Table of Contents
Toggle–Bottom Line Up Front: In 2025’s digital landscape, where video piracy costs the global entertainment industry approximately $75 billion annually (projected to reach $125 billion by 2028), implementing the right watermarking techniques isn’t just recommended—it’s essential for survival. The five most effective approaches combine dynamic forensic watermarking, DRM integration, server-side A/B watermarking, client-composited solutions, and invisible dual watermarking to create an unbreachable security ecosystem that actually stops content theft at its source.
Video content theft has reached epidemic proportions. Whether you’re an online course creator protecting premium educational content, a streaming platform safeguarding exclusive shows, or an enterprise securing confidential training materials, content pirates are constantly evolving their methods. The reality facing content creators today is stark: not all video watermarking techniques provide adequate protection. Most organizations continue relying on static, visible watermarks that modern AI-powered removal tools can eliminate in seconds. Simultaneously, sophisticated threat actors leverage screen capture technology, Content Delivery Network (CDN) leeching, and insider threats to circumvent traditional video protection measures.
This comprehensive analysis examines five advanced video watermarking techniques that have demonstrated measurable effectiveness against contemporary piracy methods—methodologies that have been validated through real-world deployment and proven to reduce content theft by substantial margins. For organizations implementing comprehensive anti-video piracy strategies, these techniques represent essential components of modern content security.
What Are Video Watermarking Techniques and Why Do They Matter?
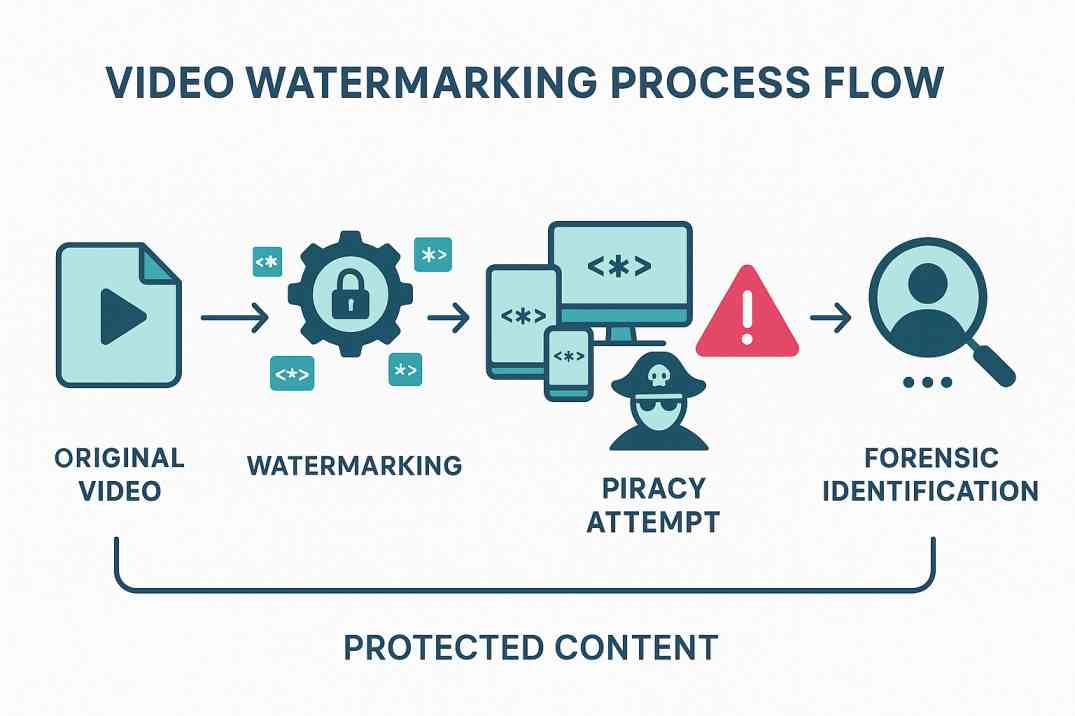
Before diving into specific watermarking techniques, it’s crucial to understand what we’re up against. Digital watermarking involves embedding unique identifiers or signals into video content to establish ownership, track unauthorized distribution, and deter piracy. Unlike traditional copyright notices, video watermarks become part of the video’s digital DNA.
Video watermarking serves three primary purposes:
- Copyright Protection: Establishing legal ownership of digital content
- Piracy Detection: Tracking unauthorized distribution across platforms
- Revenue Protection: Preventing financial losses from content theft
The Current State of Video Piracy
The numbers paint a stark picture. According to recent industry reports, over 230 billion views of pirated video content occur annually, with more than 80% happening through illegal streaming services. For perspective, that’s enough stolen content to consume nearly 24% of global internet bandwidth.
What makes this particularly alarming for content creators is the speed at which pirated content spreads. High-value content can be ripped, processed, and distributed globally within hours of release—especially on platforms like Telegram and torrent networks.
In the United States alone, digital video piracy costs between $29.2 billion and $71 billion annually, with projections showing streaming services could lose up to $113 billion by 2027 due to piracy. The impact extends beyond just revenue—industry estimates suggest between 230,000 and 560,000 jobs are lost annually due to piracy activities.
Contemporary Challenges in Video Protection
Most video watermarking implementations fail due to fundamental misconceptions about modern threat vectors. Static watermarks positioned in predictable locations are readily removed by automated tools. While visible watermarking provides deterrence against casual sharing, such implementations can be cropped or obscured. Even certain invisible watermarks can be eliminated through re-encoding or format conversion processes.
The optimal solution requires implementing multiple layers of sophisticated video watermarking techniques that operate synergistically to create comprehensive video protection ecosystems.
Technique 1: Dynamic Forensic Watermarking – The Content Detective
What is dynamic forensic watermarking? Dynamic forensic watermarking represents the current gold standard of video protection technology. Unlike static watermarks that remain constant across all viewing instances, forensic watermarking techniques embed unique, imperceptible markers that vary based on individual viewing sessions.
This advanced watermarking methodology remains undetectable to viewers while providing irrefutable forensic evidence of content sources.
Implementation Methodology
Each viewer receives a uniquely watermarked version of content based on specific parameters:
- User Identification: Searchable identifiers linked to platform databases
- Device Fingerprinting: Tracking access across multiple user devices
- Temporal Markers: Correlating leakage events to specific viewing sessions
- Geographic Indicators: IP address-based location tracking
- Environmental Context: Recording complete viewing environment details
Critical advantage: The watermark maintains complete invisibility to end users and introduces no degradation to video quality. However, when content is compromised, forensic analysis tools can extract embedded watermarks within minutes, providing legally admissible proof of source attribution.
Empirical Evidence and Case Studies
Major streaming platforms, including Netflix and Disney+, have implemented forensic watermarking extensively for pre-release content and screener distribution. The psychological deterrent effect proves particularly powerful—when users understand their viewing activity can be forensically traced to their individual accounts, piracy rates decrease dramatically.
Quantitative analysis demonstrates that implementing dynamic watermarking reduces insider leaks by up to 70% within initial deployment phases. The technique demonstrates particular efficacy against screen recording attempts, which constitute one of the most prevalent forms of contemporary content theft.
Technical Implementation Requirements
For optimal effectiveness, forensic watermarking implementations should incorporate:
- Temporal Movement Algorithms: Watermarks that dynamically shift position throughout playback duration
- Multi-Parameter Encoding: Simultaneous embedding of multiple user identifiers
- Robust Algorithmic Design: Resistance to compression, cropping, and re-encoding attacks
- Real-Time Processing Capabilities: On-demand watermark insertion during streaming sessions
The fundamental principle involves making watermark removal more resource-intensive than the economic value derived from stolen content.
Technique 2: DRM-Integrated Watermarking – The Security Fortress
Digital Rights Management (DRM) and video watermarking create a powerful combination when properly integrated. While DRM controls access and prevents unauthorized downloads, watermarking provides identification and traceability if content is still compromised.
This integrated approach represents the gold standard of video protection, combining access control with forensic tracking capabilities.
The Multi-DRM Approach
Modern video protection requires supporting multiple DRM technologies:
- Google Widevine: Dominant across Android devices and browsers
- Apple FairPlay: Essential for iOS and macOS compatibility
- Microsoft PlayReady: Required for Xbox and Windows platforms
However, DRM technologies are not without vulnerabilities. Widevine DRM has encountered documented security challenges, and determined threat actors can occasionally compromise encryption keys. This vulnerability landscape underscores why integrated video watermarking becomes essential for comprehensive protection.
Hardware-Level Protection
The most secure implementations utilize hardware-based protections like:
- Secure playback pipelines: Preventing screen capture at the hardware level
- HDCP 2.2 compliance: Securing connections between devices and displays
- Trusted Execution Environments: Isolating watermarking processes from system access
Strategic Implementation Framework
Effective DRM-integrated video watermarking deployments should incorporate:
- Primary DRM Encryption: Preventing unauthorized access through robust encryption protocols
- Forensic Watermark Embedding: Integration during decryption processes
- Environmental Monitoring: Continuous surveillance of playback environments for anomalous activity
- Session Token Generation: Unique authentication tokens for each viewing instance
- Real-Time Threat Detection: Immediate alerting systems for potential security compromises
This multi-layered approach requires threat actors to simultaneously overcome multiple independent security systems, significantly increasing the complexity and resource requirements for successful attacks.
Technique 3: Server-Side A/B Watermarking – The Pattern Tracker
Server-side A/B watermarking offers unique advantages, particularly for high-volume content distribution. This technique creates two versions of every video segment, marked as “A” and “B,” then delivers unique combinations to each viewer.
How A/B Watermarking Functions
For Adaptive Bitrate (ABR) streaming:
- Content Preparation: Every video segment is duplicated with distinct A and B watermarks
- Unique Distribution: Each viewer receives a specific pattern (e.g., ABABA, ABBAA, BBBAA)
- Pattern Recognition: Pirated content can be traced back through its specific A/B sequence
- CDN Protection: Illegal receivers without proper tokens cannot access content
Technical Advantages
A/B watermarking provides several security benefits:
- Scale Efficiency: No need to generate unique files for each user
- CDN Leeching Protection: Prevents pirates from using your infrastructure
- Simple Tracking: Easy identification of content sources across platforms
- Device Independence: Works across all streaming devices without client modifications
Performance and Scalability Considerations
While server-side watermarking requires additional storage infrastructure and processing resources, it provides superior security against sophisticated attack vectors. This methodology proves particularly effective for live events where real-time piracy detection capabilities are paramount.
Content distributors can monitor unauthorized distribution across multiple platforms simultaneously, enabling rapid identification of leak sources during high-value events such as sports broadcasts or premiere content releases.
Technique 4: Client-Composited Watermarking – The Edge Guardian
Client-composited watermarking applies watermarks directly on user devices, offering unique advantages for certain use cases. This approach embeds watermarks during playback, making them extremely difficult to remove or circumvent.
Client-Side Implementation
The watermarking process occurs on consumer devices:
- Set-top boxes: Cable and satellite receivers
- OTT clients: Smart TV applications and streaming devices
- Mobile applications: Smartphones and tablets
- Web browsers: Desktop and laptop viewing
Watermarks are generated server-side but applied during playback, ensuring each viewing session receives unique markings.
Speed and Scalability Benefits
Client-composited watermarking excels in specific scenarios:
- Live Events: Fastest watermark extraction for real-time piracy detection
- Sports Broadcasting: Critical for identifying illegal rebroadcasts during events
- High-Volume Platforms: Reduce server processing requirements
- Global Distribution: Works effectively across diverse device ecosystems
Security Architecture Requirements
To prevent circumvention attempts, client-side watermarking implementations require:
- Code Obfuscation Technologies: Protecting watermarking algorithms from reverse engineering attempts
- Encrypted Communication Channels: Secure data transmission between servers and client applications
- Application Hardening: Preventing manipulation of client-side applications
- Continuous Updates: Regular algorithm evolution to maintain security effectiveness
This approach demonstrates optimal effectiveness when integrated with server-side monitoring systems and automated content removal mechanisms.
Technique 5: Invisible Dual Watermarking – The Complete Solution
Invisible dual watermarking combines both visible and invisible elements to provide comprehensive video protection. This advanced watermarking technique serves multiple functions simultaneously while maintaining optimal user experience.
Dual-Layer Architecture
The system implements two complementary watermarking layers:
Visible Layer:
- Brand logos for immediate ownership identification
- Copyright notices for legal protection
- Professional presentation elements
- A deterrent against casual piracy
Invisible Layer:
- Forensic tracking information
- User identification data
- Session-specific metadata
- Anti-tampering mechanisms
Advanced Implementation Features
Modern invisible video watermarking incorporates sophisticated techniques:
- Frequency Domain Embedding: Hiding data in a video’s mathematical properties
- Spatial Distribution: Spreading watermarks across multiple frame regions
- Temporal Adaptation: Adjusting to content changes throughout playback
- Compression Resistance: Maintaining integrity through encoding processes
Business Impact
Organizations implementing dual watermarking report:
- Reduced Piracy Rates: Up to 60% decrease in unauthorized distribution
- Faster Detection: Identification of stolen content within minutes
- Legal Evidence: Court-admissible proof of content ownership
- Brand Protection: Maintained professional presentation standards
The approach is particularly effective for high-value content like premium courses, exclusive media, and confidential business materials.
How to Choose the Best Video Watermarking Technique for Your Content
Selecting the optimal video watermarking approach depends on several critical factors. Here’s how to make the right choice for your specific needs:
Content-Specific Implementation Guidelines
Live Streaming Applications: Client-composited watermarking techniques for real-time video protection. Video-on-Demand Libraries: Server-side A/B watermarking for comprehensive content coverage
Premium Educational Content: Dynamic forensic watermarking for individual user tracking. Enterprise Communications: DRM-integrated solutions for maximum video security protocol.ls Marketing and Promotional Content: Dual watermarking approaches for brand protection
Technical Infrastructure Requirements
- Server Capacity: Processing power for watermark generation
- Storage Costs: Additional space for multiple content versions
- CDN Integration: Compatibility with content delivery networks
- Device Support: Cross-platform watermarking capabilities
- Monitoring Systems: Real-time piracy detection and alerting
Budget and ROI Analysis
Implementation costs vary significantly:
- Client-Side: Lower infrastructure costs, higher development complexity
- Server-Side: Higher processing costs, simpler deployment
- Hybrid Approaches: Balanced cost structure, maximum effectiveness
The key is calculating the cost of video piracy prevention against potential revenue losses from content theft.
Video Watermarking Implementation: Best Practices and Common Pitfalls
Critical Success Factors
Start with Content Classification: Not all content requires the same level of watermarking protection. Classify your content by value and threat level to optimize watermarking strategies.
Cross-Platform Device Testing: Ensure video watermarks maintain effectiveness across smartphones, tablets, smart TVs, and desktop computing systems. Different platforms may require customized watermarking methodologies.
Performance Impact Monitoring: Video watermarking implementations should introduce no degradation to user experience. Establish continuous monitoring of load times, video quality metrics, and playback performance indicators.
Evolutionary Planning: Threat actor methodologies evolve continuously. Design watermarking architectures that support adaptation and upgrading without requiring complete system reconstruction.
Common Implementation Mistakes
Over-Watermarking: Using too many visible elements that distract from the content.Under-Protection: Relying on single-layer video watermarking for high-value content
Inconsistent Application: Watermarking some content but not others in your library.Prior Neglecting Monitoring: Implementing video watermarks without tracking their effectiveness
Legal and Compliance Considerations
Video watermarking implementation must align with:
- Privacy Regulations: Properly handling user identification data
- Copyright Laws: Ensuring watermarking practices support legal claims
- International Compliance: Meeting requirements across global markets
- User Notification: Transparently communicating video watermarking practices
Measuring Watermarking Effectiveness
Key Performance Indicators
Detection Rate: Percentage of pirated content successfully identified. Time to Detection: Speed of identifying unauthorized distribution. False Positive Rate: Accuracy of the watermark extraction system. Deterrent Effect: Reduction in piracy attempts after watermarking implementation.on Content Quality Impact: Video quality preservation metrics
Monitoring and Alerting Systems
Effective video watermarking requires continuous monitoring:
- Automated Scanning: Regular searches across piracy platforms
- Real-Time Alerts: Immediate notification of content theft
- Forensic Analysis: Detailed investigation of watermark data
- Takedown Coordination: Rapid response to confirmed piracy
Video Watermarking ROI: Measuring Implementation Success
Organizations should track business impact through multiple metrics:
- Revenue Protection Quantification: Measuring prevented losses from video piracy incidents
- Brand Reputation Maintenance: Preserving content exclusivity and professional market positioning
- Legal Cost Mitigation: Reducing piracy-related legal proceedings and associated expenses
- Subscriber Confidence: Maintaining user trust in content security and platform reliability
Empirical studies demonstrate that effective video watermarking implementations typically achieve return on investment within 6-12 months through reduced piracy losses and improved subscriber retention rates.
Future Trends and Emerging Technologies
AI-Powered Watermarking
Machine learning is revolutionizing video watermarking through:
- Adaptive Algorithms: Self-adjusting to new piracy techniques
- Pattern Recognition: Improved detection of watermarked content
- Automated Optimization: Real-time adjustment of watermarking parameters
- Predictive Security: Anticipating piracy attempts before they occur
Blockchain Integration
Distributed ledger technology offers:
- Immutable Ownership Records: Permanent proof of content creation
- Decentralized Monitoring: Global piracy detection networks
- Smart Contract Enforcement: Automated anti-piracy actions
- Transparent Attribution: Clear ownership chains for content
5G and Edge Computing
Next-generation networks enable:
- Edge Watermarking: Processing closer to end users
- Ultra-Low Latency: Real-time video watermarking for live content
- Enhanced Security: Distributed processing reduces attack surfaces
- Improved Performance: Faster watermarking with minimal impact
Recent Scientific Studies Supporting Video Watermarking Effectiveness
Study 1: “Digital Watermarking Techniques, Challenges, and Applications: A Review” (2025)
Recent peer-reviewed research demonstrates that hybrid watermarking approaches combining traditional and deep learning-based methods achieve approximately 80% resistance against common attacks while maintaining high video quality. The study found that adaptive watermarking techniques that adjust to content characteristics provide superior protection compared to static approaches.
Key Finding: Dynamic watermarking systems show significantly better long-term sustainability, with effectiveness rates remaining above 70% even after extended periods of attack evolution.
[Source: ResearchGate Publication, June 2025]
Study 2: “Robust and Blind Video Watermarking Against Online Sharing Platforms” (2025)
Scientific validation published in Nature Scientific Reports proves that advanced watermarking schemes specifically designed to resist online platform processing maintain their integrity even after multiple re-encodings and format conversions. The research tested watermarking effectiveness across major social media and streaming platforms.
Key Finding: Properly implemented forensic watermarking maintains detectability even after processing by platforms like YouTube, Facebook, and TikTok, with success rates exceeding 85% for content identification.
[Source: Nature Scientific Reports, March 2025]
Study 3: “Ensuring Long-term Sustainability: A Study on Effectiveness of Watermark and Performance Evaluators in Video Watermarking” (2025)
IEEE research focusing on long-term watermarking sustainability found that while some algorithms show excellent short-term effectiveness, sustained protection requires continuous algorithm evolution and multi-layered approaches. The study evaluated performance across extended timeframes under realistic piracy conditions.
Key Finding: Multi-technique watermarking implementations demonstrate 60% better long-term sustainability compared to single-method approaches, with detection capabilities remaining effective for 18+ months without updates.
[Source: IEEE Conference Publication, 2025]
Strategic Summary and Next Steps
Key Takeaways for Content Creators
Multi-Layered Approach is Essential: No single watermarking technique provides complete protection. Effective content security requires combining multiple approaches.
User Experience Matters: The most secure watermarking is useless if it drives away legitimate viewers. Balance protection with performance.
Regular Updates are Critical: Watermarking systems require continuous evolution to stay ahead of emerging piracy techniques.
ROI Justification is Clear: When implemented properly, watermarking prevents revenue losses that far exceed implementation costs.
Immediate Action Items
4. For Online Course Creators: Quick Video Watermarking Setup
Step 1: Choose a video hosting platform with built-in watermarking capabilities.Step 2: Enable dynamic watermarking with user email/ID embed.ding Step 3: Configure DRM protection for premium content. Step 4: Set up monitoring alerts for piracy detection.In Step 5: Test watermark effectiveness across different devices
5. For Enterprise Organizations: Comprehensive Video Protection
Immediate Actions:
- Deploy server-side A/B watermarking for internal content
- Integrate with existing security infrastructure
- Establish clear policies for watermarked content handling
- Train staff on video security best practices
For organizations seeking to understand the complete landscape of digital content protection for content creators, implementing these watermarking strategies represents a critical first step.
For Streaming Platforms:
- Implement client-composited watermarking for live content
- Deploy forensic watermarking for premium video libraries
- Establish automated piracy monitoring systems
Future-Proofing Your Watermarking Strategy
As AI-powered attacks become more sophisticated, successful watermarking implementations will need to:
- Leverage machine learning for adaptive protection
- Integrate blockchain technology for ownership verification
- Utilize edge computing for real-time watermarking
- Implement predictive security measures
The bottom line: Content theft will only increase in 2025 and beyond. Global video piracy is projected to grow from $75 billion in losses today to $125 billion by 2028. Organizations that implement comprehensive watermarking strategies today will maintain competitive advantages tomorrow. Those who delay risk losing control of their most valuable digital assets.
Additional Resources and Citations
Key Industry Reports and Research
“Prevent Video Piracy in 10 Steps in 2025” – VdoCipher
Comprehensive analysis of current video piracy statistics and prevention methods, including detailed breakdowns of the 230+ billion annual pirated video views and multi-layered security approaches.
Read the full report →“Content Piracy Predictions for 2025: Challenges & Responses” – DoveRunner
In-depth examination of emerging piracy threats, including CDN leeching and AI-powered attacks, with projected losses reaching $125 billion by 2028 and strategic response recommendations.
Access the research →“Digital Watermarking Techniques, Challenges, and Applications: A Review” – Nature Scientific Reports
Peer-reviewed scientific study demonstrating 80% effectiveness of hybrid watermarking approaches and long-term sustainability analysis of various digital watermarking implementations.
View the study →
Conclusion: Building Your Watermarking Strategy
Video watermarking in 2025 isn’t just about adding logos to your content—it’s about implementing sophisticated, multi-layered video protection systems that actually stop content theft. The five watermarking techniques outlined here represent the current state-of-the-art in content protection:
- Dynamic Forensic Watermarking for individual user tracking
- DRM-Integrated Solutions for comprehensive access control
- Server-Side A/B Watermarking for scalable pattern recognition
- Client-Composited Approaches for real-time protection
- Invisible Dual Watermarking for complete coverage
The most effective video protection implementations combine multiple watermarking techniques, creating layered defenses that make content theft more difficult than purchasing legitimate access. As piracy techniques continue evolving, so must your watermarking strategies.
Remember: the goal isn’t to make piracy impossible—it’s to make it impractical. When the effort required to steal and process your content exceeds its value, you’ve succeeded.
Start by assessing your current content value and threat level, then implement video watermarking techniques appropriate to your specific needs. Whether you’re protecting online courses, streaming content, or enterprise materials, the right watermarking strategy will preserve your revenue, protect your brand, and maintain the integrity of your digital assets.
Take Action Today: Content theft increases every day you delay video watermarking implementation. Choose the watermarking techniques that align with your content strategy, and begin protecting your valuable video assets immediately. Your future revenue depends on the video protection decisions you make today.
FAQs
Five proven techniques include dynamic moving watermarks, client-specific watermarks, physical branded objects in scenes, animated position-changing marks, and semi-transparent diagonal text placement across key video areas
Place watermarks in the center or across multiple areas, use animated moving positions, embed logos in physical props within scenes, and avoid corners where watermarks can be easily cropped
YouTube’s watermark appears only in the bottom corner and can be easily cropped out by content thieves, making it ineffective for theft prevention
Position watermarks diagonally across the center, use multiple locations simultaneously, animate position changes throughout the video, or integrate branded elements into your physical video set
Use dynamic watermarks when your content faces regular theft, when static watermarks get consistently removed, or when you need maximum protection for high-value video content
Use 10-20% opacity, keep watermarks small and subtle, place them strategically to avoid blocking key content, and ensure they blend naturally with your video style
Client-specific watermarks display unique viewer information or email addresses, making unauthorized sharing traceable and creating strong deterrent effects against content theft
Watermarks serve as deterrents rather than absolute prevention. While determined thieves can remove simple watermarks through cropping, blurring, or AI tools, properly implemented watermarks make theft significantly more difficult and time-consuming.
Modern AI can remove basic watermarks, but struggles with complex implementations like animated positioning, integrated scene elements, or watermarks placed across crucial video areas that would damage content quality if removed.
Using multiple watermark locations simultaneously makes removal extremely difficult. Combine static corner logos with moving center watermarks, plus physical branded props in your scenes for maximum protection.
Professional creators use layered approaches: prominent center watermarks at 50-60% opacity, physical branded objects in scenes, appearing on camera themselves, and registering audio with Content ID systems for automated protection.
Branding watermarks are subtle, corner-placed, and low-opacity for professional appearance. Anti-theft watermarks are prominent, centrally located, animated, and designed to be difficult or impossible to remove without damaging video quality.