Table of Contents
ToggleCourse piracy is the unauthorized copying, downloading, redistribution, or resale of paid online course content without the creator’s permission. The most common theft methods include credential sharing, screen recording, direct video downloading via network sniffers, Telegram group redistribution, third-party re-uploading, and AI-assisted content stripping. Effective prevention requires a layered protection stack: DRM encrypted video streaming, dynamic watermarking, secure video hosting with domain restrictions, signed URLs, and real-time access monitoring.
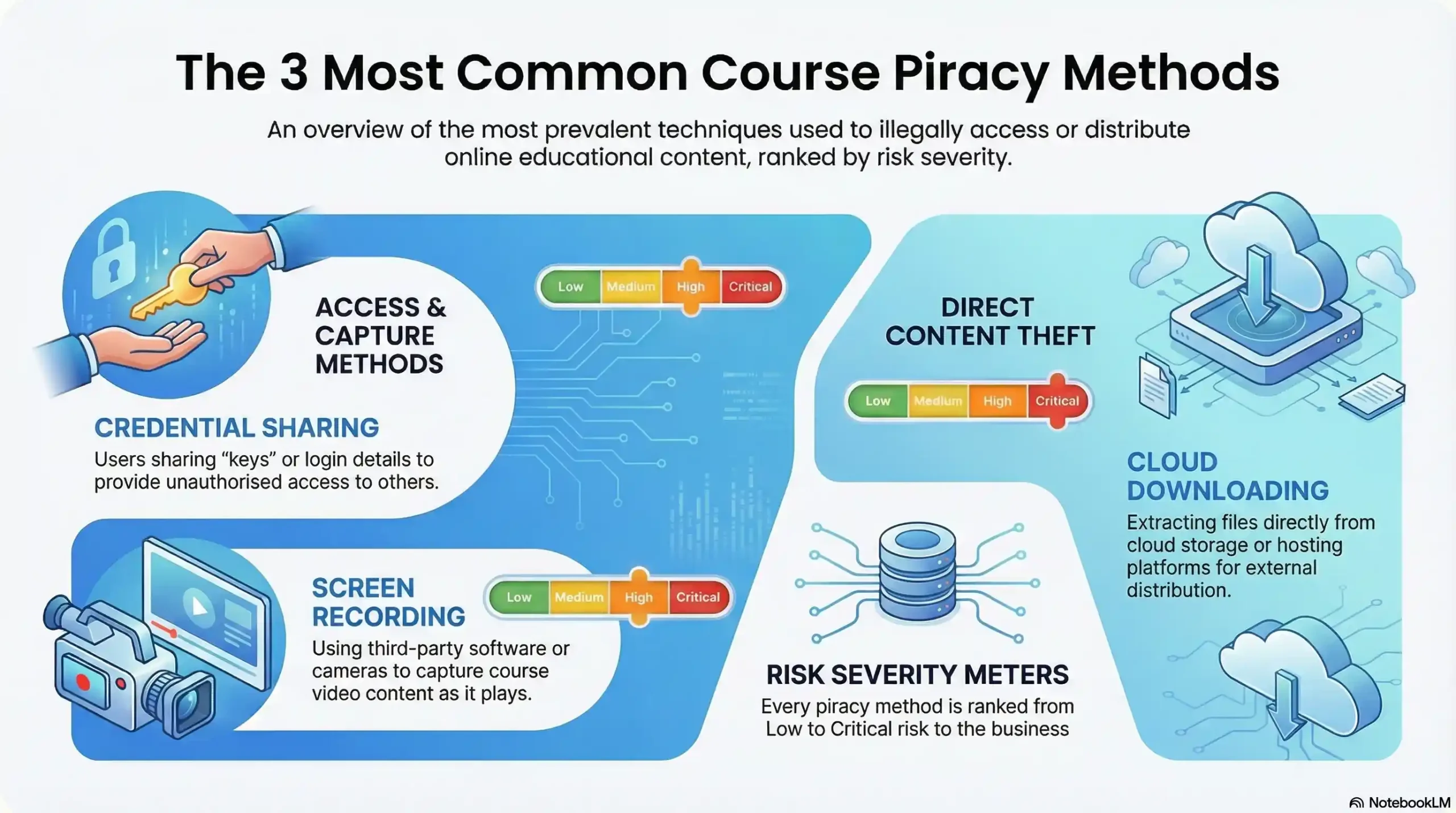
| Piracy Method | How It Works | Risk Level | Key Detection Signal |
|---|---|---|---|
| Credential Sharing | One account accessed by many unauthorized users | 🔴 Critical | Simultaneous logins from multiple locations |
| Screen Recording | Desktop/browser tools capture video playback | 🔴 Critical | No direct log — requires watermark forensics |
| Network Sniffer Downloads | Tools intercept HLS video stream URLs | 🔴 Critical | Abnormal bandwidth spikes per session |
| Telegram Redistribution | Leaked content shared in mass piracy groups | 🔴 Critical | Course titles appearing in Telegram searches |
| Re-upload & Resale | Stolen content sold on third-party platforms | 🟠 High | DMCA alerts, duplicate content signals |
| AI-Assisted Stripping | AI tools repackage and redistribute content | 🟠 High | Derivative content appearing with altered metadata |
Introduction: Your Course Is Being Stolen Right Now
You spent six months building your flagship course. Hundreds of hours scripting, recording, editing, and refining every module. You launched, sales came in, and students enrolled. What you probably did not know is that within 48 hours of your launch, there is a statistically significant chance that your content was already being shared somewhere you never authorized.
This is not a hypothetical. Global video piracy losses have surged to over $63 billion annually, and the e-learning sector is one of the fastest-growing targets. Course creators are uniquely vulnerable because most rely on platforms and hosting solutions that were never built with serious security in mind.
The most dangerous misconception in online education today is this: “My content is probably fine.” It is not a question of whether course piracy will affect you. For serious creators, it is a question of when — and whether you will be equipped to detect it, prove it, and stop it.
This guide breaks down exactly how content theft happens, the warning signs that your course may already be compromised, and the professional-grade protection stack that permanently closes every door pirates use to walk through.
What Is Course Piracy? (And Why It’s Getting Worse)
Course piracy refers to any unauthorized access, duplication, distribution, or resale of paid online educational content. This includes video lessons, PDFs, slide decks, quizzes, assignments, and any other digital material that forms part of a premium course — taken and used without the creator’s permission or compensation.
While digital piracy has existed as long as the internet itself, the online education sector has become a prime target for a specific reason: explosive market growth combined with weak default protection. The global e-learning market is on track to surpass $375 billion, making premium course content one of the most valuable — and most stolen — digital assets in the world.
What has changed most dramatically in recent years is the sophistication of the methods. Early piracy was clumsy: someone downloaded a video file and emailed it to a friend. Today’s pirates operate organized redistribution networks, use browser-level interception tools, and in 2025, leverage AI to strip, repackage, and re-upload entire curricula in minutes. The creators who are most at risk are the ones still relying on the security assumptions of five years ago.
How Online Course Content Gets Stolen: 6 Primary Methods
Understanding the mechanics of piracy is not an academic exercise. It is the foundational step to building a defense that actually works. Here are the six methods responsible for the overwhelming majority of course content theft today.
Method 1: Credential Sharing & Account Hijacking
The simplest and most widespread form of course piracy requires zero technical skill. One student purchases legitimate access, then shares their login credentials — username and password — with friends, colleagues, or members of a private group. In organized piracy operations, a single account can be shared across dozens or even hundreds of simultaneous users.
The financial math is brutal. If your course is priced at $297 and one compromised account is shared with just 20 people, you have lost nearly $6,000 in potential revenue from that single breach. Multiply that across multiple compromised accounts and the losses compound rapidly.
Detection becomes possible when access monitoring flags simultaneous logins from geographically impossible locations — the same account logged in from New York, London, and Mumbai within the same hour is a clear indicator of credential sharing. Without this monitoring layer in place, creators have no visibility into the problem at all.
Method 2: Screen Recording & Capture Tools
Even when video downloads are technically disabled, screen recording remains one of the most persistent threats to course content. Readily available tools — both browser extensions and desktop applications — allow any viewer to record exactly what plays on their screen, capturing your video in its entirety without triggering any standard platform protection.
The critical misunderstanding here is that disabling right-click, hiding download buttons, or locking video controls provides any meaningful security. These measures stop casual users. They do nothing against someone running a screen capture tool in the background while your video plays normally in their browser.
The only effective countermeasure is dynamic watermarking — embedding the viewer’s unique identifier (email address, user ID, or IP) directly into the video frame during playback. Even if the screen-recorded copy circulates, the embedded watermark forensically identifies exactly which account it came from.
Method 3: Direct Video Download via Network Sniffers
More technically sophisticated pirates use network interception tools — such as browser-based extensions that monitor network traffic — to identify and capture the underlying video stream URL while content plays. If your video is hosted without proper encryption, these tools can extract a direct download link that bypasses every surface-level protection your platform offers.
This method exploits a fundamental weakness in basic video hosting: the difference between a video that appears protected and one that is cryptographically protected. Platforms that use standard HLS streaming without DRM encryption are especially vulnerable, because the video segments themselves travel unencrypted to the browser, where they can be intercepted and reassembled into a complete downloadable file.
Method 4: Telegram & Closed-Group Redistribution
One of the most alarming developments in course piracy over the last three years has been the industrialization of content theft through private messaging platforms — most notably Telegram. Research has identified over 5,000 course piracy groups on Telegram alone, with more than 1,000 of those groups having memberships exceeding 10,000 individuals.
The operational model is straightforward and devastating: one person with legitimate access joins a group, uploads your course content, and it immediately becomes available to thousands of users who never paid. In India’s e-learning sector alone, this pattern of Telegram-based redistribution has been linked to an estimated ₹2,000 crore (~$240 million) in annual revenue losses.
The challenge for creators is that these groups operate in closed, invite-only environments that are difficult to monitor without specific tools designed to crawl private messaging platforms for unauthorized content.
Method 5: Re-uploading & Reselling on Third-Party Platforms
A significant portion of course piracy is not simply sharing — it is outright resale. Stolen course content regularly appears on black-market digital product sites, unauthorized marketplaces, and even mainstream platforms like YouTube, where full course modules are uploaded as “free” content.
Beyond the direct revenue loss, this form of piracy carries a particularly damaging secondary consequence: brand erosion. When your premium course is freely available elsewhere, it fundamentally undermines the perceived value of your content in the eyes of prospective students. Worse, it associates your intellectual property with platforms and contexts entirely outside your control.
Method 6: AI-Assisted Content Stripping
The newest and most rapidly evolving threat in the course piracy landscape is the use of artificial intelligence tools to process, repackage, and redistribute stolen content at scale. In 2025, AI-powered tools can strip identifying metadata, alter visual elements to defeat basic watermarks, generate derivative transcripts, and redistribute content in forms that are difficult for traditional detection systems to flag.
This is the front line of the current arms race between content thieves and protection technology. Staying ahead of AI-assisted piracy requires protection systems that operate at the DRM hardware level — where no amount of software-based manipulation can defeat the encryption — rather than relying on surface-level watermarks or metadata alone.
Is your course already exposed? Inkrypt Videos provides DRM-grade protection that closes all 6 of these theft vectors. Speak with our team today at 804 500 2905, email [email protected], or visit inkryptvideos.com to secure your content before the next leak.
How to Detect Course Piracy: Warning Signs You Cannot Ignore
Prevention begins before a breach occurs. But detection — knowing that your content is already in the wild — is equally critical, both for limiting ongoing damage and for building a legal case. These are the signals every course creator must actively monitor.
Suspicious Login & Access Patterns
Your course analytics are your first line of early warning. Simultaneous logins from geographically distant locations, an unusual number of active sessions from a single account, or a spike in video completion rates from users who enrolled without corresponding engagement activity — these are the behavioral fingerprints of credential sharing and unauthorized access.
Without an access monitoring system that flags these anomalies automatically, creators are entirely blind to this form of piracy as it unfolds in real time.
Dark Web & Telegram Monitoring
Manual monitoring is time-consuming but essential. Periodically searching your course name, your brand name, and specific module titles on Telegram, Reddit, torrent indexes, and digital marketplace forums can reveal whether your content is actively being distributed without authorization. Automated monitoring tools that continuously crawl these channels provide a more systematic approach.
Analytics Anomalies
When your video hosting analytics show play counts that significantly exceed your enrolled student count, when bandwidth consumption is disproportionate to active enrollments, or when referral traffic suddenly arrives from domains you do not recognize, these are data-level signals that your content may be playing somewhere unauthorized.
DMCA Strike Signals
In some cases, piracy announces itself. Receiving a complaint that someone is using your course materials, discovering a YouTube channel with your lesson videos, or finding your course title listed on a resale platform are clear indicators requiring immediate action.
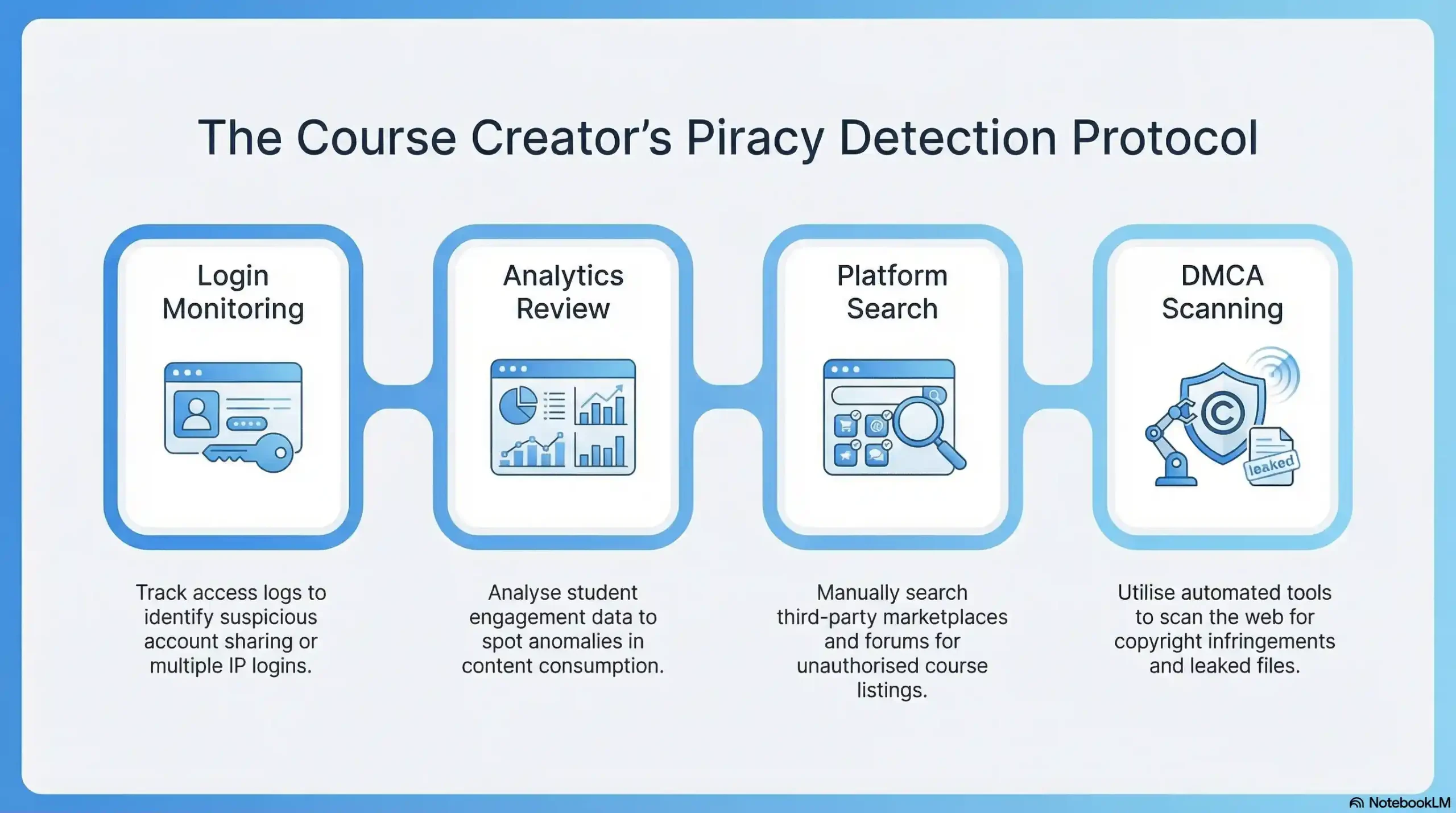
| Detection Signal | What It Means | Urgency Level | Action to Take |
|---|---|---|---|
| Simultaneous logins from multiple countries | Active credential sharing | 🔴 Immediate | Revoke session, force password reset, review access logs |
| Video plays exceeding enrollment count | Unauthorized external playback | 🔴 Immediate | Audit referral sources, activate signed URL restrictions |
| Course title found on Telegram/torrent | Active redistribution in progress | 🔴 Immediate | Document evidence, initiate DMCA, rotate encryption keys |
| Unknown referral domains in analytics | Unauthorized embedding | 🟠 Urgent | Activate domain restrictions, review hosting settings |
| Duplicate content appearing on YouTube | Re-upload piracy | 🟠 Urgent | File DMCA takedown, watermark forensics review |
| Slow enrollment despite high traffic | Potential free access circulating | 🟡 Monitor | Cross-reference with piracy platform searches |
The False Security Trap: Why Basic Protections Fail
One of the most costly mistakes course creators make is investing in protections that feel secure but offer no meaningful resistance against real piracy methods. Understanding what fails in practice is essential to understanding what genuine security actually requires.
Disabling right-click on a webpage prevents nothing. A user running a screen capture tool does not need to right-click anything. Hiding the video download button is equally cosmetic — the video stream is still traveling to the viewer’s device, and network interception tools capture it at that layer, not from a download button. Password protection alone means that anyone with the password — including anyone a legitimate student chooses to share it with — has unrestricted access.
Perhaps the most dangerous misconception is that standard HLS encryption (AES-128) provides comprehensive security. While it adds a layer above completely unprotected streaming, its static encryption keys are vulnerable to interception. Research indicates that 78% of piracy incidents can be traced back to encryption key leaks in systems that rely on basic AES-128 without dynamic key rotation. The gap between a system that looks secure and one that is cryptographically secure is where the majority of course theft occurs.
How to Prevent Course Piracy: The Professional Protection Stack
Effective course piracy prevention is not a single tool — it is a layered system where each layer compensates for the limitations of the others. This is the architecture that professional platforms use, and it is the standard every serious course creator should demand.
Layer 1: DRM Encrypted Video Streaming (Widevine)
Hardware-level Digital Rights Management is the foundational layer of any serious content protection strategy. Unlike software-based encryption, DRM systems such as Google Widevine — the same technology used by Netflix, Disney+, and Amazon Prime — bind decryption keys to specific devices at the hardware level. This means that even if a pirate captures the encrypted video stream, they cannot decrypt and play it on any unauthorized device.
Inkrypt Videos integrates Widevine DRM natively, bringing enterprise-grade encryption to course creators without requiring a technical team to implement it. Dynamic key rotation — changing encryption keys automatically every few minutes — further eliminates the window of vulnerability that static keys create.
Layer 2: Dynamic Video Watermarking
Dynamic watermarking embeds the viewer’s unique identifier — their email address, user ID, or IP address — invisibly and persistently into the video during playback. Unlike static watermarks that can be cropped or edited out, dynamic watermarks shift position, vary in opacity, and are woven into the video at the pixel level in ways that survive screen recording, re-encoding, and most AI-based removal attempts.
This layer serves two functions simultaneously: it deters piracy by making every viewer aware that their identity is embedded in the content they are watching, and it enables forensic attribution — if a leaked copy surfaces, the watermark identifies exactly which account it originated from, providing actionable evidence for legal action.
Layer 3: Secure Video Hosting with Domain Restrictions & Signed URLs
Domain-restricted video hosting ensures that your content can only be played on domains you have explicitly authorized. Embed your video on an unauthorized site, share the video URL in a Telegram group, or attempt to play it outside your course platform — the player simply will not load.
Signed URLs add a time-based access control layer: each playback request generates a unique, expiring URL that becomes invalid after a set period. There are no permanent links to steal, share, or reuse. Access exists only for the duration and context in which it was legitimately authorized.
Layer 4: Real-Time Access Monitoring & Anomaly Alerts
Automated monitoring transforms your analytics from a passive reporting tool into an active security system. When the same account logs in simultaneously from Berlin and São Paulo, the system flags it instantly. When a single session generates an abnormal number of video requests, an alert fires. Suspicious access tokens can be revoked in real time — without waiting for a weekly report to reveal the problem after thousands of unauthorized views have already occurred.
Layer 5: Global CDN Delivery Without Security Tradeoffs
A persistent misconception in content security is that protection comes at the cost of performance. Serious creators sometimes resist implementing DRM because they fear it will degrade the student experience with buffering, compatibility issues, or playback errors on older devices.
Inkrypt Videos delivers content through Amazon’s global CDN infrastructure, ensuring zero-buffering playback to audiences worldwide — while maintaining full DRM encryption at every point in the delivery chain. Universal device compatibility, including older hardware that many enterprise DRM solutions exclude, means creators never have to choose between protecting their content and serving their students.
Inkrypt Videos delivers all 5 layers of this protection stack in a single platform — with a 30-minute setup time. Reach our team directly at 804 500 2905 or [email protected]. We are based at 1528 W Sunset Ave, Springdale, Arizona 72764 and serve course creators and digital content businesses worldwide.
🏛️ Local Resources & Citations
1. U.S. Copyright Office — Digital Millennium Copyright Act (DMCA) (copyright.gov) The official U.S. government source for understanding your legal rights under the DMCA — visit here to file a formal takedown notice, access sample notice templates, and look up the designated DMCA agent for any platform hosting your stolen content.
2. U.S. Copyright Office — DMCA Section 512: Notice-and-Takedown Resources (copyright.gov) The Copyright Office’s dedicated Section 512 resource hub explains exactly how the notice-and-takedown system works, what qualifies as a legally effective takedown claim, and how online service providers must respond — essential reading before filing your first piracy complaint.
3. WIPO — World Intellectual Property Organization: Internet Treaties & Digital Copyright (wipo.int) As the United Nations agency overseeing global IP standards, WIPO administers the international treaties that govern anti-circumvention protections (including DRM legality) in 193+ countries — use this resource to understand your copyright protections when piracy occurs outside the United States.
4. NIST — Cybersecurity Framework & Cryptographic Standards (nist.gov) The U.S. National Institute of Standards and Technology publishes the official encryption standards and cybersecurity frameworks that underpin enterprise-grade DRM systems — use this to verify that any content protection platform you evaluate meets federally recognized security benchmarks.
What to Do When You Discover Your Course Has Been Pirated
Discovering active piracy of your content requires a composed, methodical response. Panic leads to incomplete action. Here is the immediate protocol:
Step 1 — Document Everything First. Before taking any action that might cause the infringing content to be removed or altered, capture screenshots with timestamps, record URLs, note platform names, and preserve any metadata visible on the pirated content. This documentation forms the foundation of any legal action.
Step 2 — File a DMCA Takedown Notice. For content hosted on platforms operating under U.S. jurisdiction, a properly filed DMCA notice requires the platform to remove infringing content promptly. Most major platforms — YouTube, Google, Udemy, Vimeo — have streamlined DMCA submission processes. For content hosted internationally, DMCA equivalents exist in most jurisdictions.
Step 3 — Revoke Compromised Access Immediately. If watermark forensics or access logs identify the account responsible for the leak, revoke that access token, invalidate their session, and disable their enrollment. Rotate your signed URL parameters and, if DRM key compromise is suspected, trigger an encryption key rotation cycle.
Step 4 — Upgrade Your Protection Before Re-Exposure. If your content was successfully pirated, your current protection level is insufficient. Implementing the full five-layer protection stack before your next launch or content update is non-negotiable. Every day your content remains protected only at a surface level is another day it is vulnerable.
Do not wait for the next incident. Inkrypt Videos is the Digital Guardian your premium content deserves — real security for real creators. Call us today at 804 500 2905 or start your protection at inkryptvideos.com.
Frequently Asked Questions
Course piracy is the unauthorized copying, downloading, redistribution, or resale of paid online course content without the creator’s permission. It directly reduces revenue by converting potential paying students into free users, erodes brand value when content appears on unauthorized platforms, and discourages creators from publishing their most valuable knowledge online.
The clearest warning signs that your course has been pirated include simultaneous logins from geographically impossible locations, video play counts that exceed your enrolled student numbers, your course title appearing in Telegram groups or torrent indexes, and unknown referral domains generating traffic in your analytics dashboard. Real-time access monitoring and automated anomaly alerts are the most reliable detection methods.
DRM (Digital Rights Management) encryption protects online courses by binding decryption keys to specific authorized devices at the hardware level, making it impossible to play content on unauthorized devices even if the video stream is intercepted. Unlike basic AES-128 encryption, enterprise-grade DRM systems such as Google Widevine — used by Netflix and Disney+ — rotate encryption keys dynamically, closing the key-leak vulnerability responsible for the majority of piracy incidents.
Yes — screen recording tools can bypass surface-level protections such as disabled right-click, hidden download buttons, and basic password access. The only effective countermeasure is dynamic video watermarking, which embeds the viewer’s unique identifier (email, user ID, or IP address) directly into every frame during playback. This ensures that even a screen-recorded copy can be forensically traced back to the specific account that leaked it.
Dynamic video watermarking is a security technique that invisibly embeds a viewer’s unique identifier — such as their email address or user ID — into the video during playback. Unlike static watermarks, dynamic watermarks shift position and vary in opacity, surviving screen recording and re-encoding. They deter piracy by making every viewer aware their identity is embedded in the content, and they enable forensic attribution when leaked copies are discovered.
If you discover your course has been pirated, take four immediate steps: first, document all evidence including URLs, screenshots, and timestamps before anything is removed; second, file a DMCA takedown notice with the hosting platform; third, revoke the compromised access token and rotate your encryption keys; fourth, upgrade your content protection to a full DRM and watermarking stack before re-exposing your content to new students.
The best platform for protecting online course videos from piracy is one that delivers a complete five-layer security stack: DRM encrypted video streaming (Widevine), dynamic video watermarking, domain-restricted secure hosting, signed expiring URLs, and real-time access anomaly monitoring. Inkrypt Videos provides all five layers with Amazon CDN-backed global delivery, 30-minute setup, and universal device compatibility — purpose-built for course creators and digital content businesses worldwide.
Course piracy occurs when unauthorized users access, download, or resell paid online course content via screen recording, bundles, or file-sharing sites.
Thieves buy access legally, then screen-record videos, bundle courses cheaply, or use software to bypass DRM and redistribute on spammy sites or torrents.
No method is 100% foolproof; determined pirates use screen recorders that capture DRM-protected streams, and content spreads quickly on forums and torrent sites.
Set up Google Alerts for course names/phrases, use tools like Brand24 for web monitoring, and manually search file-sharing sites and Reddit for leaks.
Apply visible/invisible watermarks, enable DRM encryption, limit concurrent logins, use streaming-only platforms, and register copyrights for legal takedowns.
Disclaimer:
This article is intended for educational and informational purposes only. It does not promote or endorse piracy in any form. All references to piracy methods are provided solely to help content creators understand potential risks and implement appropriate protection measures.

