 | 📍 1528 W Sunset Ave, Springdale, Arizona 72764
Frequently Asked Questions
No. Hosting course videos directly on WordPress is not safe for premium content. WordPress stores video files as static assets with publicly accessible URLs, meaning any viewer with browser developer tools can locate, copy, and download your video without a subscription or login. Anyone who can find that URL can download or share your video without visiting your site again.
No. WordPress security plugins operate at the application layer — they control page access but cannot encrypt the video file itself. Even using JavaScript and other basic security plugins leaves you vulnerable due to the private key being revealed through the network and other logs. The only technology that protects the file at the encryption level is DRM — Digital Rights Management — which operates independently of WordPress’s plugin architecture
DRM (Digital Rights Management) is an encryption framework that locks video content at the file level and issues time-limited, device-bound playback licenses to authenticated users only. It uses three major systems — Google Widevine, Apple FairPlay, and Microsoft PlayReady — to cover every device and browser. DRM integrates with DASH/HLS encryption but adds hardware-backed key protection, making it impossible for download tools or stream-ripping software to extract usable content. For course creators selling premium content, DRM is the only professional-grade solution
Video piracy on WordPress course sites happens through five primary methods: direct MP4 URL extraction via browser DevTools, hotlinking on external sites, browser extension interception of video streams, credential sharing between students, and screen recording. If your video is served as a standard MP4 file, it is vulnerable — even if you have hidden player controls or disabled right-click. None of these attacks require advanced technical skill, and none are stopped by standard WordPress security plugins
Dynamic watermarking embeds an invisible, unique identifier — including user ID, device ID, session timestamp, and IP address — into every individual video playback session. Unlike static logo watermarks, dynamic watermarks are forensic tools. These invisible marks survive compression, re-encoding, and even screen recording in many cases. If a leak occurs, the watermark identifies exactly which account was responsible, enabling legal action and immediate access revocation
The financial impact of course piracy is substantial and growing. Piracy sites attracted 216.3 billion visits in 2024, with the e-learning sector among the most heavily targeted categories. Telegram-based course piracy led to an estimated $240 million in annual revenue loss for India’s e-learning sector alone. Beyond direct revenue loss, piracy erodes course perceived value, suppresses new enrollments, and can collapse a creator’s entire pricing model within months of a single uncontrolled leak
With the right platform, adding enterprise-grade DRM protection to a WordPress LMS takes under 30 minutes. Dedicated solutions like Inkrypt Videos offer native WordPress plugin integration compatible with LearnDash, LifterLMS, and Tutor LMS — requiring no custom development or technical expertise. The plugin installs from the WordPress dashboard, connects via API key, and automatically replaces unprotected video embeds with DRM-encrypted, dynamically watermarked streams — without altering your existing course structure or student experience
Use platforms like Vimeo or Wistia with domain locks and signed URLs for secure embeds that protect against downloads.
Layer domain restrictions, encryption, and anti-hotlink rules via specialized plugins; avoid direct uploads.
Yes, slow load times from videos tank rankings; Google penalizes sites over 3 seconds.
Open ports and common paths like wp-login invite scans; fail2ban helps but constant vigilance is needed.
Disclaimer:
This article is for informational and educational purposes only. While it outlines common security risks and protection strategies, implementation results may vary depending on your platform configuration, hosting environment, and security practices. No system can guarantee absolute prevention of content piracy, but layered security measures can significantly reduce risk.

